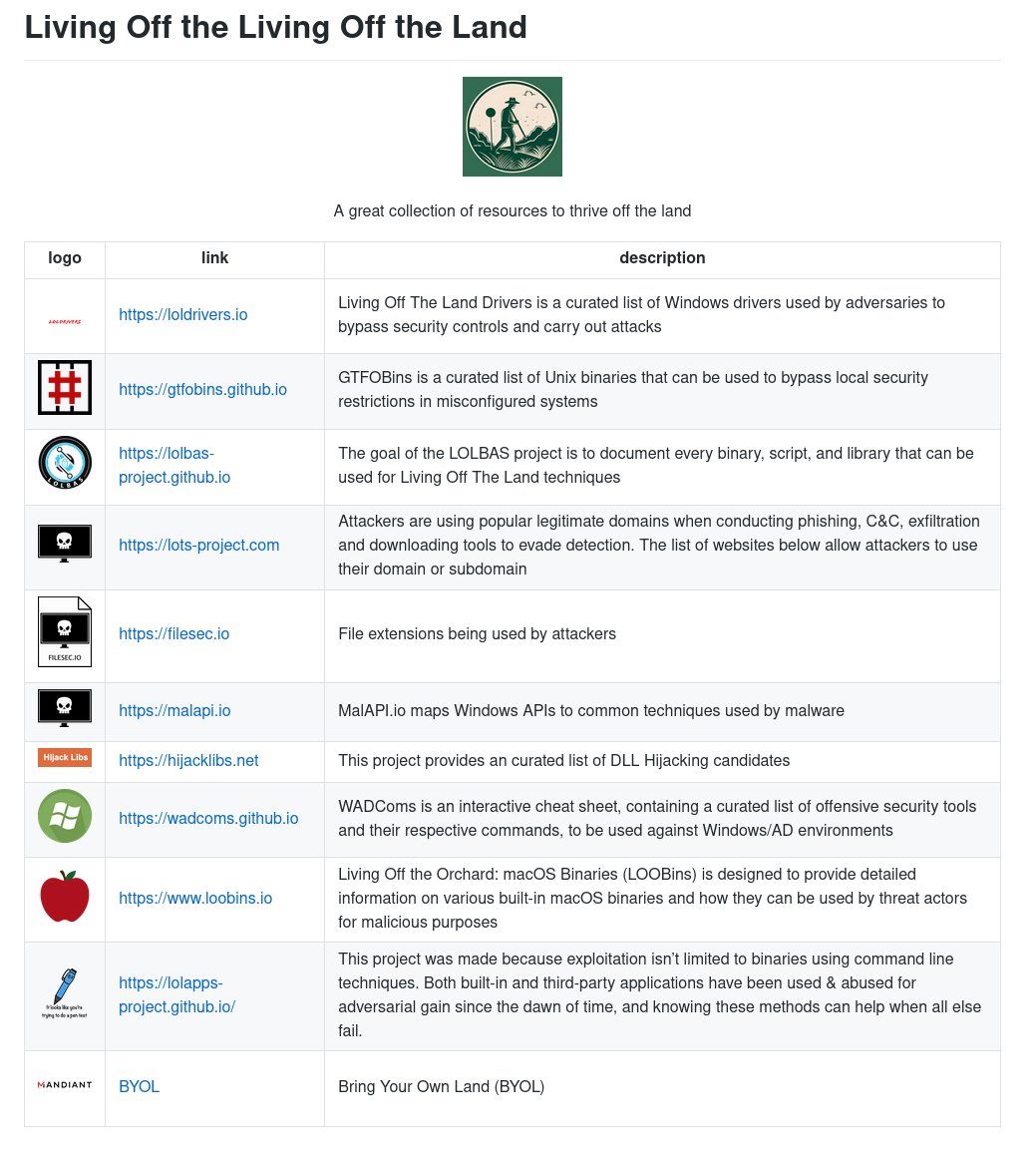
Maybe I’m just being a spoilsport here but someone should point out it’s not your job to worry about an attack like xz unless you are in a very precise role and this is fun but you should get back to disabling NTLMv1 on Monday and patching your network devices.