UdDin
144 posts


UdDin
@uddin070
I am a Cyber Security Enthusiast and very much passionate about this subject.
Bangladesh. Katılım Ağustos 2015
189 Takip Edilen20 Takipçiler

When you can solve all PortSwigger labs on your own without watching community solutions.
THE|VOICE|OF|THE|STREET®@THESTREETVOICE3
At what point can someone confidently call themselves a Hacker?
English

Hi everyOne, sorry for being inactive lately. I was dealing with some health issues over the past few weeks, but I’m happy to say that I’m completely fine now and back to working again.
Right now, I’m working on the next 2-3 videos, and I also want to give an update regarding the Dependency video. It might take a bit longer than expected because I genuinely want it to be one of the best videos ever uploaded on this channel. I don’t want to rush it just for the sake of uploading. I’m putting a massive amount of time, research, and effort into it, so I appreciate your patience.
Also, for older membership users, you can cancel your upcoming month’s subscription for now so your money doesn’t get wasted during the delay. Once the Dependency conclusion video is released, you can renew it again. And trust me, I’m 200% sure it’ll be worth every single penny.
Till then, I’ll continue uploading some public videos for everyone. Thank you for all the support and patience ❤️

English

Just scored a reward @intigriti, check my profile: app.intigriti.com/profile/arifen… #HackWithIntigriti
English

Uploaded!!
My Manual Hacking Process During Bug Hunting ( Part 1 )
youtu.be/F0z4t2sdtyQ?si…
YouTube
English

@Cyberhijabitech Right, then they repeat it infront of neighbours or relatives.
English

Alhamdulilah!
Got My First Bounty!
First Bounty always special
Thanks to almighty Allah!
And thanks my two childhood friends imran and sahidul..
Keep prayers for mine!
#YesWeHack
#FirstBounty
#Alhamdulillah
#BugBounty
#Hackerone

English

A long time ago, in a shell far, far away… 🌌
A red teamer decided it was time to prove they were ready.
CrowdForce is Bugcrowd’s elite red team, and we’re looking for hackers with the skills to execute the greatest attack simulations, adapt under pressure, and collaborate with some of the smartest minds in offensive security.
Think you’re ready? 🦸
May the force be with you. Learn how to join CrowdForce: bugcrowd.com/blog/how-to-jo…
English

F**k! I didn't look at the scope... they marked it as *OOS* "Password and account recovery policies, such as reset link expiration," but it does lead to ATO, still.
I don't know why they added such in *OOS*
You can definitely look out for it on your target ( might get accepted if not listed in *OOS* )
Tip -
1. Create a test account ( test@gmail.com )
2. Logout, then do a *password reset* on *test@gmail.com*
3. Once you get the reset link, take note of it ( do not use it yet )
4. Login back to *test@gmail.com*
5. Change email from *test@gmail.com* to *another@gmail.com* ( make sure email change is verified / successful )
6. Logout from *another@gmail.com*
7. Attempt login to *test@gmail.com* ( results to "Invalid login", due to the email doesn't exist in the system, anymore )
8. Now, go back to the *reset link* sent to *test@gmail.com*
9. Try to use it to set a new password. If successful, the account with the email *another@gmail.com*, password, will be changed.
The old email address, although no longer valid for authentication, still retained account recovery capability.
A realistic scenario -
1. An attacker gains temporary access to the victim's old email inbox or obtains a reset link.
2. The attacker requests a password reset and keeps the link.
3. The victim later updates their account email to a new address, believing the account is secured.
4. The attacker uses the old reset link to reset the password and regain full access.
Gospel@4osp3l
This vulnerability is an interesting one ( it leads to ATO )! I sent the report a few days ago. Once the report gets accepted, I'll share some tips. You might probably spot the same misconfiguration on your target! I've no idea of the severity ( could be an easy P2/P3 ).
English

Let’s test your 💎 Rails knowledge
@user.update(params.require(:user).permit(:name, :bio, :is_admin))
What’s the bug?
A) Insecure Direct Object Reference
B) Mass assignment leading to privilege escalation
C) Server Side Request Forgery
D) Cross Site Request Forgery
Bonus: Which parameter should never be user-controlled here? 😈
English

Yay, I was awarded a $600 bounty on @Hacker0x01
hackerone.com/deepvvm
#TogetherWeHitHarder
#bugbountytip
Tip :
Upload Documents > open in a New Tab
/29582.gif 200 OK ✅
/29581.gif 403 Forbidden ❌
victim delete the document
try to access it again
/29581.gif 200 OK ✅
English

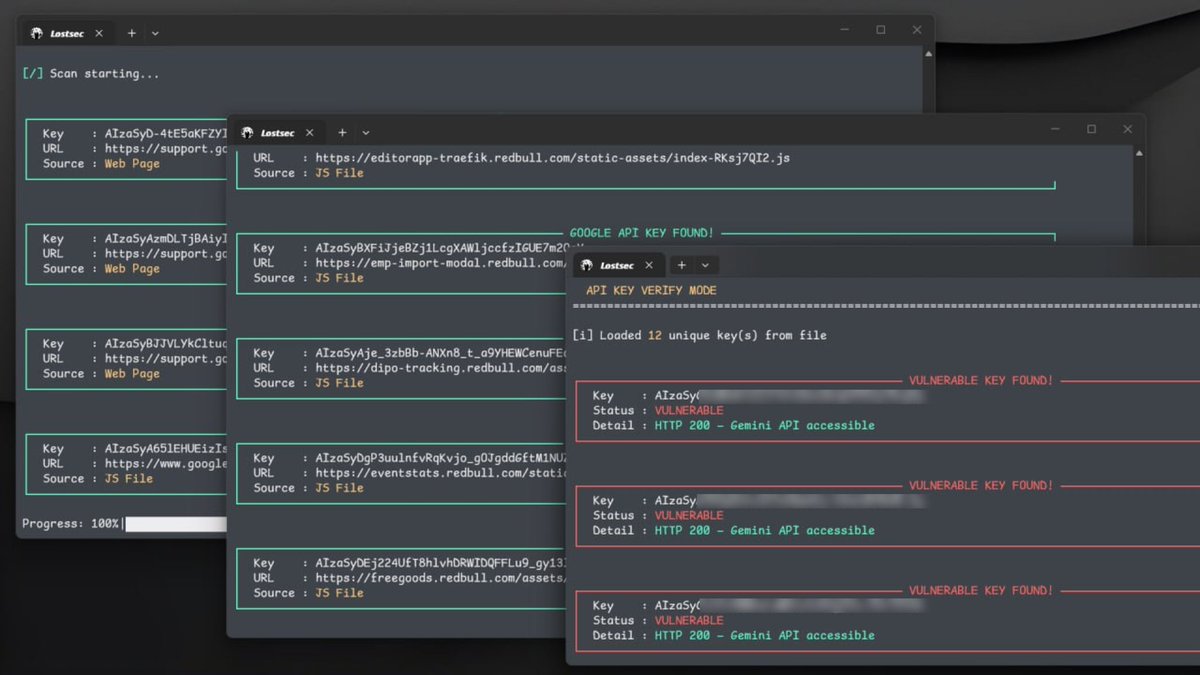
things are getting more serious.
[github dorking + manual hunting + burp extensions + private tools + a custom panel to use discovered API keys like gemini chat interface…
just enter a target domain or a list of subdomains and the tool handles the rest.
it scrapes API keys from page source and JS files at full high speed, then lets you verify them for vulnerable to issues like file disclosure, upload, delete and more.
this is just a small demo.
full video coming soon with much more things combined. you have no idea how much impact a single leaked API key can have at scale.
stay tuned.

English