Tim Smart
453 posts


Tim Smart
@tim_smart
I hack on @EffectTS_


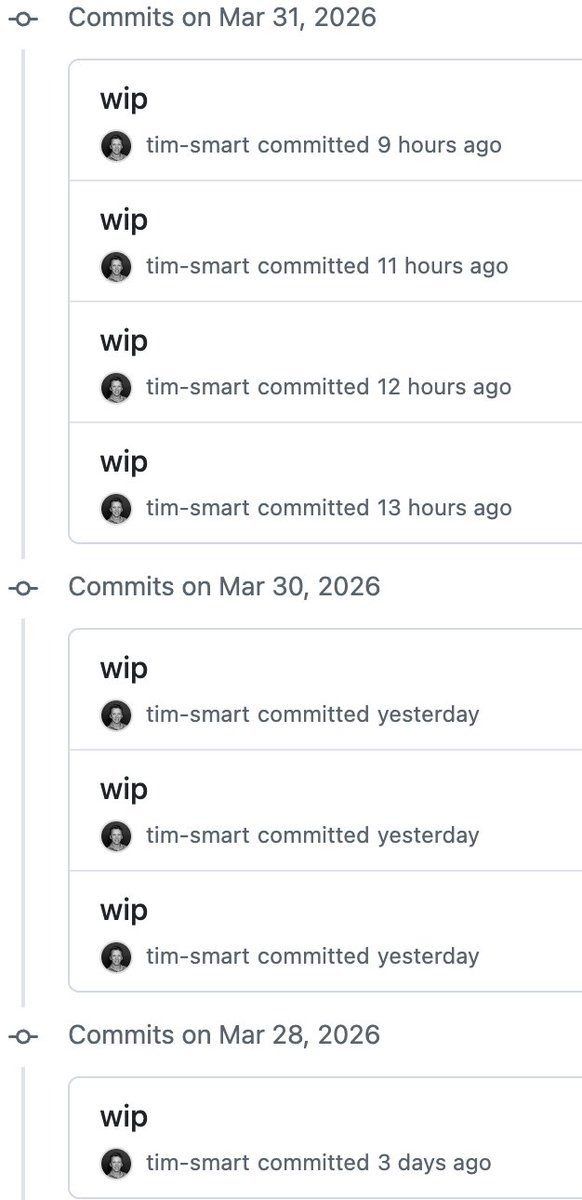
OpenCode v1.4.4 released. TL;DR: Effect architecture migration • Embedded WASM Ripgrep • PII redaction for exports • Alibaba Cloud support • Core Architecture Replaced global async runtime facades with Effect, unifying service injection, contextual logging, and improving composability across core subsystems. Swapped the external Ripgrep binary backend for an embedded WASM version, improving platform portability and shrinking the standalone executable size. • Providers Added Alibaba Cloud Model Studio provider package and cache support. Upgraded GitHub Copilot to use the new messages API when available. Guarded reasoningSummary injection for @ai-sdk/openai-compatible proxies (e.g. LiteLLM) to prevent API rejection. • Tools & Capabilities Added a --sanitize flag to opencode export to strip PII and confidential information before sharing session transcripts. Exposed workspace adaptors to plugins, allowing custom workspace strategies. Added experimental.compaction.autocontinue plugin hook to disable the synthetic auto-continue prompt after compaction. • UI & TUI Added an interactive burst animation to the TUI logo and fixed contrast for diff line numbers across built-in themes. Compare: github.com/anomalyco/open…




Pills for llm coding from an OpenAI talk at @aiDotEngineer : - have single shared utils to do stuff like bounded concurrency - treat errors as values and part of the control flow - use telemetry for everything - rely on static analysis for backpressure Should we tell them???


🚨 CRITICAL: Active supply chain attack on axios -- one of npm's most depended-on packages. The latest axios@1.14.1 now pulls in plain-crypto-js@4.2.1, a package that did not exist before today. This is a live compromise. This is textbook supply chain installer malware. axios has 100M+ weekly downloads. Every npm install pulling the latest version is potentially compromised right now. Socket AI analysis confirms this is malware. plain-crypto-js is an obfuscated dropper/loader that: • Deobfuscates embedded payloads and operational strings at runtime • Dynamically loads fs, os, and execSync to evade static analysis • Executes decoded shell commands • Stages and copies payload files into OS temp and Windows ProgramData directories • Deletes and renames artifacts post-execution to destroy forensic evidence If you use axios, pin your version immediately and audit your lockfiles. Do not upgrade.