usmann
1.5K posts

usmann
@usmannk
a bit confused | Protocol @Plasma 🕊️



back in Ldn! 🇬🇧 8 months in the Gulf taught me a lot. but for what I'm building, London is the right base. → unmatched talent density → Imperial, Oxford, Cambridge, UCL → hiring cheaper than SF/NYC → @OpenAI and @AnthropicAI expanding coffee if you're around🤝




At Frax, we did all of these mitigations immediately & more at the very beginning before rolling out our frxUSD LZ mint-burn mesh. I'm surprised how many other projects didn't. We use our own libraries (no external entity can upgrade them, not even LZ), we run our own Frax DVN internally with veto privs but require external DVN unanimous consensus to transfer value, we've had 3/3 DVN policy since last year (increasing to 5/5 soon), & are currently working on even more advanced+secure hook logic compared to the simple rate limiter/circuit breakers projects are just starting to deploy. If you want to collaborate or need crosschain guidance, feel free to reach out to us to work on security together.

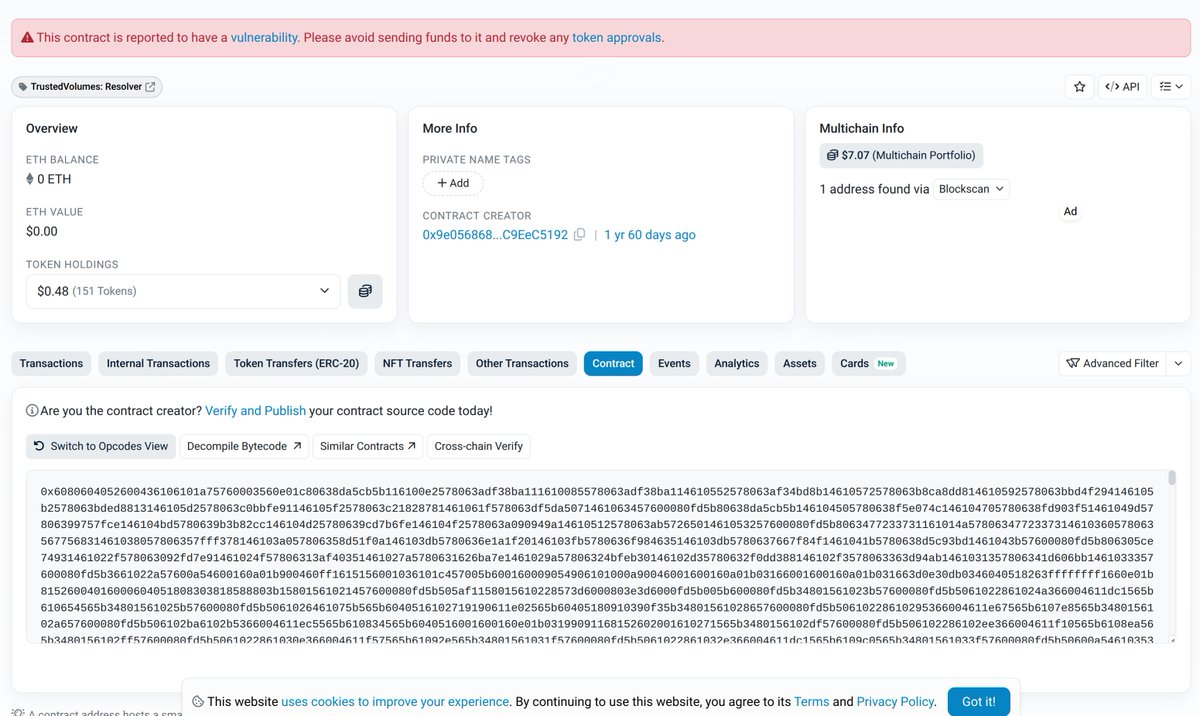
🚨 Blockaid's exploit detection system has identified an on-going exploit on TrustedVolumes (1inch market maker / resolver, @trustedvolumes ). Chain: Ethereum Victim contract: TrustedVolumes resolver — 0x9bA0CF1588E1DFA905eC948F7FE5104dD40EDa31 Exploiter: 0xC3EBDdEa4f69df717a8f5c89e7cF20C1c0389100 Exploit tx: 0xc5c61b3ac39d854773b9dc34bd0cdbc8b5bbf75f18551802a0b5881fcb990513 Total extracted so far: ~$5.87M (1,291.16 WETH + 206,282 USDT + 16.939 WBTC + 1,268,771 USDC). Same operator as the March-2025 1inch Fusion V1 incident; this is a different vulnerability, in a TrustedVolumes-controlled custom RFQ swap proxy (0xeEeEEe53033F7227d488ae83a27Bc9A9D5051756). More details will follow.

Why I think it's (at least somewhat) interesting that Ubuntu hired a Trans security researcher to look over the Rust-rewrites of CoreUtils: - The Rust programming language has been heavily promoted by, and associated with, Trans Activism. To the point where it has become a standard joke that everyone in Tech understands. - Rust is also tightly associated with people who pretend to be underage, anime style, animated girls on the Internet. Again, to the point where it has become a well understood cliche. - The motivation for replacing all of GNU CoreUtils with Rust-rewrites has appeared to be driven by a non-engineering motivation. Politics, a desire to remove GPL'd code from Linux distros, or both. - There are a *lot* of security research, code auditing, and consultant firms in the world. Ubuntu chose to go with one founded by someone "Trans". *And* who represents himself as an "underage, anime style, animated girl". Now, is this particular "Trans" / Anime person a good developer? Could be! But what is the likelihood of a "Trans" / "Underage Anime Girl but Actually a Grown Man" person being hired -- among all of the potential firms in the world -- without some sort of bias from Canonical / Ubuntu coming into play? I would suggest that "Trans Activism" and political bias likely played a large role in the choice of firm which got that contract. Maybe you are ok with that. Maybe you aren't. Either way, it's worth documenting as part of a broader movement within Open Source which has a heavy influence from both politics and Trans Activism.

Remember the security firm that Ubuntu hired to audit the (ill-advised, highly buggy) Rust-rewrites of all of the GNU Coreutils? Turns out that security firm is run by @gf_256, who: - Appears to be a man who thinks he's a woman ("trans"). - Uses an anime cartoon of a girl as his avatar. - Appears to have an OnlyFans page. I repeat: Ubuntu hired a "Trans" man, with an anime girl avatar and an OnlyFans page... to audit Rust code. It's hard to get more on-the-nose than that.

Remember the security firm that Ubuntu hired to audit the (ill-advised, highly buggy) Rust-rewrites of all of the GNU Coreutils? Turns out that security firm is run by @gf_256, who: - Appears to be a man who thinks he's a woman ("trans"). - Uses an anime cartoon of a girl as his avatar. - Appears to have an OnlyFans page. I repeat: Ubuntu hired a "Trans" man, with an anime girl avatar and an OnlyFans page... to audit Rust code. It's hard to get more on-the-nose than that.










