Tecnurd
1.1K posts

Tecnurd
@tecnurd
Programmer with a love of science and learning.



"I've never experienced hate like it," Eileen Flynn told The Journal, after a video of remarks she made in the Seanad about the recent fuel protests went viral in certain circles online on Wednesday. jrnl.ie/7014874









Far-right leaders from Europe will gather in Milan for a rally against irregular immigration and Brussels bureaucracy, the first since the electoral defeat of nationalist Viktor Orbán in Hungary rte.ie/news/world/202…




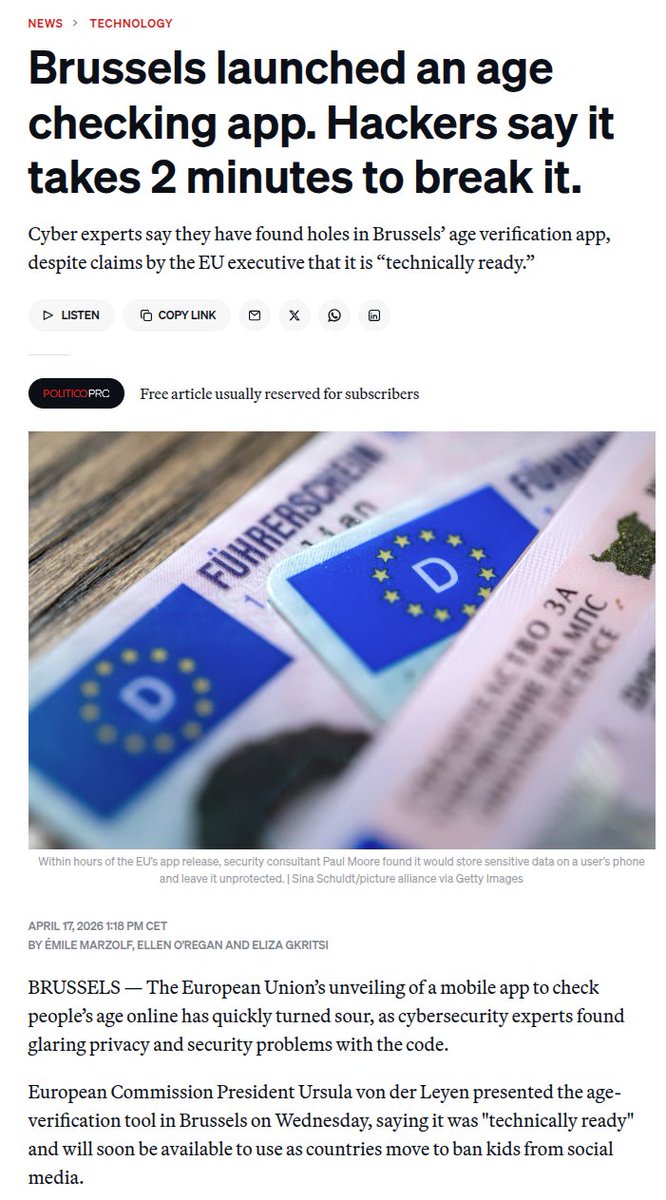
🇪🇺 The EU age verification app can be bypassed in minutes. The PIN isn’t properly tied to the user’s data, so deleting it lets you set a new one while keeping access to existing credentials. Other protections are just editable settings, making the system easy to manipulate. How many millions of euros did this defective app cost? Source: @Paul_Reviews

@CR1337 Parents should stay in full control. They buy the phone, so they decide what their child can access and for how long using traffic filters and screen limits. This is far harder to bypass than any app. The issue with this app is explained next x.com/Paul_Reviews/s…




Let's shift focus and explain why the #EU #AgeVerification concept is fundamentally flawed. Assume: 1. The production app is released. 2. It's 100% secure, 100% private (fantasy land, but stick with me) 3. It cryptographically challenges every step, including hardware attestation which requires a physical device. 4. Every single other attack vector in the surrounding environment is somehow magically patched. aka - it's working exactly as intended/designed. It does not protect against a relay attack. This is a threat they considered and somewhat addressed here: github.com/eu-digital-ide… With the current design, there's nothing preventing someone running a verification-as-a-service; a remote Android device which returns a valid attestation. Remember, it's not returning "I am over 18", it returns "someone is over 18". Neither the verifier, nor the app has any way to link the session ID to a physical device. Their own docs state this clearly: Remote Cross-Device Presentation: "Note that the Wallet Instance does not see any difference between the cross-device flow and the same-device flow. In both cases, it receives an OpenID4VP-compliant presentation request over the Wallet Instance-platform API described in the previous section." This is a known & well-understood attack vector in all remote credential presentation models; it's just not mitigated in this one... primarily because they can't. CTAP 2.2 won't work with all app flows, hardware attestation doesn't mitigate relay attacks, on-demand liveness detection would be too intrusive & potentially privacy-invasive & timing calculations don't reveal anything useful... all the available options to resolve this break the core design; completely anonymous age verification. The Architecture & Reference Framework (ARF) is technically sound in some respects. They considered external threat actors and discussed solutions to mitigate them, including ZKP. However, the EC applied the wrong threat model, thus arriving at the wrong conclusion. Yes, you need to protect against malicious verifiers, phishing sites, session hijacks, data brokers et al... but that's addressing external threats, it doesn't protect the architecture from the user itself. In virtually every other scenario, the user and system's interests are aligned; protect my biometric asset at all costs. Specifically for age verification, most users do not want to present ID simply to access a website, so whilst the system may adequately protect from external threats, if the user wants to bypass the system, they can... and the architecture doesn't consider this. Every single applied mitigation assumes the user is the protected party, not the threat actor. To those people claiming "it requires physical access to the device and root, this is BS/hyperbole", you too applied the wrong threat model & completely missed the point. These disclosures demonstrate that you, the user, are the threat actor they haven't considered. You have your device. You can root your device. You can create a chrome extension, just as I did. Ironically, it's precisely those under 18 who can't pass verification who are motivated to bypass it. So where does that leave us? A system which replaces "I am over 18" with "someone is over 18", with absolutely no guarantee that it's true... which is the entire purpose of the app.








Conferenza sulla navigazione marittima nello Stretto di Hormuz: dichiarazioni congiunte alla stampa con @EmmanuelMacron, @Keir_Starmer e @_FriedrichMerz