Vishnuuuuu
793 posts



I earned $16,400 for my submission on @bugcrowd bugcrowd.com/h/defmax #ItTakesACrowd
Human in the loop is the way forward.
English
Vishnuuuuu retweetledi

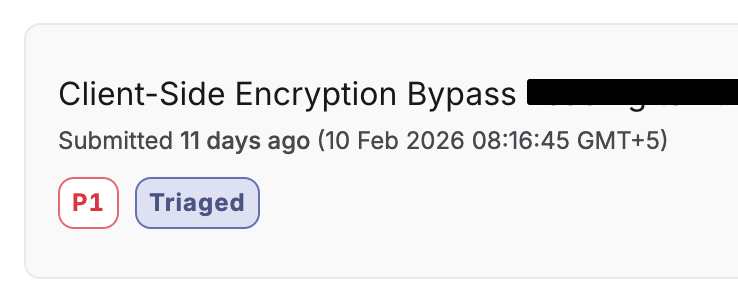
Critical: Client-Side Encryption Collapse
site.com
↓
some_javascript.js
↓
Line no 80519 → encObj + base64 key
↓
atob(val) → "Encoded_Password"
↓
CryptoJS.AES.decrypt(encObj, passphrase)
↓
55 configuration properties → 107 operational secrets exposed
→ Azure AD client_secret → OAuth client_credentials flow
→ RSA public keys → Forge encrypted /enc/ API requests
→ HMAC key → Backend-accepted payload signing
→ Direct Line token → Production chatbot access
→ Monitoring / RUM keys → Telemetry manipulation
→ Auth0 + reCAPTCHA config → Auth flow manipulation
→ 31+ encrypted authentication endpoints mapped
↓
Use extracted Azure AD credentials
↓
Request token from Microsoft OAuth endpoint (client_credentials)
↓
Receive valid JWT with high-privilege role (e.g., AllAccess)
↓
“Super token” accepted by backend across protected API routes
(No user interaction required, role-based authorization granted)
↓
All sensitive authentication and account endpoints
were wrapped in client-side hybrid encryption
→ Every request payload encrypted in browser
→ AES-256-CBC used for body encryption
→ RSA-OAEP used to wrap per-request AES key
→ Server accepts any request that decrypts successfully
→ Decryption success treated as implicit authorization
↓
Reverse-engineer encryption module (@**6246)
→ Algorithm: AES-256-CBC + RSA-OAEP (SHA-512)
→ Random 32-byte AES key per request
→ IV derived client-side
→ AES key wrapped with embedded RSA public key (promocode_pem)
→ Final format: { "key": base64(RSA_key), "body": hex(AES_ciphertext) }
↓
Hook JSON.stringify + XMLHttpRequest
↓
Capture plaintext BEFORE encryption (credentials, OTPs, tokens)
Capture encrypted wrapper AFTER encryption
Capture correlated server responses
↓
Analyze MFA implementation
↓
IP-based rate limiting only (lockout resets on IP change)
OTP expiration not strictly enforced server-side
Encrypted payload fields trusted after decryption
↓
Mass takeover method
↓
1. Trigger MFA or password reset
2. Rotate IP to bypass rate limiting
3. Reuse or brute-force OTP under weak enforcement
4. Complete password reset flow
5. Authenticate as victim
6. Capture decrypted OTP and auth tokens via runtime hook
7. Reuse valid 2FA tokens for subsequent authenticated requests
↓
Full attack chain achieved:
→ Extract secrets from client bundle
→ Generate high-privilege JWT (“super token”)
→ Read any plaintext request (credentials, PII, tokens)
→ Forge any encrypted request the server will accept
→ Bypass MFA protections via IP rotation
→ Reset victim passwords
→ Decrypt authentication flows in runtime
→ Mass account takeover
English
Vishnuuuuu retweetledi
Vishnuuuuu retweetledi

I'm on the lookout for a sales intern for @osmsec_xyz
The Sales Intern will support the business development and consulting teams by assisting in selling cybersecurity services, including penetration testing, security audits, and partner security products.
If this sounds fun, apply here: forms.gle/L8sohmugrZ3sao…

English
Vishnuuuuu retweetledi

We are looking for a Sales Engineer - Intern to support our B2B sales for cybersecurity services, including penetration testing, security audits, and partner security products.
Apply here: forms.gle/fJ94D5hVrS6d8h…

English
Vishnuuuuu retweetledi
Vishnuuuuu retweetledi

Huge shoutout to @TweetsFromPanda from @Hackerware_io for cooking up this awesome badge for @BSidesVizag, proudly sponsored by @hacktronix_in! 🔥 #BadgeLife
GIF
English
Vishnuuuuu retweetledi

Grateful to the amazing @BSidesVizag team for the opportunity to speak at #BsidesVizag2025! 🙌
Had a great time sharing my talk: “Bugs, Bounties & Breakthroughs” 🐛💻🚀
Slides here:
github.com/0xdln1/bsidesv…
English
Vishnuuuuu retweetledi

Glad to be a part of bug bounty panel at @BSidesVizag
It was great sharing the stage with
Surya Subash, Laxmi Narayana @0xdln, Charan, Dhawal.
A big thanks to @deathflash_xyz and their entire team for organizing it so well. Wishing you all the best for future editions.


English
Vishnuuuuu retweetledi

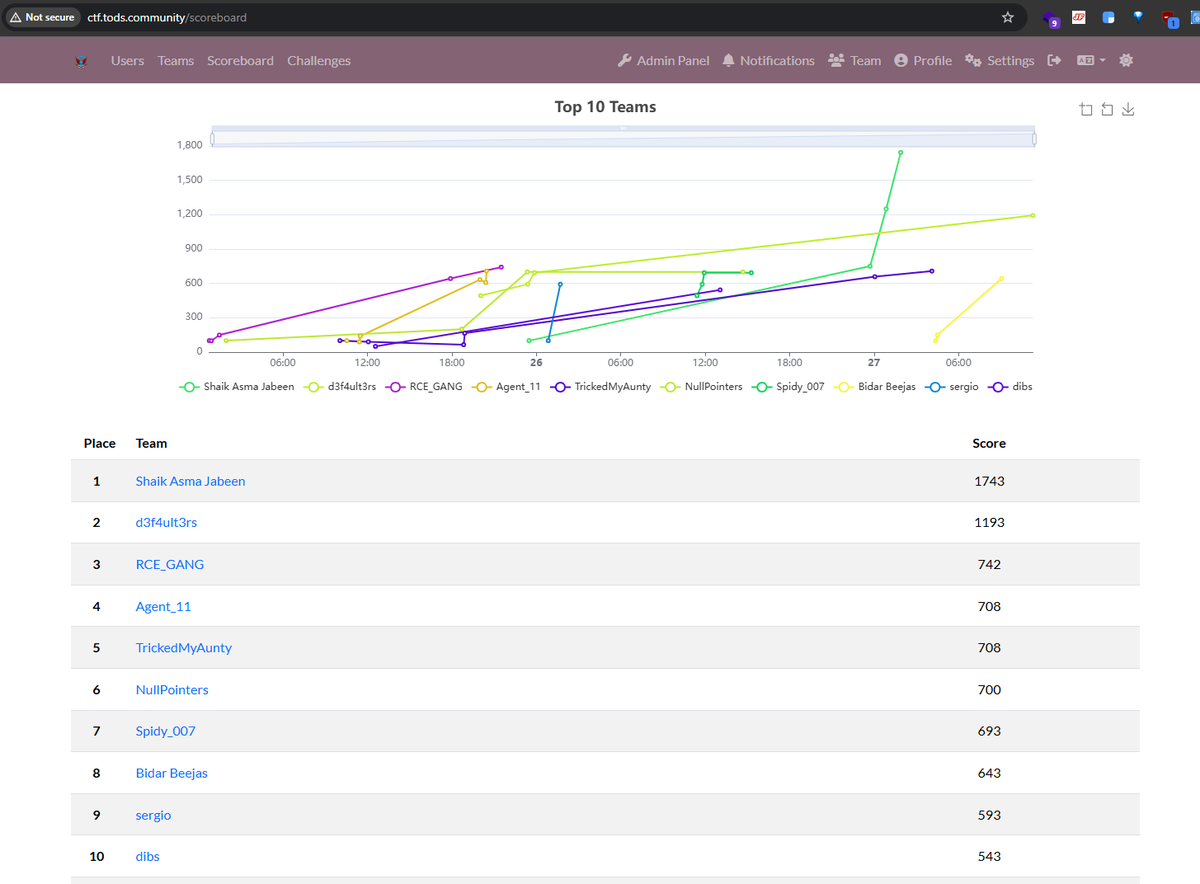
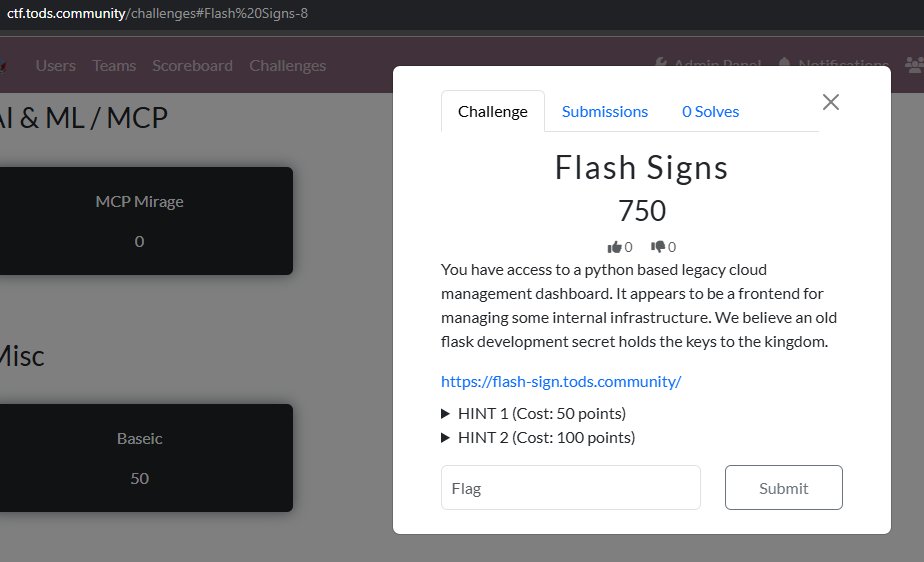
New CTF challenge just dropped — and it’s Tight, Tight, TIGHT! 💥
Energy is insane, scoreboard is shifting every hour.
If you love the feeling of breaking something that was designed to stop you — this one is for you.
🔗 ctf.tods.community
⚔️ Hack. Learn. Adapt. Win.
#tods

English

Hey everyone 👋
I’m thrilled to announce that I’ll be giving a talk at @BSidesVizag
If you want to know more about my journey, catch me at BSides Vizag, would love to connect and chat.
Use the code BOUNTIES for a special discount 🎟️
#BSidesVizag #BugBounty
English

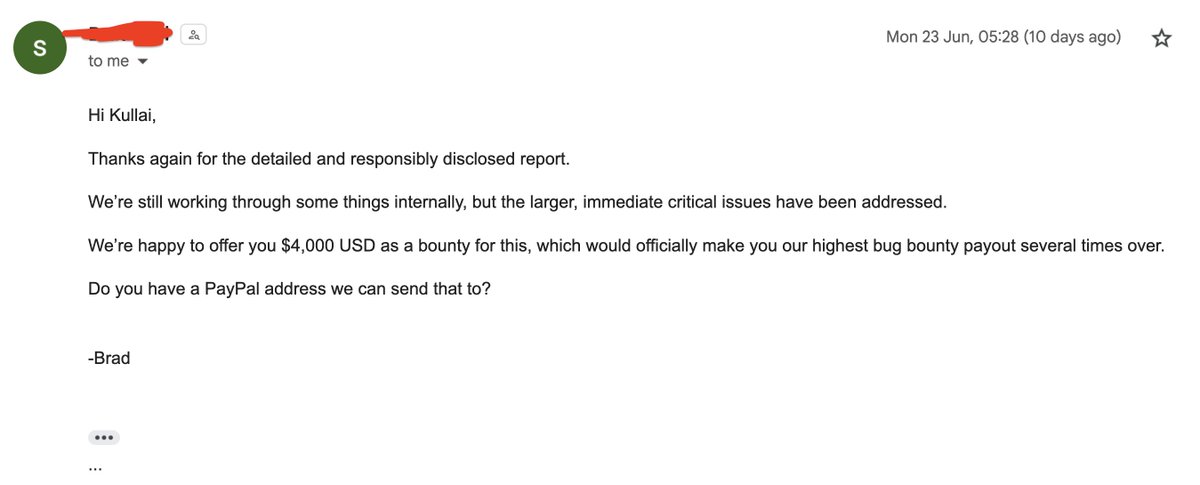
$4,000 - Github Pat Token Leak Leads to CRUD permissions
$1,000 - Auth Bypass
$500 - Privilege Escalation
$100 + $100 + $100 = Information Disclosure
$5,800 in June :)
$110 worth Swag from @posthog
Crossed 750 on @Hacker0x01 Finally 🙌
#hackerone #BugBounty #security



English
Vishnuuuuu retweetledi

Hello everyone ♥
a little bit write-up of #bugbountytip #bugbountytips I am going to write here .....
Title:
getting unauthorized access on 3rd party's/workspaces & and building your checklist for quickly locating bugs there via massive recon
we know that its helpful to look for google
groups/docs/etc..
Slack as well just like when the amazing @h4x0r_dz shared days ago ..
Use google dork "site:join.slack.com"
so I was not in a good mode the last months to doing Google Dorks, so what I did was build a checklist ready for me & very huge one
for EX:
groups.google.com
docs.google.com
join.slack.com
and here is just an example you can add more similar workspaces for your checklist
thin I extracted all internet endpoints and as example here join[.]slack[.]com
otx.alienvault.com/api/v1/indicat…
virustotal.com/vtapi/v2/domai…
web.archive.org/cdx/search/cdx…
you can use the ready tools to do it such as waymore
important note: you have to keep your checklist updated every week
and from here I just keep looking for the company name or domain name to see if there's anything connected
and mostly the company name or domain name in the URL it self EX: tesla
join.slack.com/t/Tesla-Intern…
Ex For Bugs found:
1 unauthorized access to the workspaces
(PII | Information disclose)
2 account takeover as Ex: valid signup employee link
3 account takeover as Ex: valid reset password employee link
now about Slack, as an example if you found an invitation link for tesla
Tesla join.slack.com/t/Tesla-Intern… and that link was not valid, don't stop here
it will redirect for Ex:
tesla-internal[.]slack[.]com
here back and start looking manually for endpoints of this subdomain as well EX:
web.archive.org/cdx/search/cdx…
now there are a lot of 3rd party's/workspaces I just shared here
slack & Google Docs/groups
What I wrote is a bit long and annoying to some, so I apologize. I hope, as usual, that this will be useful to all who follow me here.
#Bugounty
don't forget to retweet if you like it ♥♥♥


English
Vishnuuuuu retweetledi

I can see your pain (new bug hunters), I can see that it’s really hard to find bugs. I know some of you are working for years but didn’t succeed like the way you should be, I just want to let all of you know who are suffering, I am with you guys, I believe in you guys, I know no one believes in you, People call you a failure, Lets convert this pain into something big something worthy ❤️🩹.
English

Yay, I was awarded a $2,000 bounty on @Hacker0x01! hackerone.com/kullai
Full customers pII disclosed!!
#TogetherWeHitHarder #hackerone #bugbounty

English




