Emanuele Vannacci retweetledi
Emanuele Vannacci
97 posts
Emanuele Vannacci
@vanema94
PhD student at @vu5ec - (u)arch attacks && memory_safety
Amsterdam, The Netherlands Katılım Ekim 2011
442 Takip Edilen185 Takipçiler
Thanks to all my co-authors @jana_tweets_cs @oleksii_o Cédric Fournet and @socialboris for the amazin work. And thanks @vu5ec for supporting me in this project!
English
I'm thrilled to announce that our paper "Speculation@Fault" @USENIXSecurity is online! Read about how we automatically find information leakages arising from CPU exceptions by fuzzing against speculative contracts.
Jana Hofmann@jana_tweets_cs
Now that the embargo is finally lifted🥳: I'm excited to share details about our most recent work (appearing at USENIX this week) on modeling and testing microarchitectural information leakage of CPU exceptions (think Meltdown 👻and alike).
English
Emanuele Vannacci retweetledi

POV: @JakobKoschel and I (with @vu5ec) accidentally getting the Linux kernel to upgrade to modern C

LWN.net@lwnnet
[$] Moving the kernel to modern C lwn.net/Articles/88594…
English
Emanuele Vannacci retweetledi

Introducing #FPVI and #SCSB, two new transient execution vulnerabilities based on previously unexplored causes of Machine Clear. See vusec.net/projects/fpvi-…. We use FPVI to read arbitrary memory in Firefox via attacker-controlled and transiently-injected floating-point results:
GIF
English
Emanuele Vannacci retweetledi

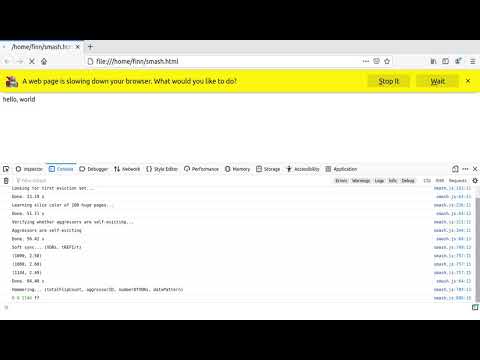
While we showed earlier that DDR4 is vulnerable to Rowhammer, we could not launch attacks from JavaScript. Until now.
By synchronizing memory requests with DRAM refresh commands, we show that web users are at risk also.
Page: vusec.net/projects/smash/
Demo: youtube.com/watch?v=k2D4D-…
YouTube
English
Emanuele Vannacci retweetledi

Our #PIBE paper @ASPLOSConf and code are now online. We show how to greatly reduce the overhead of mitigations such as LVI-CFI and retpoline on the kernel using PGO. Joint work by @victor_duta (who did all the hard work!) @c_giuffrida @herbertbos @EKouwe:
download.vusec.net/papers/pibe_as…
English
Emanuele Vannacci retweetledi

Three pages of nominations and looks like #TRRespass is the lucky winner of this year's most innovative research pwnie! Congrats to all @pit_frg @vanema94 @ArthasSin @vvdveen @_onurmutlu_ @c_giuffrida @herbertbos
English
Emanuele Vannacci retweetledi
Emanuele Vannacci retweetledi

#BlindSide’s source code is now online. We also released 2 new kernel exploit demo videos, e.g., Exploit 2: a single buffer overflow to speculatively break arbitrary randomization and mount an architectural data-only exploit
to leak the root password hash:
vusec.net/projects/blind…
GIF
English
@bz2 @VUamsterdam even without considering that surgical masks protect other people from you, so they work only if everyone wear them.
English

@VUamsterdam Dit is schandelijk. Als je het niet verplicht stelt (en dat zouden we moeten doen), waarom het niet adviseren? Het kost niks om zo'n advies uit te vaardigen. Waarom zou juist een universiteit de wetenschap op dit gebied negeren?
Nederlands

3/3 Femke Halsema gaf gister het advies om in publiek toegankelijke binnenruimten een mondkapje te dragen. Als universiteit vallen we hier niet onder. Op de VU geldt dat iedereen zelf een keuze mag maken wat betreft het dragen van een mondkapje. vu.nl/coronavirus
Nederlands
Emanuele Vannacci retweetledi

Best paper award @IEEEEUROSP! @rk_konoth didn't give up after the 1st, 2ed .. rejects. Kept improving the paper, formal verification, more features, integrations. Apparently there is sometimes a big light at the end of the tunnel! Talk on Thursday at 16:30 CEST
Radhesh Krishnan@rk_konoth
Our paper #SecurePay won the best paper award at @IEEEEUROSP 2020. Thank you @elathan @herbertbos @kavehrazavi et al. @vu5ec! Enjoy download.vusec.net/papers/securep…
English
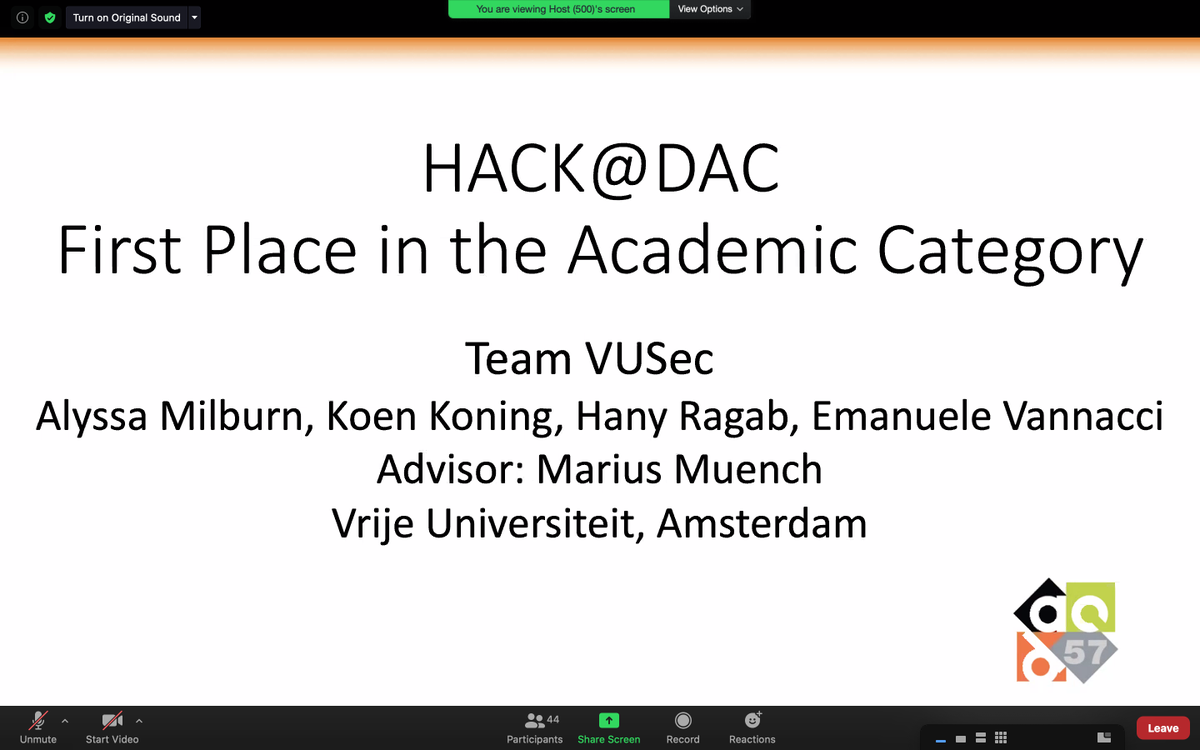
Emanuele Vannacci retweetledi

We tried something new! A virtual hardware Capture the Flag competition. Congratulations to @noopwafel, @hanyrax, @vanema94, and Koen Koning from @vu5ec, who took first place. #57thDac

English
Emanuele Vannacci retweetledi
Emanuele Vannacci retweetledi

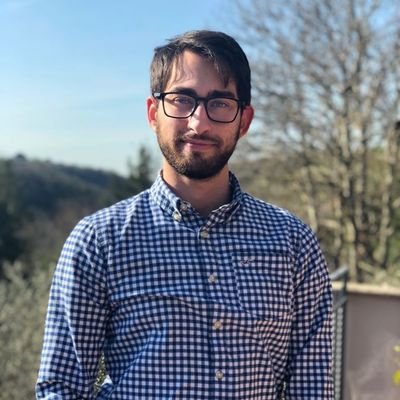
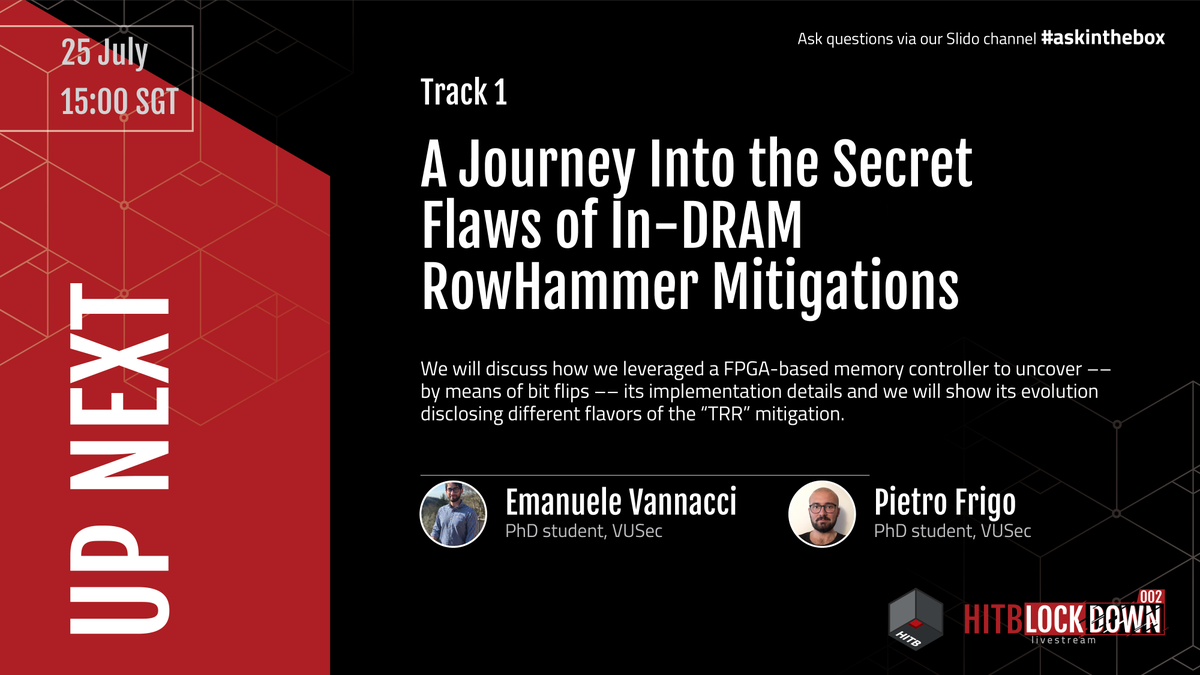
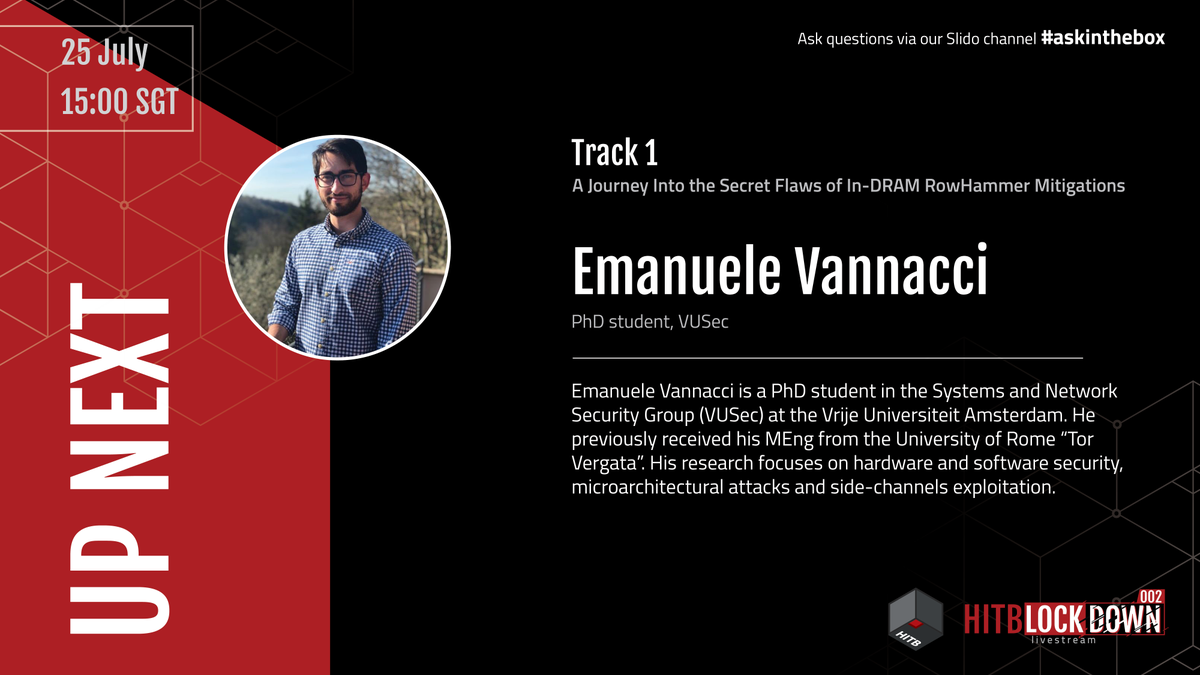
Next up on #HITBLockdown002 Track 1:
"A Journey Into the Secret Flaws of In-DRAM RowHammer Mitigations"
Presented by @vanema94 & @pit_frg
Starts 15:00 SGT at youtu.be/siylg59I6FA
Ask questions via our Slido channel #askinthebox

YouTube

English
Emanuele Vannacci retweetledi

Our #TagBleed paper is now online. We show Tagged TLB's performance benefits come at a security cost. TL;DR Confused-deputy side-channel attacks based on Tagged TLBs can break #KASLR even in face of ideal #KPTI or state-of-the-art KASLR mitigations:
download.vusec.net/papers/tagblee…
English
Looking forward for me and @pit_frg to present "A journey into the secret flaws of in-DRAM RowHammer mitigations" at @HITBSecConf2020 ! Don't miss it! #HITBLockdown002
English
Intel CPUs Vulnerable to New 'SGAxe' and 'CrossTalk' Side-Channel Attacks thehackernews.com/2020/06/intel-… via @TheHackersNews
English