0xfran6(🍊,💊)
11.1K posts

0xfran6(🍊,💊)
@yeabor
IT Support Engineer and Crypto Enthusiast



10x volume boost on @risextrade (3 days to go) today, i came across an article on how to use @tread_fi’s market maker bot to generate volume on Risex. before that, i had already spent most of the day experimenting with the bot myself. fun fact: it’s actually good and very convenient, but also pretty expensive, at least in my opinion. still, i’m making another deposit right now with the intention of burning through about 50% of it chasing volume. if things go well, i might even close the hunt in positive pnl. link to article if interested: x.com/og_branxi/stat… wish me luck, amigos.


the subtle art of depositing on @risextrade gut feeling; good things are coming




Introducing Agent Payments Protocol (APP) - the open standard for agent commerce, built for every chain. For the first time, agents can move beyond payments to full-scale commerce: including drafting quotes, hiring specialists, escrowing funds, resolving disputes & more. 🧵👇


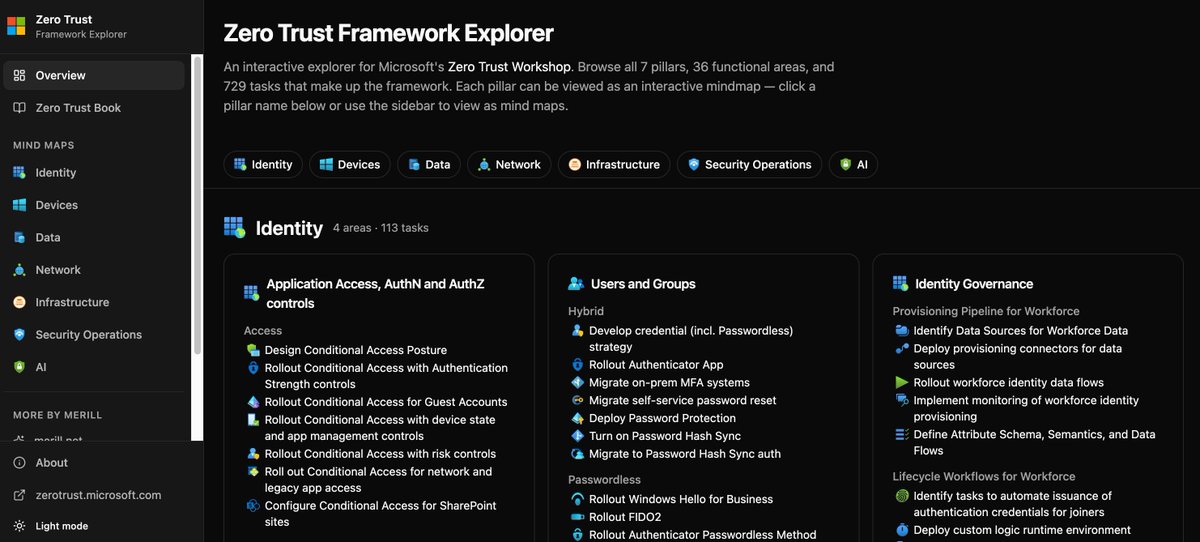
Entra Hardening Tip #6: Kill Standing Access 🔐 Admin accounts are the ultimate target. If these accounts stay active 24/7, you're leaving a door open for attackers to disable policies, create identities + credentials and hide in your tenant. To harden Microsoft Entra, you need Zero Standing Access. ⏰ Just-In-Time (JIT) Access Stop using permanent role assignments. Use Privileged Identity Management (PIM) so roles are only active when they are actually being used. This limits the time an attacker has to exploit a compromised account. 👥 The Second Admin Rule Don't let a single user activate a high-risk role alone. Require a second admin to approve the request. This forces an attacker to compromise two accounts to get anywhere. This "two-key" system breaks the attack chain and creates logs that are much easier to monitor. Checklist: ✅ Use PIM: Move your admins from "Permanent" to "Eligible." ✅ Log Justifications: Every activation needs a business reason. ✅ Enforce Approvals: Require a second admin for high privileged roles. ✅ Audit Often: Use Entra ID Governance to ensure access is still necessary. If they can't get the time or the second approval, they can't get to your data.







🔥🤖 M365 Connector for Claude – Why SecOps Must Care Monitoring the M365 Connector for Claude is critical because when ResultType=0, it means an Entra Global Admin has granted permissions, enabling Claude to directly access SharePoint, OneDrive, Outlook, and Teams—a governance decision with major security implications that SecOps must track closely. Meanwhile, ResultType=90095 shows end users attempting to use the connector without the admin grant, signaling demand, shadow IT risk, and adoption pressure. By watching both signals, defenders gain visibility into where governance decisions meet user behavior, ensuring connector risks are managed before they escalate. KQL Code: github.com/SlimKQL/Detect… #Cybersecurity #M365ConnectorClaude #Entra #Governance