Sabitlenmiş Tweet
ᅟ
780 posts


ᅟ
@vegowski
🇵🇱 | exceptional ragebaiter
Sandy Steppes, Placid Paddies Katılım Ekim 2021
484 Takip Edilen36 Takipçiler

🎥 SEASON 3 - The Fame Season is here! 🎉
🎁 Use code “COMMUNITY23” for a free Wrap!
▶️ Play Now: roblox.com/games/17625359…

English

Literally the best map ever made?
FUT RaGe@RaGe1030
pls can this thing be removed ???????????????????????????????????????????
English

Retiring from professional @FNCompetitive. Thanks to everyone who supported me. I will never forget the grands I won. 😢
English

@vegowski @FNCompetitive noo don't quit bro u finna become a scammer cause u got no j*b
English

@claasic_CS2 *ABSOLUTE DOGSHIT WAS AN OPTION BUT YOU WANT UNFINISHED GARBAGE
English

community is cooked
TRAIN WAS AN OPTION BUT YOU WANT UNFINISHED GARBAGE
FACEIT CS2@FACEITcs
Cache joins FACEIT matchmaking in Season 8 on April 22 following 148,840 votes. Matches on Cache will count toward your Elo. Players can deselect Cache without needing to subscribe or change your other map bans.
English

@vxunderground im worried, is gpu-z also affected or is it a different ownership?
English

Yeah, so pretty much this cpuid.com malware is a pain in the ass. I'd have to spend a good bit of time trying to bonk it with a stick and reconstruct some of it. Whoever developed this malware actually cares about evasion and made some intelligent decisions when developing this malware payload.
This appears to only impact HWMonitor 64bit. It appears (based on user reports) cpuid became malicious around 7PM EST, April 10th, 2026. However, it is possible it was much earlier than this, this is just when people began noticing and discussing it online.
From an extremely high-level overview, it appears the ultimate goal of this malware is data theft, specifically browser credentials. However, I could be wrong in that assessment, but I'm fairly confident in it. I'm guessing this is the end goal because when I emulated it I can see it messing with Google Chrome's IElevation COM interface (trying to dump and decrypt saved passwords). However, between this it does a bunch of other stuff too.
1. They (an unknown Threat Actor) compromised cpuid.com to deliver malware from HWMonitor. It impacts the actual installer as well as the portable installer. It downloads stuff from supp0v3-dot-com, the same domain used from a previous malware campaign targeting FileZilla in the beginning of March, 2026 initially reported by MalwareBytes.
2. HWMonitor comes packaged with a malicious CRYPTBASE.dll. CRYPTBASE.dll is a legitimate Windows library, but they made a fake one to blend in (malware masquerading). This DLL is responsible for connecting to their C2 and downloading the other malware stages.
3. It tries to detect emulation and prevent reverse engineering by checking for the presence of specific registry keys on the machine. However, they failed doing this and didn't account for everything. Notably, they only check for VirtualBox (whomp, whomp).
4. It downloads a .cs file from a remote C2 and then compiles it manually on the machine by invoking .NET stuff. This is an interesting strategy. It does all of this via Powershell (LOLBIN nonsense).
5. The .cs file it compiles is a .NET binary with NTDLL exports. The main HWMonitor binary performs process injection using this compiled .NET binary. This is an interesting strategy.
6. Almost everything it does is performed in-memory. I would have to do through this and manually bonk all of this stuff with a stick and determine precisely how it operates. However, I don't think that is necessary because at this point we know this is malware and we know it's trying to steal browser credentials.
+2 points for IElevation COM Interface credential dumping
+1 point for inline Powershell CLI DLL compilation
+1 point for .NET assembly NTDLL export proxying
-1 point for botched anti-emulation
+2 points for website compromise and supply chain attack
+1 point for memory persistence
-3 points for recycling the same C2 from March, 2026 campaign
Overall I give this malware a B-. This is pretty good malware.

English

@_konliberal ja mam 28 lat i moj max wiekowy u chlopaka to 15
Polski

@YTWestbomb I don't think match draws are something we're considering at the moment, especially considering some of the best moments on FACEIT have come from long games (donk 95 kills, for example)
English

.@FACEIT_Darwin happy easter. FUCK UNLIMITED OVERTIME. give me 2 chances then get me out. 2 HOURS FOR ONE PUG IS FUCKING STUPID
English

We are looking for a 5th player! 👹
🔺 duelist/sentinel/controller
🔺 16+
🔺 very vocal/mid-rounding/2nd caller
🔺 high availability
🔺 willing to grind and improve
🔺 long term only❗️
dm @anubis_vlr on twitter or “legitjustbad” discord

English

@formulacy @jeff45587162990 we should lowkey skin him alive for trying to defend his teammate
English

@jeff45587162990 this while defending Boo for retweeting a racist tweet that was apparently "accidental" and multiple clips of him insulting turkish people while playing ranked

English

and it's the best thing that could have happened to Valorant this year so let's keep it that way should we
statsmeister Valorant@statsmeisterVLR
He is not signed yet.... just saying
English

@tomcornishh oh hey i worked on this before i left
English

Customs are now fixed for all Epic Gamemodes and UEFN🔥
But Chris has shared some teasers of Custom Matchmaking Settings (FINALLY).
Controlling the weather, the storm, and even disabling PvP! Streamers and content creators have been asking for this for years, so it’s great that we’re finally getting these options!
Elite Tofu (Daigo Chris)@EpicTofuChris
@tomcornishh Bug. We're on it! Though while we're here, maybe we can do you one better this season 👀. @NickEh30 , your time to shine ☀️//⛈️⏸️//🔫❌
English

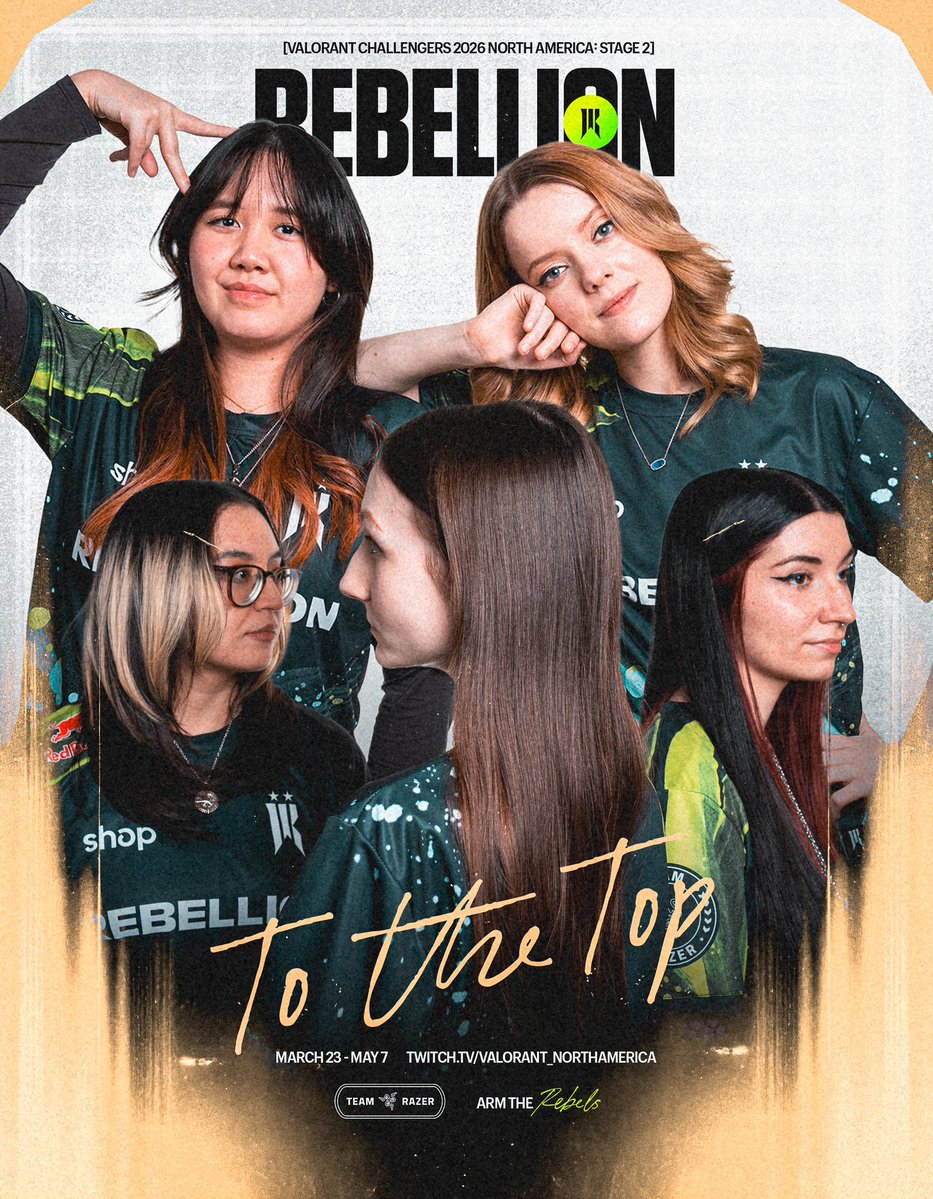
Huge kudos to @SRVAL Gold and @KRUesports Blaze for making their way into the VCT main circuit! Great inspiration for us at Riot and for all the GC players grinding day in and day out.

English