
Slava S.
349 posts


Slava S.
@slvDev
building tools and shipping too many things at once




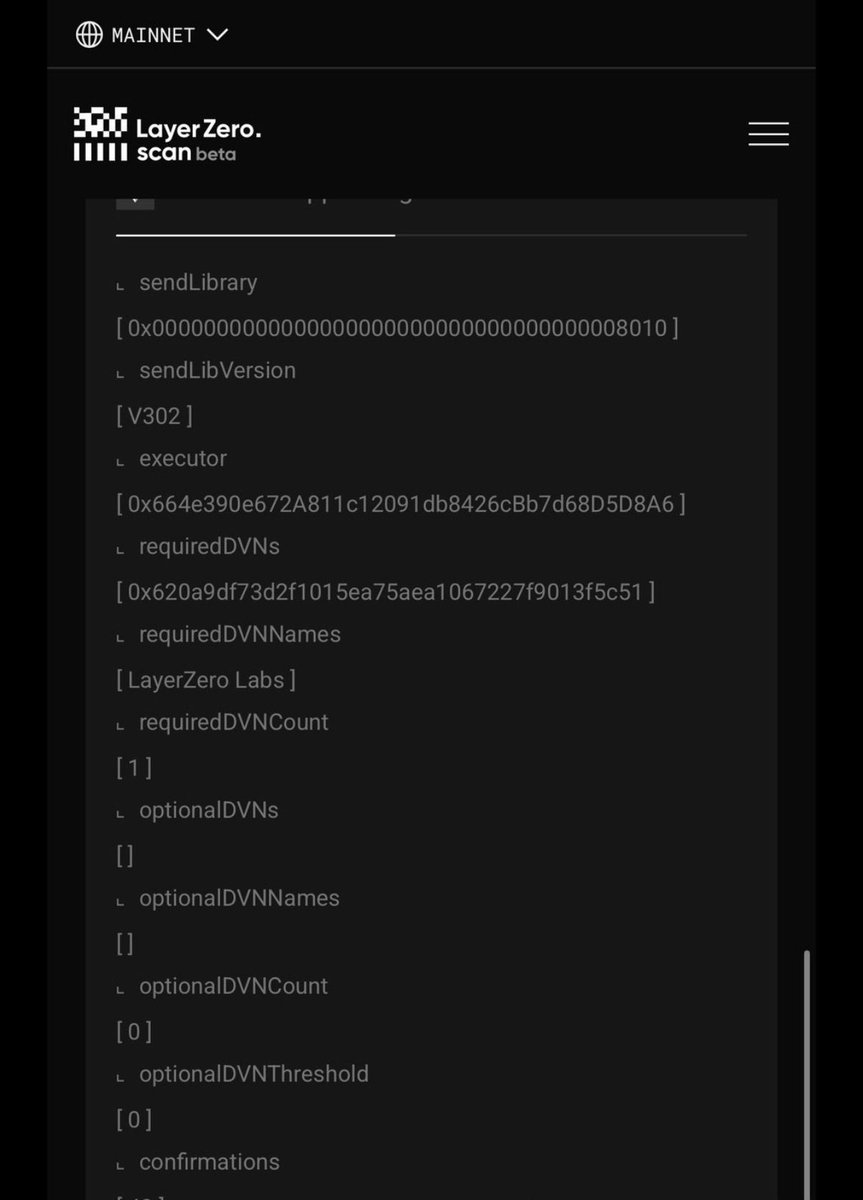
A forensic look at the Arbitrum intervention this morning, because the onchain details connect directly to the @KelpDAO attacker wallets traced in the earlier thread. At block 454686044 on Arbitrum on 2026-04-21 at 06:45:56 UTC, a state transition moved 30,765.6674 ETH out of an attacker-controlled address at `0x5d3919f12bcc35c26eee5f8226a9bee90c257ccc` and into a previously-empty address at `0x0000000000000000000000000000000000000da0`. The receipt is at `0x5618044241dade84af6c41b7d84496dc9823700f98b79751e257608dac570f6b`. After the transaction completed, the attacker's Arbitrum address retained 0.0001 ETH of dust and went silent. The destination address holds exactly the 30,765.6674 ETH and has no contract code attached. Two details about the transaction itself are worth calling out. It consumed exactly 21,000 gas, which is the fixed cost of a vanilla ETH transfer with no contract logic attached. It emitted zero logs. Together those two numbers tell you the Security Council did not execute this through a standard governance pathway with a multisig-signed authorization trail. They appear to have rewritten the state directly, and the transaction entry surfaces the state write as if it were a regular transfer out of the attacker's address. Odysseas from Phylax described this earlier today as "manually upgrading the system contracts and the client code in tandem to perform an improper state transition," and the onchain fingerprint is consistent with that reading. The more striking observation is about where the 30,765 ETH came from in the first place. The attacker's Arbitrum consolidation address received inbound ETH over a short window on 2026-04-18 from six of the seven fresh EOAs used in the original Ethereum mainnet attack. `0x1b748b68` sent 7,877 ETH. `0xeba786c9` sent 12,382 ETH. `0xcbb24a6b` sent 4,318 ETH. `0xe9e2f48b` sent 4,431 ETH. `0x8d11aeac` sent 999 ETH. `0xbb6a6006` sent 758 ETH. Those six amounts sum to 30,765.67 ETH, which matches the clawback amount exactly. The only one of the seven original EOAs that did not feed this Arbitrum wallet is `0x1f4c1c2e`, which is the EOA that held its 53,000 rsETH position on @aave V3 Ethereum mainnet and is still sitting on it right now. Said differently, the Arbitrum state transition cleanly zeroed the full Arbitrum arm of the coordinated attack. Every piece of ETH that the attacker had moved onto Arbitrum is now out of their control. The mechanism by which those six EOAs generated ETH on Arbitrum in the first place, whether through Aave Arbitrum loans against bridged rsETH, DEX swaps, or a combination, is not directly visible from this consolidation wallet's history. What is visible is the arithmetic: 30,765 ETH in, 30,765 ETH out, exactly and in one transaction. Three observations worth landing separately. The first observation is about selectivity. Arbitrum acted this morning. Other chains that held parts of the attacker's position, or held bridged rsETH supply affected by the exploit, have not executed anything similar so far. Circle, which could in theory have frozen USDC had the attacker converted into stablecoin before the clawback, also did not act. A security researcher in a live channel earlier today noted the uncomfortable counterfactual: if the attacker had swapped the ETH into USDC on Arbitrum before 06:45 UTC, they would have been in the clear today. The capability to intervene exists in more places than the feed acknowledges. It fires only when a specific set of humans decides to pull it. The second observation is about precedent. Odysseas from Phylax made the point that if the Clarity Act reaches proceedings in the United States, this intervention will sit in the record as an example. The regulatory framing question around L2s is whether they qualify as decentralized networks or something closer to centralized money transmitters, and a Security Council that can execute a state transition to claw back specific funds will get cited in whichever direction the regulators end up taking it. @banteg credited Arbitrum for making a hard decision. James Prestwich pointed out that both Ethereum and Bitcoin have historical precedent for clawing back exploited funds. The discomfort some people are expressing today is really discomfort with the capability being acknowledged at this visibility level, not with the existence of the capability itself. The third observation is about the bad debt math. The 30,765 ETH, worth approximately 70M dollars at current ETH spot, is the single largest recovery event in the @KelpDAO / @LayerZero_Core / @aave incident so far. It does not directly offset the attacker's WETH debt on Aave mainnet, which remains open, but it does materially shrink the global loss pool across all chains involved. The three protocols have spent the last seventy two hours lawyered up and publicly blaming each other through press statements and live channels. The recovered ETH pool is a bigger chip on the table than any of them was expecting to have by this morning, and it makes the scenario where users take a minimal haircut meaningfully more plausible than it was yesterday. The architectural capability to do what Arbitrum did this morning was always there. The Security Council has always had the authority to upgrade contracts and the client code that runs them. What changed today was the willingness to use that authority visibly enough that the transaction shows up in a block explorer as a 21,000-gas transfer with zero logs and 30,765 ETH on the value line. The receipt is public, the precedent is set, and neither one is going anywhere.





An onchain investigation of the @KelpDAO / @LayerZero_Core incident, broken into the stages the attacker actually moved through. Everything below comes from Ethereum mainnet receipts, not from writeups. Each stage traces what happened, how the market reacted, and what the onchain data says about numbers that are still being debated on the feed. Stage one, the setup. Nine hours before the attack, at block 24905614, a fresh address called `0x4966260619701a80637cdbdac6a6ce0131f8575e` received 0.9939 ETH through an internal transfer. When the attacker's own tx went out later, this wallet was still sitting at nonce zero, which means the wallet had never been used for anything before that incoming transfer. The sender of that 0.9939 ETH is interesting. Etherscan labels the address `0x47ce0c6ed5b0ce3d3a51fdb1c52dc66a7c3c2936` as `TornadoCash_eth`. So the funder is the 1 ETH Tornado Cash pool itself, and the 0.9939 figure is the payout minus the Tornado relayer fee. Looking further upstream, the router used was `0xd90e2f925da726b50c4ed8d0fb90ad053324f31b`, which is literally called `TornadoRouter` onchain. The attacker used Tornado to obscure where the gas money came from, and did it cleanly enough that the trail ends at the pool itself. This is worth calling out because several early tweets said the wallet was "pre-funded through Tornado Cash," which is true but vague. The onchain reality is more specific: one 0.9939 ETH withdrawal, nine hours before execution, to a brand new address that only ever did one thing. Stage two, the forged packet. The attack centers on a single forged cross-chain message submitted to LayerZero. The packet itself is readable byte for byte. The version byte reads 1. The nonce reads 308. The source chain ID reads 30320, which is LayerZero's identifier for @unichain. The sender address on the source side is `0xc3eacf0612346366db554c991d7858716db09f58`, which is the rsETH OFT deployment on Unichain. The destination chain ID reads 30101, which is Ethereum mainnet. The destination receiver is `0x85d456b2dff1fd8245387c0bfb64dfb700e98ef3`, which Etherscan has verified as `RSETH_OFTAdapter`. In plain language, the packet claims that a legitimate message had been emitted on Unichain telling the Ethereum adapter to release rsETH. No such message had been emitted on Unichain at that nonce. The DVN that was supposed to verify this claim signed off on it anyway. That signature is the entire breach, and everything else downstream is consequence. The nonce of 308 is oddly specific. Either the attacker knew the exact counter state on the Unichain side when they crafted the forgery, or the DVN was not checking continuity of nonces at all. Neither possibility reads well for the verification layer. Stage three, the commit. At block 24908283 on 2026-04-18 at 17:35:11 UTC, the attacker submitted their first transaction. It was a call to `commitVerification` on the contract at `0xc02ab410f0734efa3f14628780e6e695156024c2`. That contract matters because it is not a Kelp contract. It resolves to `ReceiveUln302`, the LayerZero V2 receive library, deployed by LayerZero Labs in January 2024. The function `commitVerification` is permissionless. Anyone can call it once the required DVN signatures for a given packet already exist. All the actual cryptographic work has happened offchain by the time the transaction goes out. This is the key finding of the investigation. The attacker did not need to be the DVN operator to execute the onchain part of the attack. They only needed the DVN to have already signed the forged packet. Everything that followed was routine on their end. Stage four, the release. Two blocks later, at 24908285, about twenty four seconds after the verification commit, the attacker called `lzReceive` on the LayerZero V2 endpoint at `0x1a44076050125825900e736c501f859c50fe728c`. The transaction burned 94,456 gas and emitted exactly one token transfer event. That event shows 116,500.0000 rsETH moving from the OFT Adapter at `0x85d456b2...` to an address at `0x8b1b6c9a6db1304000412dd21ae6a70a82d60d3b`. That address was labeled in community posts as the "exploiter contract," but onchain it is actually an EOA, not a contract. Its code length is zero. The attack was orchestrated from externally owned accounts, not from a dedicated exploit contract. The rsETH token itself lives at `0xa1290d69c65a6fe4df752f95823fae25cb99e5a7`. At the rsETH spot price during that hour, 116,500 tokens work out to approximately 292M dollars. Stage five, the fan-out. What happened in the following six minutes, between blocks 24908285 and 24908316, is what tells us the attacker had done homework. The exploiter address fanned the entire 116,500 rsETH across seven brand new EOAs, each of which had held zero balance before. The address `0x1f4c1c2e610f089d6914c4448e6f21cb0db3adef` received 53,000 rsETH. `0xeba786c9517a4823a5cfd9c72e4e80bf8168129b` received 30,000. `0xcbb24a6b4dafaaa1a759a2f413ea0eb6ae1455cc` received 10,000. `0x1b748b680373a1dd70a2319261328cab2a6f644c` received 8,000. `0xbb6a6006eb71205e977eceb19fcad1c8d631c787` received 6,000. `0x8d11aeac74267dd5c56d371bf4ae1afa174c2d49` received 5,000. The last one, `0xe9e2f48bb0018276391aec240abb46e8c3cad181`, received 4,500. Those numbers add up to 116,500 exactly. What is less expected is how specific the shares are. Those sizes do not look random. They look like someone measured, in advance, how much rsETH each downstream venue was going to accept before the protocol parameters refused the deposit, and then chose the chunks accordingly. Whoever built this knew the venue caps before the attack started. Stage six, where each chunk actually went. Tracing what happened after each of those seven EOAs received their share, the picture of the full attack strategy emerges. This is the part the feed has mostly not lifted out of the onchain data. The largest share, 53,000 rsETH at `0x1f4c1c2e`, went straight to @aave V3 on Ethereum mainnet. The attacker deposited the entire 53,000 rsETH as collateral and received an equivalent 53,000 aRsETH in return. Against that collateral, they borrowed 52,440 WETH. The position is still open on chain and currently reads 53,000 aRsETH collateral and 52,448.80 variableDebtWETH as the exact onchain numbers at this moment. A secondary position on @aave V3 came from `0x8d11aeac`, which deposited 400 rsETH and borrowed 393.98 WETH. Combined with the `0x1f4c1c2e` position, the attacker's total direct exposure on Aave V3 Ethereum sits at 53,400 rsETH on the collateral side and approximately 52,843 WETH on the debt side. Two of the seven EOAs, `0x1b748b68` and `0xe9e2f48b`, did not stay on Ethereum. They called into a LayerZero helper contract called `LZMultiCall` at `0xacddac6c77318b615f7f6fb9bb67c6833e9c05f1` and bridged their 8,000 and 4,500 rsETH respectively to @unichain and from there out to other destinations. The event logs show destination EID 30110, which is Arbitrum. The attacker was extending the exploit to Aave Arbitrum, and likely other chains, using the same LayerZero infrastructure that had just been compromised. The `0xeba786c9` wallet that received 30,000 rsETH used Lido infrastructure to swap into wstETH and then forwarded the wstETH onward through a series of transactions. The `0xcbb24a6b` wallet that received 10,000 moved through WBTC and WETH intermediaries in a pattern that looks like swap legs on Uniswap. The `0xbb6a6006` wallet that received 6,000 converted directly into roughly 5,580 ETH. So the attack was not a single theft into a single lending market. It was a coordinated multi-chain, multi-venue extraction that used at least three lending protocols, multiple bridges, and parallel swap paths. The 53,000 chunk that reached Aave Ethereum is only the biggest single piece, not the whole story. Stage seven, the Kelp pause. Kelp's OFT adapter is owned by a Gnosis Safe at `0xcbcdd778aa25476f203814214dd3e9b9c46829a1`. The first `execTransaction` call against that Safe after the attack lands at block 24908497, which is 212 blocks after the attack started. At Ethereum's twelve second block time, that works out to roughly 42 minutes. The widely cited "46 minutes from forged message to emergency pause" figure in writeups and news posts is reasonably close to the onchain reality. The Safe signers, visible in the execTransaction callers, are `0x51c5978563`, `0x7aad74b7f0`, and `0xfcc1c98f88`. The pause was not a single tx but a sequence of Safe operations between blocks 24908497 and 24908648, which takes the actual completed pause closer to 47 to 50 minutes after the attack rather than the clean "46 min" framing. Stage eight, the second attempt and why it failed. At block 24908538, roughly 51 minutes after the first attack, the same attacker EOA `0x4966...` submitted another `commitVerification`. It succeeded, which is the part that should bother people. The DVN had signed a second forged packet during the window while Kelp was actively pausing. The verification layer was still approving forgeries. One block later, at 24908539, the attacker called `lzReceive` again. That transaction reverted. A few blocks after, at 24908547, they tried once more and it reverted too. The reason both second attempts failed is that Kelp had, by that point, paused the OFT adapter through their Safe actions, so the downstream execution could no longer complete. The asymmetry is the interesting finding. The Kelp pause worked at the application layer. The LayerZero verification layer kept signing fraudulent packets the whole time. The attacker could have done more damage through other OFT-configured tokens using the same DVN if those tokens had not also been paused by their respective teams. Stage nine, the verified bad debt math. This is where the numbers on Twitter have been all over the map. Onchain, the situation is more boring than most of the estimates. The aRsETH token on Aave V3 Ethereum currently holds 525,760.90 rsETH as its total supply. That is the total rsETH deposited on Aave V3 Ethereum from every depositor combined. Of that, approximately 53,400 rsETH is the attacker's direct deposit across the two EOAs. The other approximately 472,360 rsETH is pre-existing user collateral that was already on Aave before the attack, owned by regular rsETH depositors. The WETH aToken on Aave V3 Ethereum currently holds only 0.01 WETH. The WETH reserve is effectively empty. Total variable debt on WETH across Aave V3 Ethereum runs approximately 2,667,860 WETH. Combined, these two numbers confirm the community claim that WETH borrowing on Aave is at near-100% utilization, which is why borrow rates on USDC and USDT reportedly spiked toward 15 percent in the hours after the attack. The attacker's direct bad debt contribution, meaning the portion of the debt where the attacker's collateral would not cover the loan, depends on how rsETH ultimately gets repriced. If the loss is socialized across all rsETH holders on all chains, the implied writedown sits around 18 percent. Under that scenario, the attacker's position becomes underwater by approximately 13.8M dollars at a rough ETH price of 2,300 dollars per WETH. That is a small piece of the total, and the broader picture becomes one of haircuts on legitimate depositors rather than true bad debt. If instead the bridged L2 versions of rsETH are written down to zero while mainnet rsETH stays fully backed, the mainnet Aave position of the attacker is technically still over-collateralized, and the real bad debt gets concentrated on the Aave Arbitrum and Aave Mantle deployments where the bridged chunks of 8,000 and 4,500 rsETH ended up. Aave Arbitrum reportedly had 62,280 rsETH deposited across all users, and Aave Mantle reportedly had 47,280, both of which would be at risk under this scenario. The technical recalculation currently circulating on Twitter, attributed to one analyst, puts the actual Aave bad debt figure at approximately 75.9M dollars. That number sits roughly in the middle of the two scenarios above and is currently the most defensible estimate in circulation. None of this has been formally endorsed yet by @aave governance. Stage ten, the broader market response. The dollar numbers from market moves should be read as reported rather than independently audited. AAVE token reportedly traded down between ten and fourteen percent in the hours after the attack, with the range depending on which feed someone reads. Ether itself reportedly fell around 3.7 percent to approximately 2,300 dollars. Observers on the @aave side cited roughly 5.4B dollars in ETH withdrawal outflows in the hours that followed the attack. The onchain reality supports the direction of this claim, given that the WETH aToken now reads 0.01 WETH as its balance, but the exact 5.4B number deserves an independent tally before it gets treated as settled. One wallet that many onchain watchers attribute to @justinsuntron reportedly pulled around 65,584 ETH, worth approximately 154M dollars. The movement itself is visible on chain at the addresses attributed to that wallet, but the ownership attribution is not publicly confirmed by the wallet's operator. Borrow rates on USDC and USDT in affected markets reportedly spiked toward 15 percent. Large holders reportedly dumped around 60,000 AAVE tokens across the aftermath. These numbers are consistent with the feed narrative of a liquidity panic, but clean onchain tallies are still being pieced together by observers and have not been formally published. Stage eleven, Aave's safety buffers, verified onchain. On the @aave safety module side, the onchain totals look like this. The legacy stkAAVE safety module holds approximately 2.97M staked AAVE tokens. The stkABPT pool holds approximately 2.84M staked Balancer tokens. The newer stkGHO Umbrella module holds approximately 240M stkGHO. Using rough current prices, the stkGHO module is approximately 240M dollars in backing, the stkAAVE legacy module sits around 250 to 300M dollars depending on AAVE price at the moment of slashing, and the stkABPT module is another 300M or so. Combined, the theoretical safety buffer across all three sits somewhere between 700M and 850M dollars, though whether any given piece of that buffer actually becomes available for this specific loss depends entirely on how Aave governance classifies the incident and which modules they choose to slash. Community posts have cited "Umbrella 40M, legacy 312M" as the number pair, and those figures roughly match the stkAAVE and stkABPT modules specifically, not the combined picture. The stkGHO Umbrella is much larger in headline dollar terms but may not be available for slashing on non-GHO losses without governance action. Stage twelve, the industry-wide shape of the problem. The single Unichain route that was exploited had been configured with a 1-of-1 DVN, meaning one required signer carried the entire cross-chain verification. Community counts put 24 of the 26 rsETH pathways on the identical 1-of-1 @LayerZero_Core Labs setup, which is what turns this from a Kelp accident into a broader industry signal. The attacker only needed to pick one door because one door already turned out to be enough, and the other 23 were structurally identical. The exposure extends well past rsETH. Similar OFT deployments with 1-of-1 or 2-of-2 DVN configurations are running on USDT0, Ethena USDe, Sky USDS, AUSD, USDai, Cap cUSD, Reservoir rUSD, infiniFi iUSD, @ether_fi weETH, mETH cmETH, and Puffer pufETH. PYUSD is reportedly deployed on a similar @LayerZero_Core OFT configuration controlled by a single EOA owner, with a self-reported market cap above 9B dollars. After the Kelp incident, USDT0, Ethena, Sky, EtherFi, and Cap paused their bridges preemptively. LayerZero's own founder announced in a live chat during triage that LayerZero Labs has blocked all weak configs, specifically 1-of-1, from its own infrastructure and is actively helping other protocols migrate to stronger configurations. This is actual post-incident action and has not yet been widely picked up on the feed. Pulling it all together. The short version is that no contract was exploited in the sense people usually mean. Every line of solidity across @LayerZero_Core, @KelpDAO, @aave, @compoundfinance, @MorphoLabs, SparkLend, Fluid, and Euler executed correctly. The breach was a single offchain validator signing a packet that described a source-chain event which had never happened. That signature was enough, because the verification threshold on that route was one required signer. The attacker built the attack with the kind of precision that suggests the DVN compromise was not opportunistic. The 7-way fanout, the precomputed venue caps, the parallel bridge-outs to other chains, and the nine-hour Tornado timing all point to a planned operation, not a smash-and-grab. The Kelp response worked at the application layer, forty two minutes from attack to the first Safe action. The LayerZero verification layer continued signing forged packets into the second attempt window, which is the more uncomfortable piece. The bad debt, once the dust settles, is probably smaller than the opening estimates of 177 to 200M dollars and larger than the pure "only attacker's position is underwater" minimum. The 75.9M dollar technical recalc is currently the most defensible middle. Whichever way the haircut politics land, the outcome will set precedent for how every other 1-of-1 OFT-configured asset gets treated the next time this happens.

Kelp DAO's rsETH bridge apparently exploited for roughly $292 million in LayerZero-based attack theblock.co/post/397988/ke…







Due to the KelpDAO exploit, the attacker deposited $RSETH into #Aave to borrow $ETH, creating bad debt on #Aave. Many whales have already rushed to withdraw their $ETH from #Aave. $ETH Utilization Rate on Aave has now reached 100%.










