Steve Syfuhs
47.1K posts


Steve Syfuhs
@SteveSyfuhs
Windows and Authentication at Microsoft. Developer. Mostly dog pictures. Might actually be two dogs in a trench coat. 🇺🇸 / 🇨🇦 @syfuhs.net on blue sky


























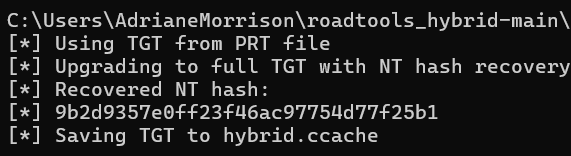
@NathanMcNulty @StevenKister1 It generally follows the lifetime of the PRT or max age of the TGT, whichever is less. It's a bit wonky because while they are given at the same time, they aren't inherently bound to one another. You can get a TGT that lives longer than SIF, but in practice you never will.




🎧 Join Dustin Heywood @Evil_Mog, Hacker, Researcher, and Senior Leader at IBM, on the latest episode of The #BlueHat Podcast as he demonstrates cracking NTLM version 1, shares insights on auditing legacy systems, and discusses the critical role of IT asset management. Tune in now: podcasts.apple.com/us/podcast/sec… Don’t forget to take our BlueHat podcast survey for a chance to win an exclusive BlueHat Yeti cup: forms.office.com/r/YpPS2LAv5S