

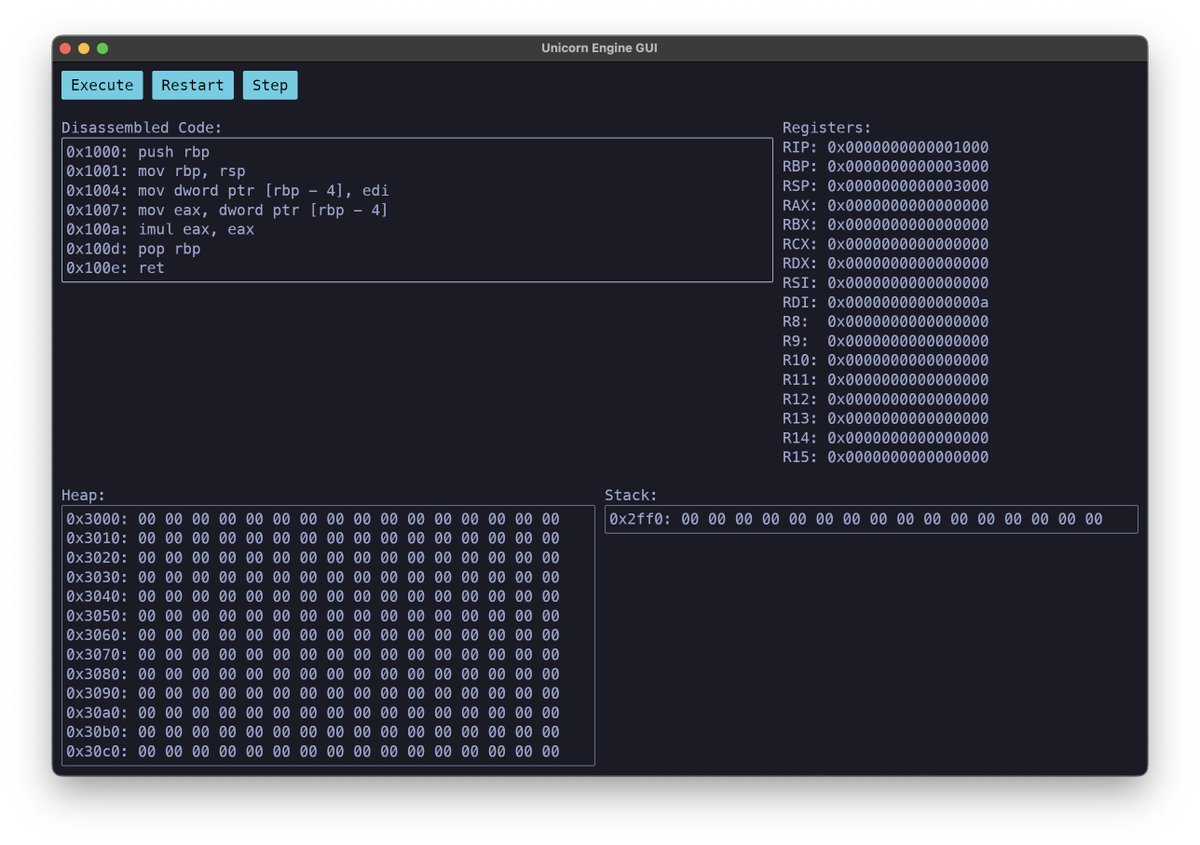
Unicorn Engine
1.3K posts

@unicorn_engine
The Ultimate CPU Emulator. Also see our related frameworks @capstone_engine, @keystone_engine





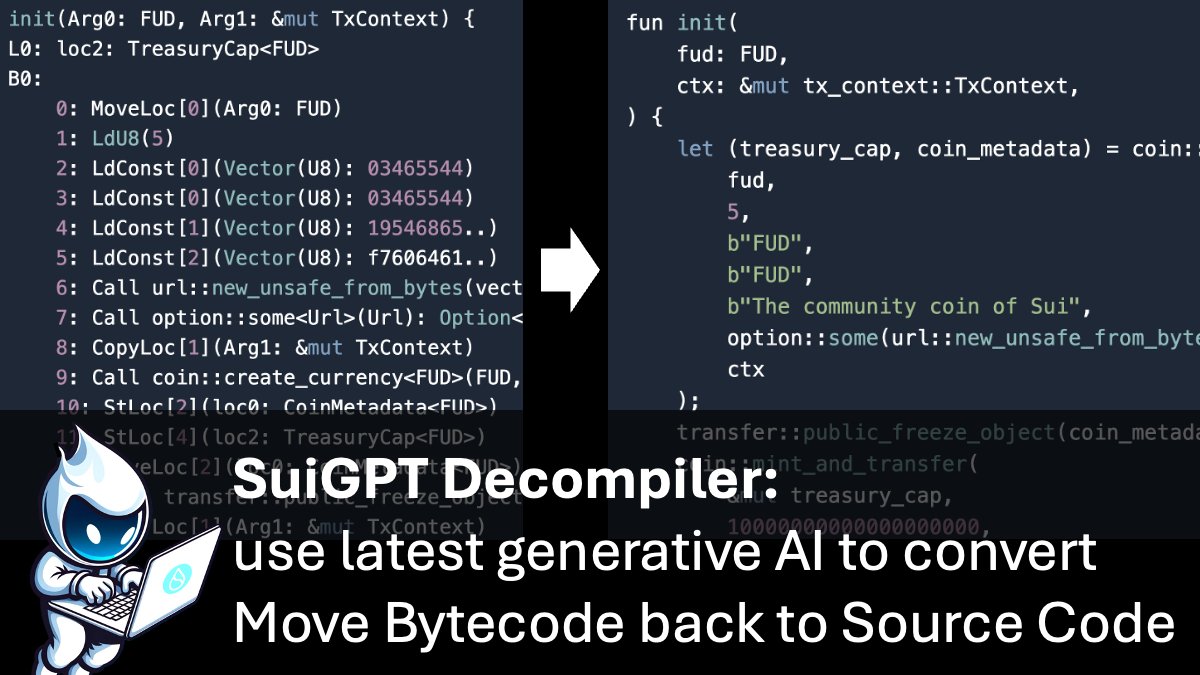


The Move decompiler developed in collaboration by @Verichains and @AptosLabs is a game changer for the security on the @Aptos network. It allows to convert any bytecode deployed on chain back to source code. Only possible with Move! aptoslabs.medium.com/move-revealed-…





1. On May 21, 2023, Multichain CEO Zhaojun was taken away by the Chinese police from his home and has been out of contact with the global Multichain team ever since. The team contacted the MPC node operators and learned that their operational access keys to MPC node servers had been revoked. Furthermore, these MPC node servers, like all other ordinary servers, were actually running under Zhaojun's personal cloud server account. No member of the team has access to Zhaojun's personal cloud server account, so nobody can log on to these MPC servers. 2. Later, the team established contact with Zhaojun's family and learned that all of Zhaojun's computers, phones, hardware wallets, and mnemonic phrases were confiscated by the authorities. Since the inception of the project, all operational funds and investments from investors have been under Zhaojun's control. This also means that all the team's funds and access to the servers are with Zhaojun and the police. 3. Due to the lack of information about the case, the team could only maintain project operations to the best of their abilities through the remaining access on some non-MPC servers that hadn't been revoked yet. Per the lawyer's suggestions, the team has chosen to cooperate as much as possible with the demands of Zhaojun's family and adhere to the requirements of local laws and regulations, refraining from disclosing unauthorized information about the case to the public. 4. On May 30, in a responsible approach toward the community, the team released the news about Zhaojun's disappearance and informed the community about the technical issues currently faced. 5. On June 4, Zhaojun's family successfully logged into the cloud server platform using the historical information on his home computer. However, Zhaojun's family only allowed Multichain team engineers physical access to the home computer to fix technical issues with Router2 and Router5. 6. During this period, Zhaojun's family and the lawyer were in communication with the police. The team was not informed about the details of the case but was notified that Zhaojun would be released soon and was asked to continue maintaining the system and await further updates. 7. The Multichain protocol continued to operate as designed. The team made every effort with limited resources to sustain the operation of the Multichain protocol and resolve user issues as much as possible. 8. On July 7, user assets locked on the MPC addresses were transferred to unknown addresses abnormally. According to Zhaojun's sister, login information from an IP address in Kunming was found on the cloud server platform, along with a series of operations transferring funds from the MPC addresses. 9. On July 9, Zhaojun's sister transferred the remaining user assets in the router pool and subsequently notified the team and several project parties of this asset preservation action. The funds were transferred to EOA addresses controlled by Zhaojun's sister. 0x1eed63efba5f81d95bfe37d82c8e736b974f477b 0x6b6314f4f07c974600d872182dcde092c480e57b 10. On July 13, according to information provided by Zhaojun's family, the police took Zhaojun's sister into custody. Now, Zhaojun's sister is also out of contact. The status of the assets she has preserved is uncertain, so the team believes it is necessary to inform the community about all the known circumstances. 11. Due to the lack of alternative sources of information and corresponding operational funds, the team is forced to cease operations. If there are any further notifications and developments, the team will update the community accordingly. 12. The Multichain team does not have the access to Domain Account to redirect or bring down the frontend multichain.org. Please help amplify and ask users not to use the Multichain service anymore. Can @GoDaddy help to bring down multichain.org? Thanks.

THORChain: There are claims of a potential vulnerability with a THORChain dependency that may affect THORChain. Out of an abundance of caution, steps have been taken to halt THORChain globally. THORChain is a settlement layer that facilitates swaps between 8 chains. x.com/pluto9r/status…



Join @onlyxwings at #HITB2023HKT to discover bugs in IoT devices with the Qiling Framework. Learn standard workflows and leverage Qiling's capabilities for efficient emulation. Register at conference.hitb.org/hitbsecconf202… #IoTsecurity #QilingFramework


Join @onlyxwings at #HITB2023HKT to discover bugs in IoT devices with the Qiling Framework. Learn standard workflows and leverage Qiling's capabilities for efficient emulation. Register at conference.hitb.org/hitbsecconf202… #IoTsecurity #QilingFramework




I've put together a new blog post! This one re-treads @bl4sty's earlier AMLogic research but takes my own approach to exploit development, with an 'alternative' vulnerability and an emulator. Just for fun! boredpentester.com/retreading-the…


