AndrewMohawk⁽ⁿᵘˡˡ⁾
12.7K posts


AndrewMohawk⁽ⁿᵘˡˡ⁾
@AndrewMohawk
Sec/Madness @privy_io principal security , @_seal_org technical council prev: HoS @uniswap, D&R/IR @RobinhoodApp, IR @BitMEX, Built @Paterva Maltego with RT

The future of mankind




Posting a mini XSS challenge! Goal is to pop an alert. I believe this trick is not well known. Intended solution is chrome only. Thanks to @kevin_mizu for beta testing! Don't post solutions in the thread; DM only! xss.hashkitten.io/xss1.html



Thanks everyone for playing! I talk about the solution here, as well as how I discovered this behavior while looking into the Chrome Sanitizer API: slcyber.io/research-cente…

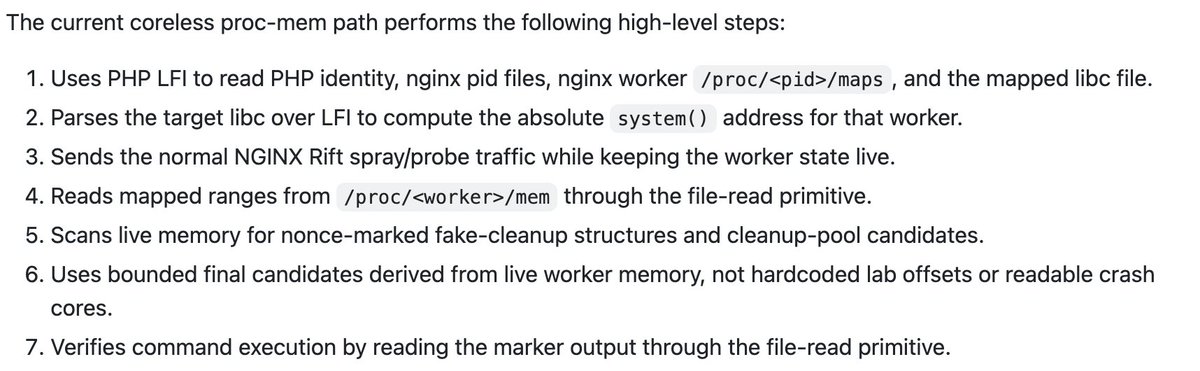
We’ve now seen at least four nginx RCEs that require non-default configs: nginx rift, nginx poolslip, and two of our own (including the one in the last tweet). The configs involved are unusual, which raises the obvious question: do these attacks actually work in real-world deployments? We asked Claude to download and analyze more than 4,000 nginx config files from GitHub. The result was embarrassing: none of them were vulnerable to nginx rift or our own attacks. We can’t say anything about nginx poolslip yet, since it hasn’t been published. So don't worry about your nginx yet. Moral of the story: AI can generate FUD, but also help fight FUD. Embrace it!








We are investigating unauthorized access to GitHub’s internal repositories. While we currently have no evidence of impact to customer information stored outside of GitHub’s internal repositories (such as our customers’ enterprises, organizations, and repositories), we are closely monitoring our infrastructure for follow-on activity.



We are investigating unauthorized access to GitHub’s internal repositories. While we currently have no evidence of impact to customer information stored outside of GitHub’s internal repositories (such as our customers’ enterprises, organizations, and repositories), we are closely monitoring our infrastructure for follow-on activity.