Rafał Goryl
68 posts


Rafał Goryl
@voix44er
Breaking stuff, Security researcher @pixiepointsec | Pwn2Own Toronto 2023, Tokyo 2025, Ireland 2025
Katılım Ağustos 2018
418 Takip Edilen162 Takipçiler

Confirmed! Julien COHEN‑SCALI of @FuzzingLabs targeted the Phoenix Contact CHARX SEC‑3150, chaining two vulnerabilities - an authentication bypass and privilege escalation - to earn $20,000 USD and 4 Master of Pwn points. #Pwn2Own #P2OAuto

English
Rafał Goryl retweetledi

My very first blog post is live: kiddo-pwn.github.io/blog/2025-11-3…
During research, I've run into and documented a simple universal SQLite Injection RCE trick. Enjoy!
N-day Analysis about Synology Beestation RCE (CVE-2024-50629~50631) by legendary DEVCORE 🎃 🍊
Thanks to @u1f383 @orange_8361 for original finding and allowing to post, and to @the_emmons for the invaluable references 🔥
Enjoy the Demo!
PoC: github.com/kiddo-pwn/CVE-…
English
Rafał Goryl retweetledi
Rafał Goryl retweetledi

Another successful collision: @_voix44er from PixiePoint Security succeeded in exploiting the Phillips Hue Bridge, but the bugs he used were collisions with a previous entry. He still earns $10,000 and 2 Master of Pwn points. #Pwn2Own


English
Rafał Goryl retweetledi
Rafał Goryl retweetledi

And... hot on the heels will be @voix44er attempting the Philips Hue Bridge this week! All the best and have fun!
English
Rafał Goryl retweetledi

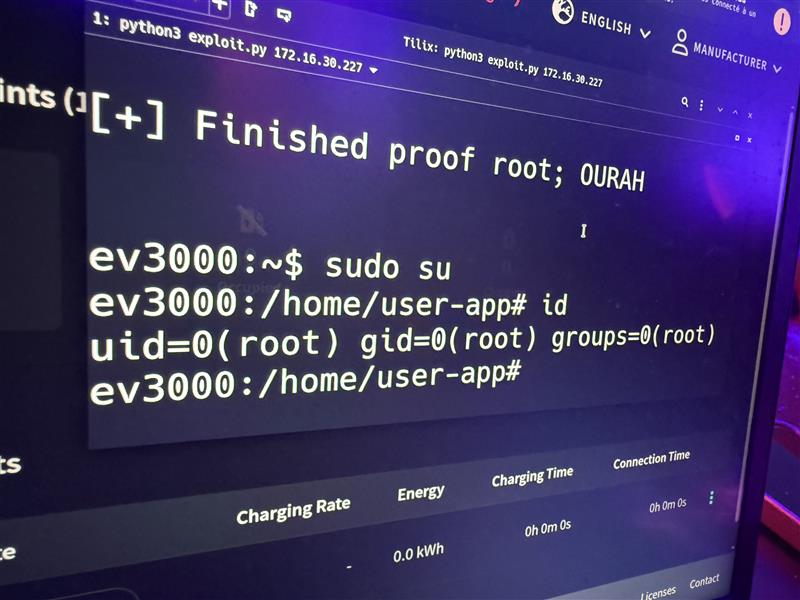
If u think that Windows research is all we do, think again! In our first IOT blog, @voix44er details the Wolfbox EV charger setup, attack surface, his #Pwn2Own Automotive 2025 bug, exploitation, and best of all, displaying our name on it (in styleee...)!
pixiepointsecurity.com/blog/pwn2own-2…
English
Rafał Goryl retweetledi

[ZDI-25-329|CVE-2025-5750] (0Day) (Pwn2Own) WOLFBOX Level 2 EV Charger tuya_svc_devos_activate_result_parse Heap-based Buffer Overflow Remote Code Execution Vulnerability (CVSS 8.8; Credit: Rafal Goryl of PixiePoint Security) zerodayinitiative.com/advisories/ZDI…
English
Rafał Goryl retweetledi

How China Is Building an Army of Hackers. With commentary from ZDI's Dustin Childs and footage from #Pwn2Own Automotive youtu.be/8kpnSb4yGR0?si… via @YouTube

YouTube
English
Rafał Goryl retweetledi

Proud to see @_jaelkoh (with @saidelike) talking about undocumented internals of KTM, the bugs and exploits in 'Hunting for Overlooked Cookies in Windows 11 KTM and Baking Exploits for Them'. No ovens required for this recipe!
offensivecon@offensive_con
2025 agenda is out! offensivecon.org/agenda/2025.ht…
English
Rafał Goryl retweetledi
Rafał Goryl retweetledi
Rafał Goryl retweetledi

Confirmed (with a collision)! Rafal Goryl of PixiePoint Security used a 2 bug chain to exploit the WOLFBOX Level 2 EV Charger, but one of the bugs was previously known. He earns himself $18,750 and 3.75 Master of Pwn points. #P2OAuto


English

And that’s a wrap! #Pwn2Own Automotive 2025 is complete. In total, we awarded $886,250 for 49 0-days over the three day competition. With 30.5 points and $222,250 awarded, Sina Kheirkhah (@SinSinology) of Summoning Team (@SummoningTeam) is our Master of Pwn. #P2OAuto

English
Rafał Goryl retweetledi

Annnddd... the odds ARE in your favor! Congrats @voix44er ! This result is just the cherry on the cake. Regardless of what it may be, what we don't see is the dedication and hard work put into the research.. 💪💪💪
TrendAI Zero Day Initiative@thezdi
Success! On his second attempt, Rafal Goryl of PixiePoint Security was able to exploit the WOLFBOX EV charger. He heads off the the disclosure room to provide us with all the details. #P2OAuto #Pwn2Own
English
Rafał Goryl retweetledi

@thezdi @dustin_childs Hey @thezdi is it still possible to register entry for Pwn2Own? As I can't get any confirmation for entry registration these past few days over email.
English

No time to read the blog? Just want the highlights? It may be 4am where he's at, but @dustin_childs is still covering patch Tuesday. Here's the Patch Report for January 2025. And stick around to the end for a sneak peak at #Pwn2Own Automotive. youtu.be/3GUMoGRRA2U

YouTube
English
Rafał Goryl retweetledi

Paged Out! Issue #5 is out now!
pagedout.institute/?page=issues.p…
Happy reading!
Please RT and tell your friends! :)
English
Rafał Goryl retweetledi

[ZDI-24-839|CVE-2024-6248] (Pwn2Own) Wyze Cam v3 Cloud Infrastructure Improper Authentication Remote Code Execution Vulnerability (CVSS 7.5; Credit: Rafal Goryl) zerodayinitiative.com/advisories/ZDI…
English
Rafał Goryl retweetledi