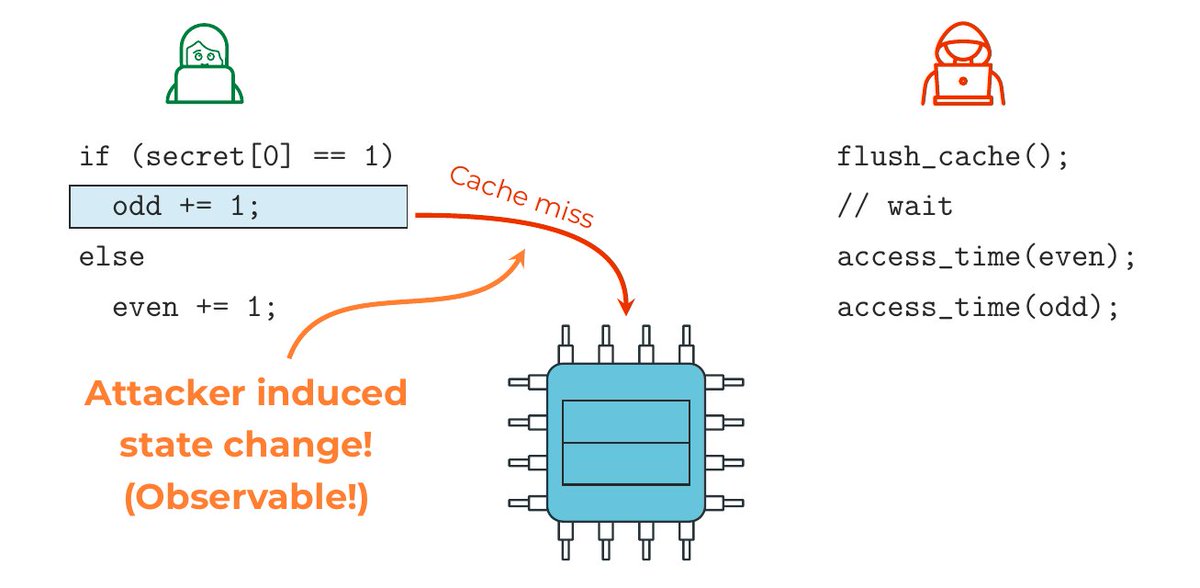
More Info + Exploits: stackwarpattack.com
AMD's Fix: amd.com/en/resources/p…
English
Daniel Weber
162 posts

@weber_daniel
Microarchitectural Security | PhD Student @cispa | Stealing Flags for @saarsec







I defended my PhD with distinction at @tugraz last friday! 🎉 Thank you to all the friends and folks who made this journey unforgettable. Special shoutout to @lavados, who went above and beyond by designing a game based on a "beer"-idea: Werewolves in the context of academia 🐺🎓

Faulty instructions in Alibaba's T-Head C910 RISC-V CPUs blow away all security dlvr.it/TBd09l