Sabitlenmiş Tweet

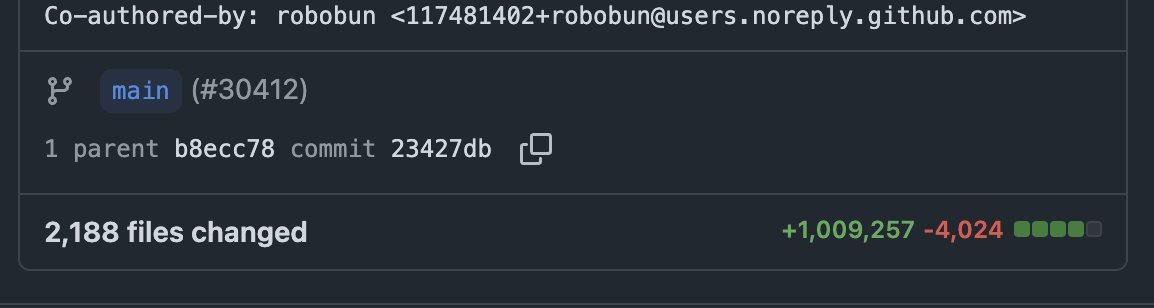
I build AI agents. 🔧 dodo — coding agent in your terminal. Local-first, sandboxed, model-agnostic. 🤖 ctxant — runs in your real Chrome via Telegram. No re-auth, no shadow profile. Posting what I learn building them. chamsbouzaiene.function.io/dodo/ ctxant.com
English