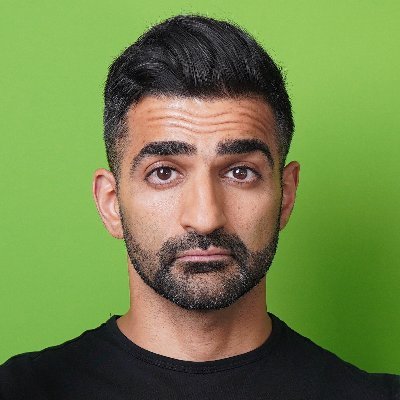
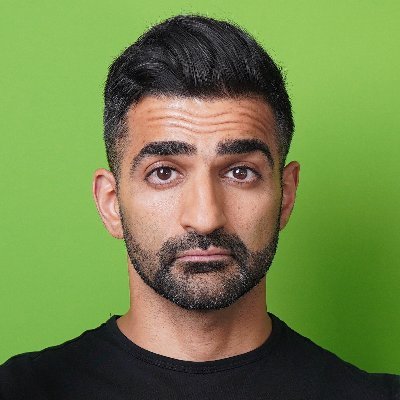
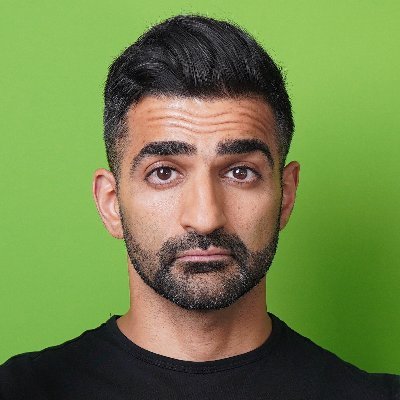
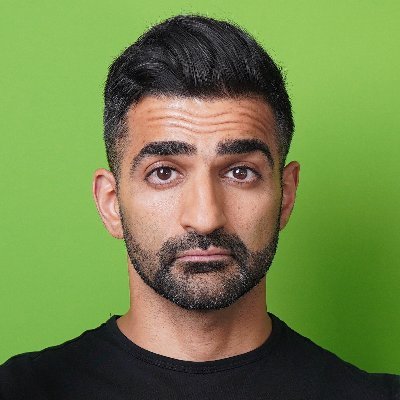
Anuj Soni
752 posts
Anuj Soni
@asoni
Malware Reverse Engineer. Instructor & Author. Occasional YouTuber.



Today's Training Tuesday Highlight is @asoni! Want to learn Malware Analysis & Reverse Engineering? Check out his awesome FREE videos with links to the samples included in the descriptions so you can follow along! YouTube Channel: @sonianuj" target="_blank" rel="nofollow noopener">youtube.com/@sonianuj
#MalwareAnalysis #IncidentResponse #DFIRDivaTTH

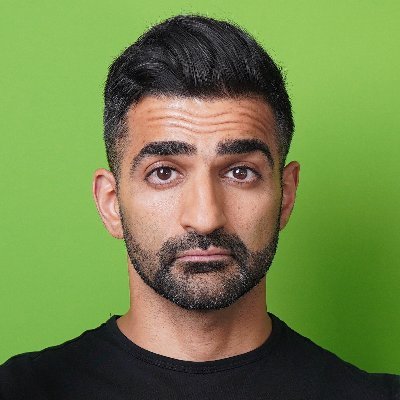
Part 2 of my shellcode analysis series is here! This time, we’re automating shellcode extraction with one of @hasherezade’s incredible open-source tools. 🎥 Watch now: youtu.be/D6Bm5vD78eY

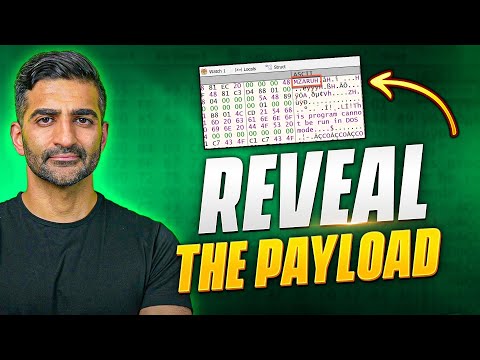
Supply chain malware from an infected game mod 🤯😱 Long-form reverse engineering and a WILD ride: Binary Ninja, x64dbg, 010 Editor, PEB walking, reworking API function hashing in Python, DLL search-order hijacking, hooked functions & more. MASSIVE video: jh.live/bvyklJ5Wie0