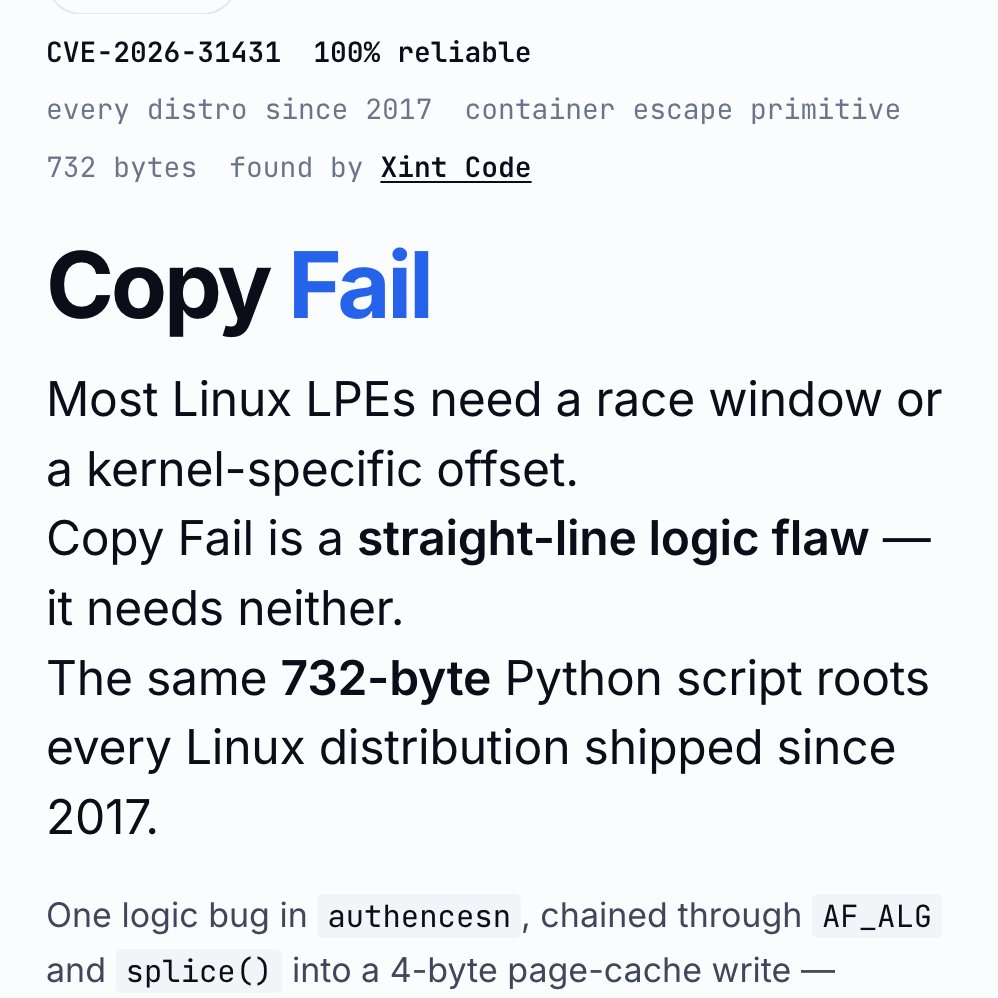
Sabitlenmiş Tweet
「進研ゼミ小学講座」で配信中の SF ドラマ『情報発信局「わくわく! 地球調査隊」』についての記事が公開されました!
私が開発している Furigana Studio を字幕制作に採用したエピソードにも触れていただきました。 #進研ゼミ #小学講座
VIDEO SALON編集部(ビデオサロン)@videosalon
【レポート】VFXを活かした短編シリーズの事例 ストーリー仕立てで魅せるSFドラマ制作 #SFドラマ #VFX #ショートドラマ videosalon.jp/report/wakuwak…
日本語