Sabitlenmiş Tweet

Subreption releases research exposing critical security flaws in FIPS/Common Criteria certified enterprise network switches. (subreption.com/press-releases…)
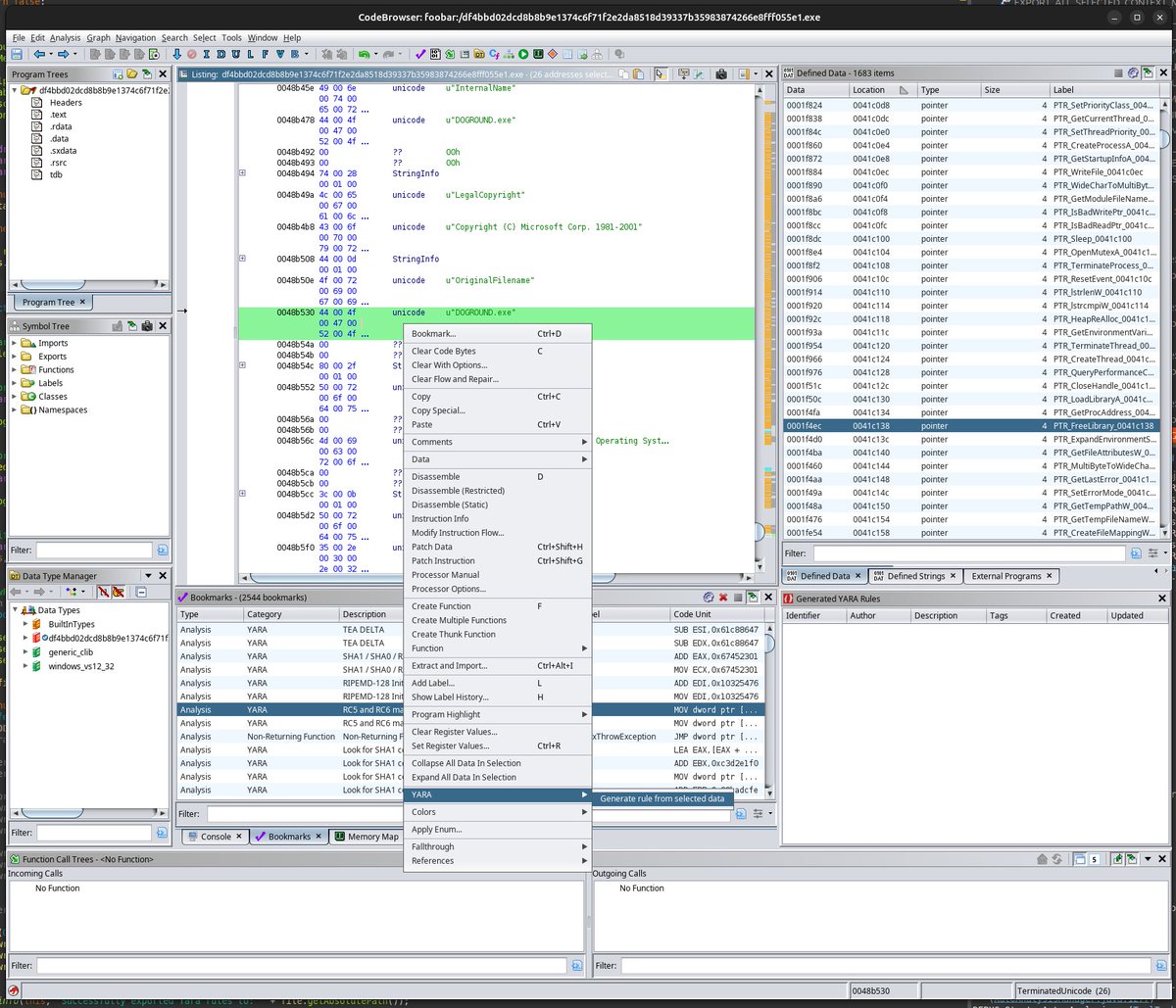
FLAPPYSWITCH abuses CVE-2024-50604, CVE-2024-50605, CVE-2024-50606 and CVE-2024-50607, for breaking out of the management "cli", executing a modular loader and achieving persistence in the underlying Linux-based OS through classic ELF infection techniques.
Vendor patches quietly released (Jan 2025) insufficiently addressed the issues, and misrepresented them as requiring physical access. Vulnerabilities remain exploitable.
Our research hopes to bring proper attention to the state of the art in enterprise network equipment security, as it is often overlooked, in the wake of the Salt Typhoon incident.
Available at:
github.com/subreption/FLA…
Stay tuned for updates.
#FLAPPYSWITCH #salttyphoon

English