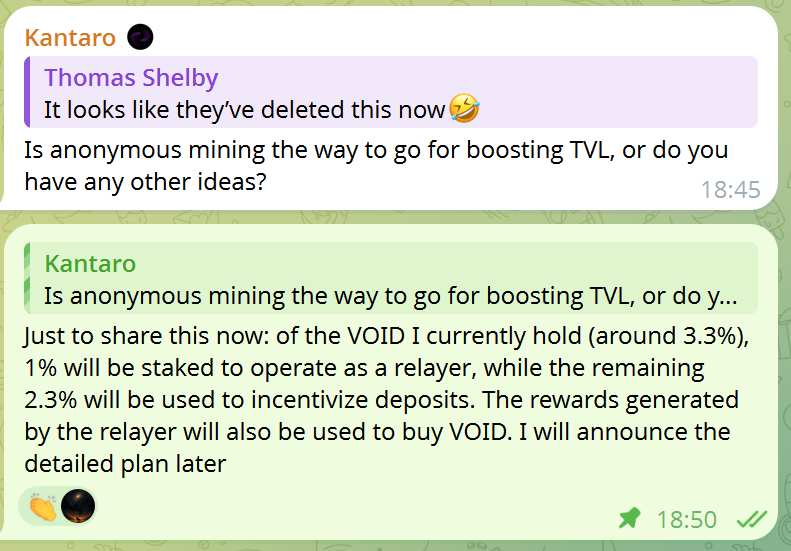
tornadosto retweetledi

I, @tornadostoshi, am officially announcing that the app is now live on IPFS.
voidifycto.eth.limo
This is more than just a website launch. Moving to IPFS means the app now lives in a decentralized way — transparent, persistent, no longer dependent on any single party to keep it online, and no longer something that can be simply shut down by one party. It marks a real step toward censorship resistance, permanence, and community ownership
From this moment on, the project is community-run. This is a true CTO — a Community Takeover. Voidify is alive again, and this time it grows with the community.
Now people can see clearly what was true and what was not.
Call back everyone who was abandoned. Call back every Void holder. This is not the end — it is only the beginning.
Roadmap:
Website Launch → IPFS (Now) → TVL Growth → Relayer → Staking → Governance/Voting → The Ultimate Monster (Full Form)
Voidify remains under the same CA: J2bUGZDxRDpsVfjZqKwn6yYCUKFmqzHgt8UajhGtpump
Watch us
Please note:
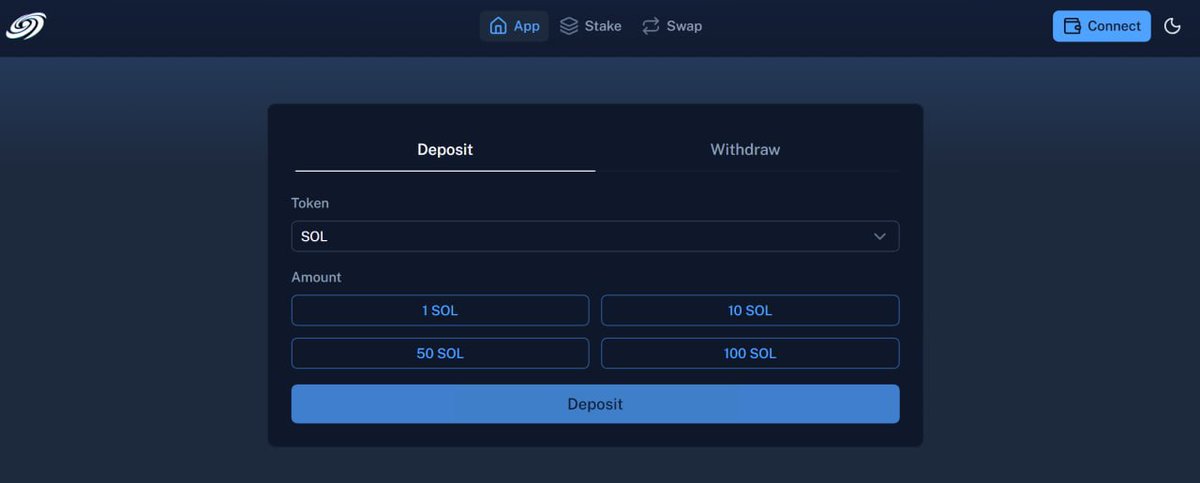
It’s currently live on devnet for initial testing and trial runs
for devnet solana(faucet.solana.com)
since the app is now decentralized and hosted on IPFS, the first visit may require a bit of patience while the files finish syncing across the network. If your deposit or withdrawal does not go through on the first try, refresh the page and try again. IPFS propagation takes time, and this is a normal part of the transition to a fully decentralized setup
English