Wintermute
250 posts


Your microservices architecture implements OAuth 2.0 for authentication, but you're facing challenges propagating the OAuth token through internal service-to-service calls, leading to unauthorized requests.
How would you redesign the security architecture to propagate authentication tokens across internal services?
English
Wintermute retweetledi

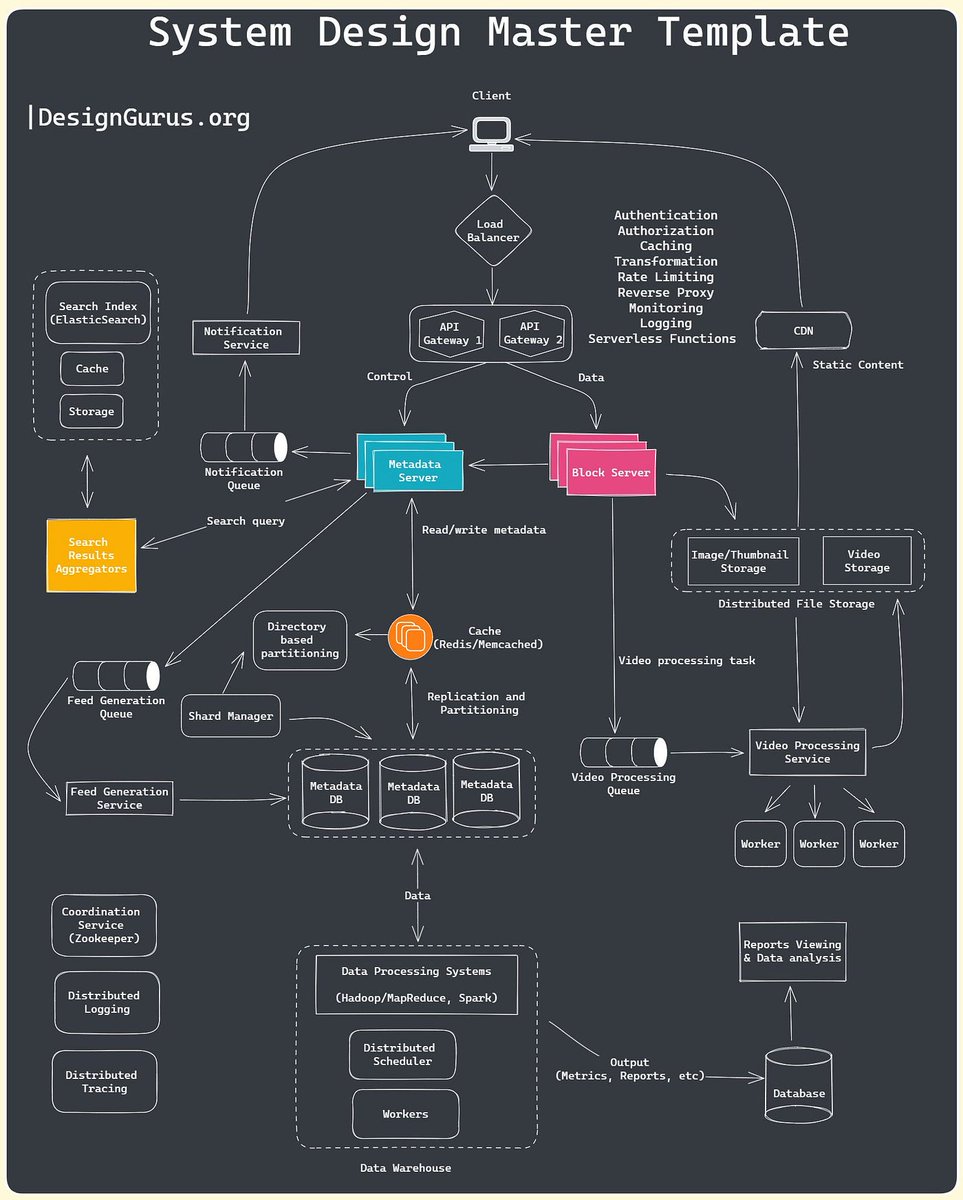
10 Best System design Topics for interviews
1. Caching
2. DB Sharding
3. load-balancing
4. replication
5. fault-tolerance
6. high-availability
7. Performance
8. scalability
9. Performance
10. Indexing
learn more on DesignGuru - bit.ly/3pMiO8g
English
Wintermute retweetledi

Top 12 Tips for API Security
- Use HTTPS
- Use OAuth2
- Use WebAuthn
- Use Leveled API Keys
- Authorization
- Rate Limiting
- API Versioning
- Whitelisting
- Check OWASP API Security Risks
- Use API Gateway
- Error Handling
- Input Validation
–
Subscribe to our weekly newsletter to get a Free System Design PDF (158 pages): bit.ly/3KCnWXq

English
Wintermute retweetledi

I have created a GitHub repository to help you learn system design weeks ago.
And it received 400+ stars on GitHub.
I've added many case studies to make it easy for you
It gives you:
- System design interview tips
- System design fundamentals
repo - github.com/javabuddy/best…

English
Wintermute retweetledi

⚗️ localtoast
Localtoast is a scanner for running security-related configuration checks such as CIS benchmarks in an easily configurable manner.
github.com/google/localto…
English
Wintermute retweetledi

📺 @defcon 2023 videos posted!
Watch all of the 96 main stage talks for free
You can also see some of the village talks here:
@DEFCONConference/playlists" target="_blank" rel="nofollow noopener">youtube.com/@DEFCONConfere…
youtube.com/watch?v=1JT_lT…

YouTube

English
Wintermute retweetledi

My recommended materials for cracking your next technical interview:
Coding
- Leetcode
- Cracking the coding interview book
- Neetcode
System Design Interview
- System Design Interview book 1, 2 by Alex Xu
- Grokking the system design by Design Guru
- Design Data-intensive Application book
Behavioral interview
- Tech Interview Handbook (Github repo)
- A Life Engineered (YT)
- STAR method (general method)
OOD Interview
- Interviewready
- OOD by educative
- Head First Design Patterns Book
Mock interviews
- Interviewingio
- Pramp
- Meetapro
Apply for Jobs
- Linkedin
- Monster
- Indeed
Over to you: What is your favorite interview prep material?
–
Subscribe to our weekly newsletter to get a Free System Design PDF (158 pages): bit.ly/3KCnWXq
English
Wintermute retweetledi

OAuth 2.0 Flows
Authorization Code Flow: The most common OAuth flow. After user authentication, the client receives an authorization code and exchanges it for an access token and refresh token.
Client Credentials Flow: Designed for single-page applications. The access token is returned directly to the client without an intermediate authorization code.
Implicit Code Flow: Designed for single-page applications. The access token is returned directly to the client without an intermediate authorization code.
Resource Owner Password Grant Flow: Allows users to provide their username and password directly to the client, which then exchanges them for an access token.
Over to you - So which one do you think is something that you should use next in your application?
–
Subscribe to our weekly newsletter to get a Free System Design PDF (158 pages): bit.ly/3KCnWXq

English
Wintermute retweetledi

I’ve been using jswzl.io for the last month. If you reverse engineer JavaScript this is a must have tool. @CharlieEriksen has done an excellent job.
English
Wintermute retweetledi
I’m proud to present ProtoBurp, a new Burp Suite extension to help encode and fuzz Protobuf messages based on pain points with existing tooling.
Check out my latest blog post about it! dillonfrankesecurity.com/posts/protobur…
#pentesting #burpsuite #protobuf #offsec
English
Wintermute retweetledi

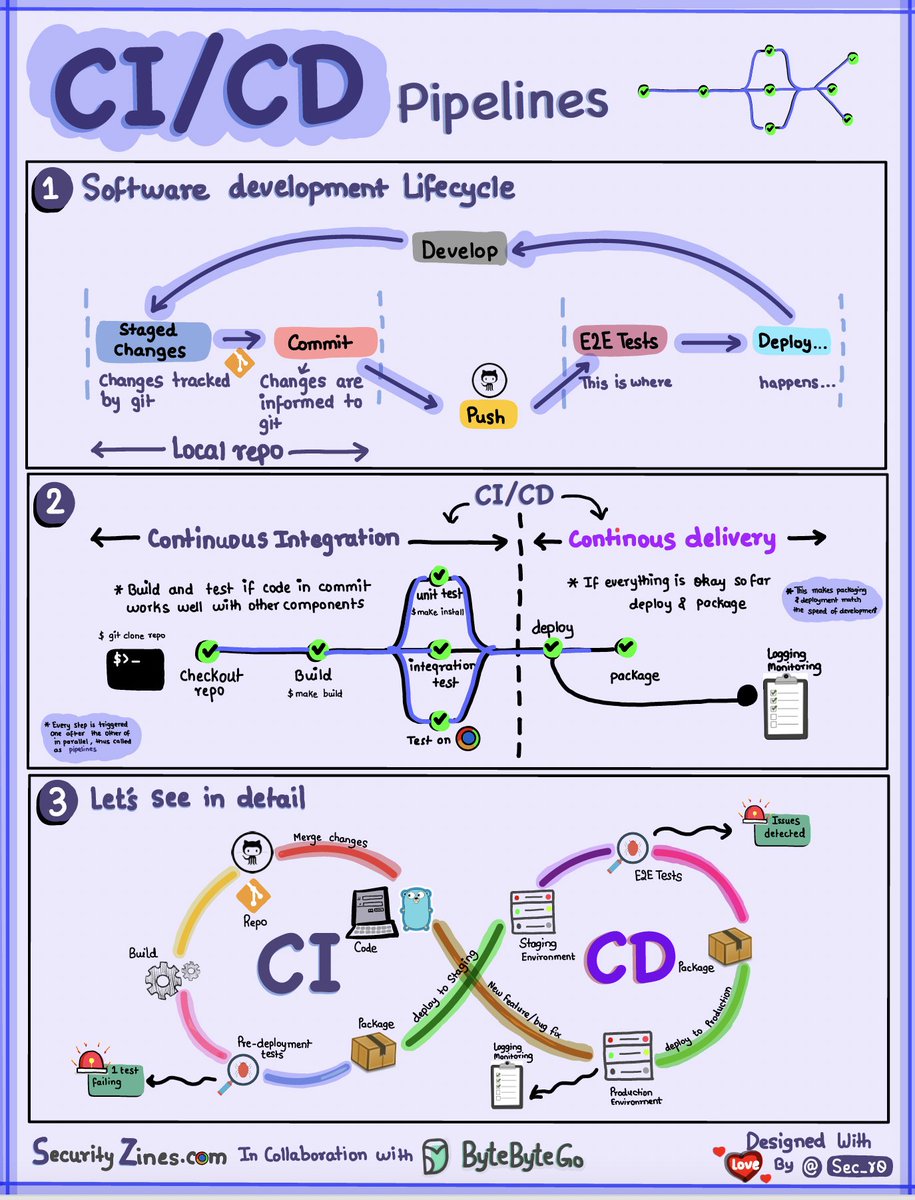
CI/CD Pipeline Explained to Kids
Section 1 - SDLC with CI/CD
The software development life cycle (SDLC) consists of several key stages: development, testing, deployment, and maintenance. CI/CD automates and integrates these stages to enable faster, more reliable releases.
When code is pushed to a git repository, it triggers an automated build and test process. End-to-end (e2e) test cases are run to validate the code. If tests pass, the code can be automatically deployed to staging/production. If issues are found, the code is sent back to development for bug fixing. This automation provides fast feedback to developers and reduces risk of bugs in production.
Section 2 - Difference between CI and CD
Continuous Integration (CI) automates the build, test, and merge process. It runs tests whenever code is committed to detect integration issues early. This encourages frequent code commits and rapid feedback.
Continuous Delivery (CD) automates release processes like infrastructure changes and deployment. It ensures software can be released reliably at any time through automated workflows. CD may also automate the manual testing and approval steps required before production deployment.
Section 3 - CI/CD Pipeline
A typical CI/CD pipeline has several connected stages:
- Developer commits code changes to source control
- CI server detects changes and triggers build
- Code is compiled, tested (unit, integration tests)
- Test results reported to developer
- On success, artifacts are deployed to staging environments
- Further testing may be done on staging before release
- CD system deploys approved changes to production
–
Subscribe to our weekly newsletter to get a Free System Design PDF (158 pages): bit.ly/42Ex9oZ
English
Wintermute retweetledi

⚗️ github-actions-goat
Deliberately Vulnerable GitHub Actions CI/CD Environment.
github.com/step-security/…
English
Wintermute retweetledi

☁️ How to get rid of AWS access keys: Replacing the authentication
@0xdabbad00 discusses alternative solutions to using access keys
→ OpenID Connect for other clouds
→ IAM Roles Anywhere or Systems Manager Hybrid Activation for on-prem
wiz.io/blog/how-to-ge…
English
Wintermute retweetledi

As a developer, you may feel pressure to learn new things all the time.
And while it's good to stay on top of things, don't forget about the fundamentals.
In this guide, @tamerlan_dev lays out the key CS concepts you should know – and how to learn them.
freecodecamp.org/news/what-ever…
English
Wintermute retweetledi

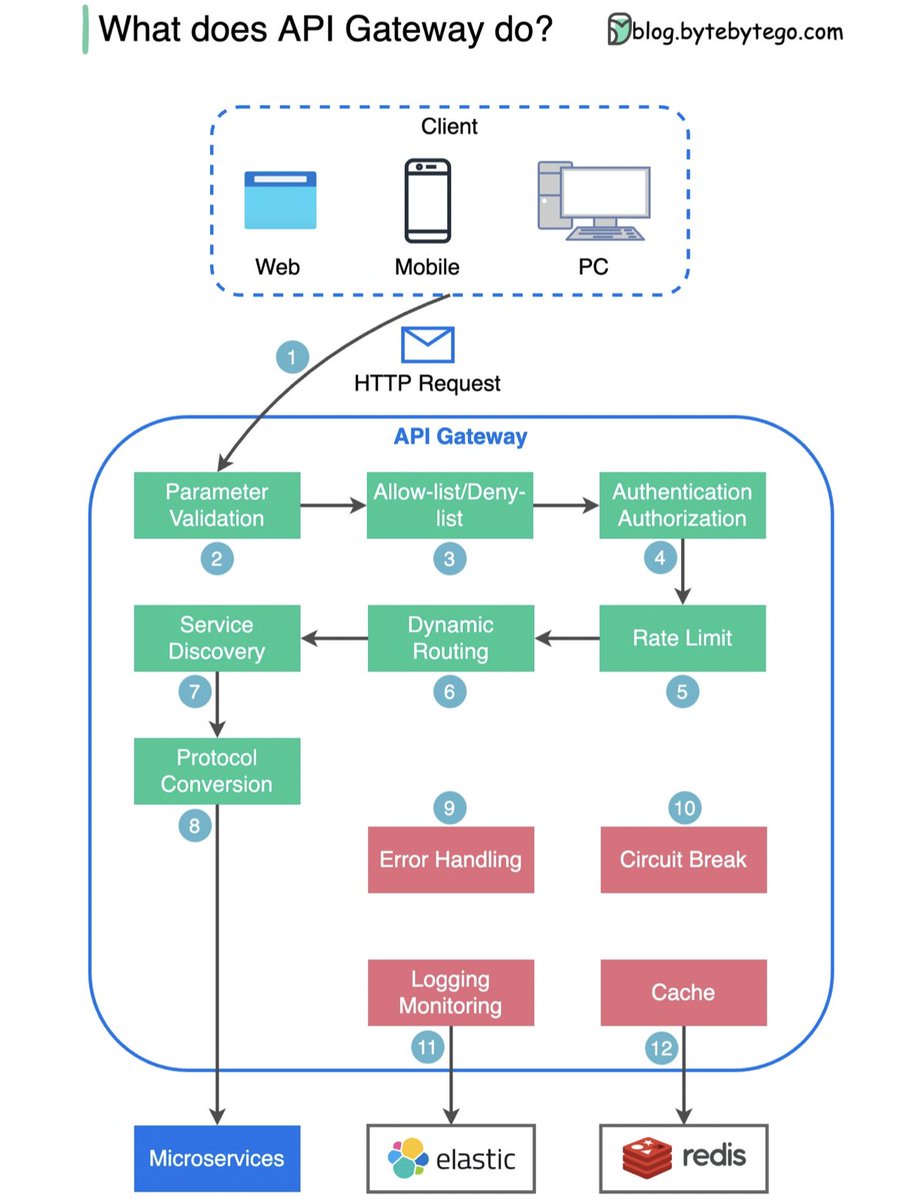
What does API gateway do?
The diagram below shows the detail.
Step 1 - The client sends an HTTP request to the API gateway.
Step 2 - The API gateway parses and validates the attributes in the HTTP request.
Step 3 - The API gateway performs allow-list/deny-list checks.
Step 4 - The API gateway talks to an identity provider for authentication and authorization.
Step 5 - The rate limiting rules are applied to the request. If it is over the limit, the request is rejected.
Steps 6 and 7 - Now that the request has passed basic checks, the API gateway finds the relevant service to route to by path matching.
Step 8 - The API gateway transforms the request into the appropriate protocol and sends it to backend microservices.
Steps 9-12: The API gateway can handle errors properly, and deals with faults if the error takes a longer time to recover (circuit break). It can also leverage ELK (Elastic-Logstash-Kibana) stack for logging and monitoring. We sometimes cache data in the API gateway.
Over to you: 1) What’s the difference between a load balancer and an API gateway?
2) Do we need to use different API gateways for PC, mobile and browser separately?
—
Subscribe to our weekly newsletter to get a Free System Design PDF (158 pages): bit.ly/42Ex9oZ
English
Wintermute retweetledi
Wintermute retweetledi

Building a Login System with Python Flask and MySQL for Beginners
#python #mysql
morioh.com/p/c61187faa9be…
English
Wintermute retweetledi

📈 Modernizing Secrets Scanning: Part 2–the Semantic Eureka
Secrets detection approaches that rely on known structure or high entropy are fundamentally limited
Nikolai found a code-aware tool improved their detection rate 200%, reduced noise
hackernoon.com/modernizing-se…
English
Wintermute retweetledi

🧑🎓 Security Study Plan
A complete practical study plan to become a successful security professional in:
* Pen testing
* AppSec
* Cloud Security
* DevSecOps
and more
By @jassics
github.com/jassics/securi…
English
Wintermute retweetledi

🔥 Introducing Cloudfoxable
A gamified cloud hacking sandbox to learn AWS #pentesting
Scenarios based on real cloud pen tests
Flags to reward you for finding new entry points & lateral movement paths
By @sethsec
bishopfox.com/blog/cloudfoxa…
English