sec_leabhart
10 posts

sec_leabhart
@sec_leabhart
I do cybersecurity or something like that sometimes. Main acct is @leabhart.
Katılım Temmuz 2024
209 Takip Edilen5 Takipçiler


🚨 BREAKING
ShinyHunters claims to have accessed internal systems linked to Anthropic’s Mythos model — sharing screenshots of:
User management panels
AI experiment dashboards
Model performance & cost analytics
⚠️ At this stage, authenticity is unverified — but if confirmed, this would be a major escalation:
AI models designed to find vulnerabilities… becoming targets themselves.
This isn’t just a breach story.
It’s a preview of the next cyber battleground: AI infrastructure.
More to come.
#CyberSecurity #AI #DataBreach #ShinyHunters #Infosec #DDW




English

El cuento fue este:
-Un usuario estaba analizando (reverse-engineering) su propia aspiradora Roborock con ayuda de Claude AI y descubrió una API no documentada en la nube de la marca.
-Por un fallo de diseño en esa API, podía interactuar con prácticamente cualquier otra #Roborock conectada a la misma plataforma en todo el mundo, entonces logró acceso remoto a:
--Planos/mapa completos del suelo de las casas
--Imágenes y vídeo en directo de las cámaras (de los modelos que las tienen)
--Posibilidad de moverlas, encenderlas, etc.
-En pocas palabras, consiguió controlar accidentalmente más de 6.700 aspiradoras de todo el mundo mientras investigaba su propio dispositivo.
El usuario lo reportó a Roborock el 24/02/2026, y la empresa corrió a parchar el fallo para cerrar el acceso cruzado no autorizado. Como debe ser!
Es un caso de vulnerabilidad en dispositivos IoT.
Eso me recuerda q el otro día vi una wifi de una lavadora...🤔
elhacker.NET@elhackernet
Usuario toma el control accidental de más de 6.700 robots aspiradores blog.elhacker.net/2026/02/usuari…
Español

@vxunderground FWIW CrowdStrike had csa-251248 on October 30 with same IOCs as in that blog.
English

Rapid7 did a write-up on the Notepad++ compromise. Rapid7 released the paper fast af boi
How?
1. They sat on it
or...
2. Called in all the malware analysis schizos for lock the fuck in time
tldr ya prolly China lol
rapid7.com/blog/post/tr-c…
English

@jamieantisocial i really appreciate when you annotate articles like this. i can't even count how many times i skipped reading an article because i didn't think i'd find it interesting/relevant but then i see your tweet and realize i'm missing out and should read it after all. :-)
English

fresh take on old tradecraft.
lolbas-project.github.io/lolbas/OtherMS…
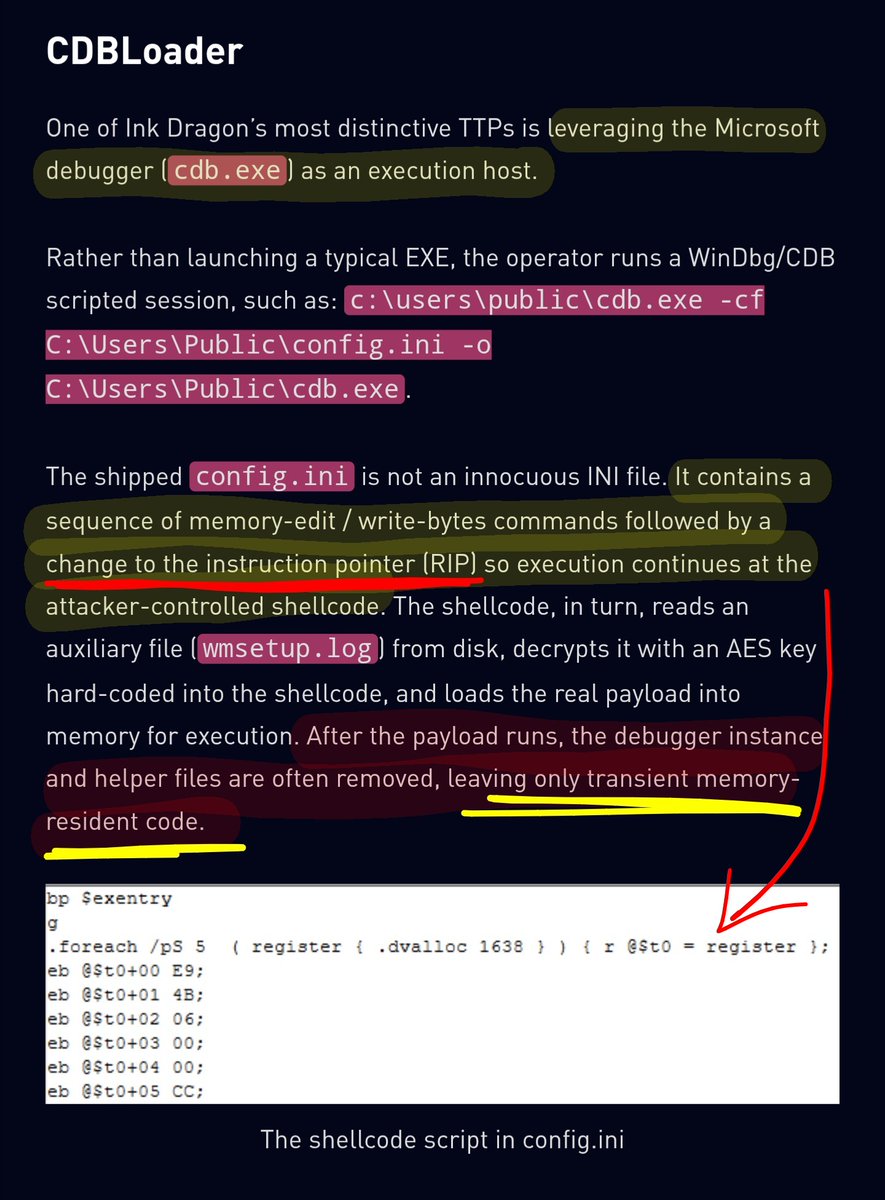
Check Point Research@_CPResearch_
China-linked #InkDragon expands into Europe, building a distributed relay network by weaponizing compromised servers with a custom #ShadowPad IIS listener alongside new TTPs and an evolved FinalDraft.research.checkpoint.com/2025/ink-drago…
English
sec_leabhart retweetledi

Tired of "reacting" to CVE-2025-55182? Come to SecDSM tonight! Doors open at 18:00 with free pizza and drinks. There will be a talk on monitoring networks for malicious traffic followed by "show & tell." Deets at secdsm.org.
English
sec_leabhart retweetledi
sec_leabhart retweetledi

New Blog! Top 10 Cyber Threats of 2024
Overall, this year was full of mega breaches, government hacking campaigns, massive ransomware attacks, disruptive ICS attacks, and global technology failures
🔗 blog.bushidotoken.net/2024/12/top-10…
#cybercrime #infosec #malware #cybersecurity

English