Sunil retweetledi

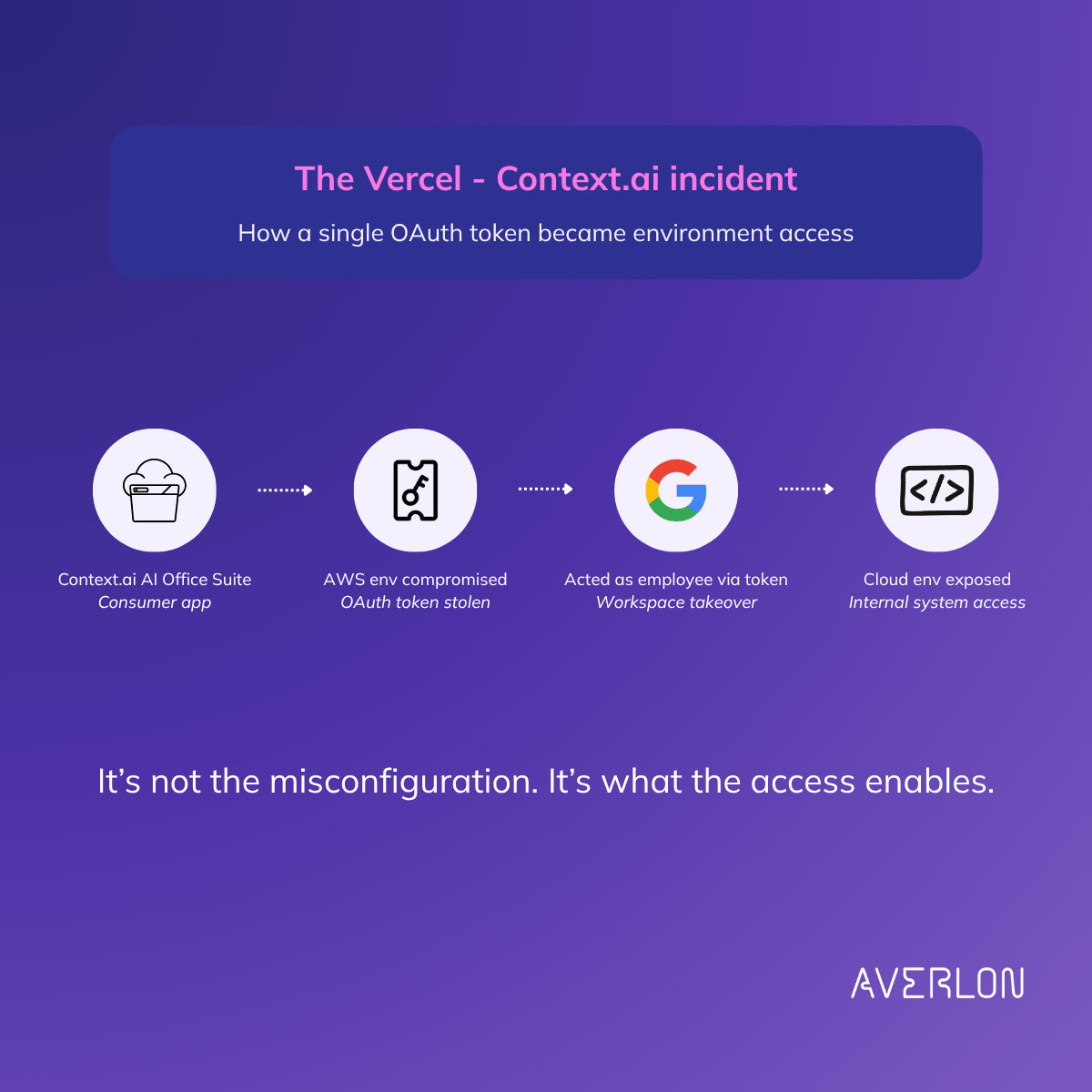
𝗧𝗵𝗿𝗲𝗲 𝗶𝗻𝗰𝗶𝗱𝗲𝗻𝘁𝘀. 𝗧𝗵𝗿𝗲𝗲 𝗰𝗼𝗺𝗽𝗮𝗻𝗶𝗲𝘀. 𝗢𝗻𝗲 𝘂𝗻𝗱𝗲𝗿𝗹𝘆𝗶𝗻𝗴 𝗽𝗮𝘁𝘁𝗲𝗿𝗻.
Vercel. Lovable. Vimeo.
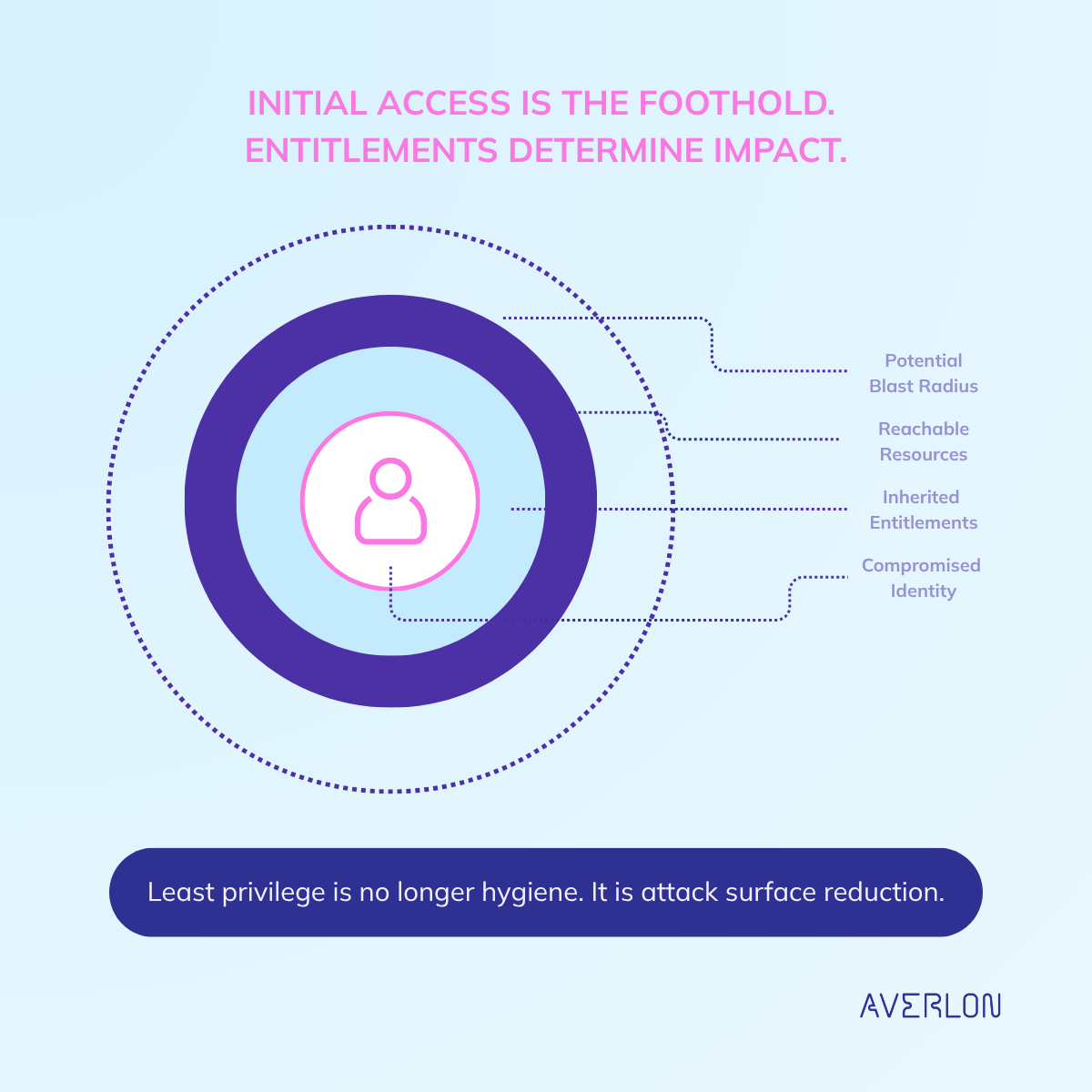
In each case, the breach wasn't in the target's own code. It was in a third-party tool with token-based access into connected environments.
Once the token was compromised, the blast radius was defined by what that token was allowed to do.
𝗜𝗻𝗶𝘁𝗶𝗮𝗹 𝗮𝗰𝗰𝗲𝘀𝘀 𝘀𝗲𝘁𝘀 𝘁𝗵𝗲 𝗲𝗻𝘁𝗿𝘆 𝗽𝗼𝗶𝗻𝘁. 𝗘𝗻𝘁𝗶𝘁𝗹𝗲𝗺𝗲𝗻𝘁𝘀 𝘀𝗲𝘁 𝘁𝗵𝗲 𝗯𝗹𝗮𝘀𝘁 𝗿𝗮𝗱𝗶𝘂𝘀.
In practice: service principals accumulate permissions. Third-party integrations inherit broad access. Tokens sit dormant until they don't.
When something goes wrong, permissions decide how bad it gets.
averlon.ai/blog/when-perm…
English