REhints
4.2K posts
REhints
@REhints
sharing reverse engineering knowledge


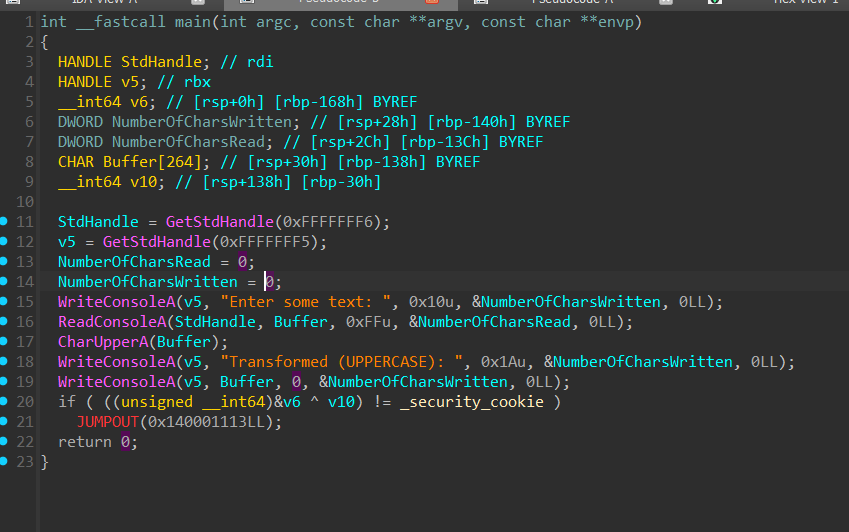
In the last couple months, I have replaced so many scripts with prompts like "use idac to perform class recovery, rename variables and functions, set prototypes, make and apply types to make the decompilation output look like the original source" github.com/trailofbits/id…


For the past 2 months, XBOW has been testing Mythos Preview under embargo as part of a select early-access group. Today, we can finally share what we found. The headline: Mythos Preview is a major advance. It is substantially better than prior models at finding vulnerability candidates, especially when source code is available. But it’s not perfect. We surfaced issues with exploit validation, judgment, and efficiency. Our full write-up covers where Mythos Preview shines, where it still needs support, and what we think this means for the future of offensive security: bit.ly/42zQl98

Our cyber range results illustrate this step-up. Since our first Mythos evaluation, we received access to a newer Mythos Preview checkpoint. On a 32-step corporate network attack we estimate takes a human expert ~20 hours, this checkpoint completes the full attack in 6 /10 attempts.

Early this week, @brucedang and I had a meeting at Apple Park in Cupertino. While there, we also shared with Apple our latest vulnerability research report: the first public macOS kernel memory corruption exploit on M5 silicon, surviving MIE. It was laser printed, in honor of our hacker friends. We wanted to report it in person, instead of getting buried in the submission flood that some unfortunate Pwn2Own participants just experienced. Most respected hackers avoid human interaction whenever possible, so this physical strategy may give us a slight edge in the eternal race for five minutes of fame and glory on Twitter. This is the story of the exploit and our field trip. Full technical details will be shared after Apple fixes the vulnerabilities and attack path. Hopefully it won’t take our beloved company too long. We only budgeted one year of domain registration fees for this attack. This is our strongest research yet, led by @justdionysus, @blacktop__ and @brucedang. It is really dope. Full story: blog.calif.io/p/first-public…

Confirmed! @chompie1337 of IBM X-Force Offensive Research (XOR) used a race condition to escalate privileges on Red Hat Enterprise Linux for Workstations, earning $20,000 and 2 Master of Pwn points. #Pwn2Own #P2OBerlin



We're likely 1st to publicly exploit crypto: af_alg as a new attack surface in kernelCTF. Our members @n0psledbyte & @st424204 started poking it in Sep 2025, finding a 0-day container escape unnoticed since 2011. @AnthropicAI @OpenAI: interested in collaborations? We are all ears





Our 2026 agenda is live! 🔗 offensivecon.org/agenda












CVE-2026-23870, CVE-2026-44575, CVE-2026-44579, CVE-2026-44574, CVE-2026-44578, CVE-2026-44573, CVE-2026-44581, CVE-2026-44580, CVE-2026-44577, CVE-2026-44576, CVE-2026-44582, CVE-2026-44572 github.com/dwisiswant0/ne…