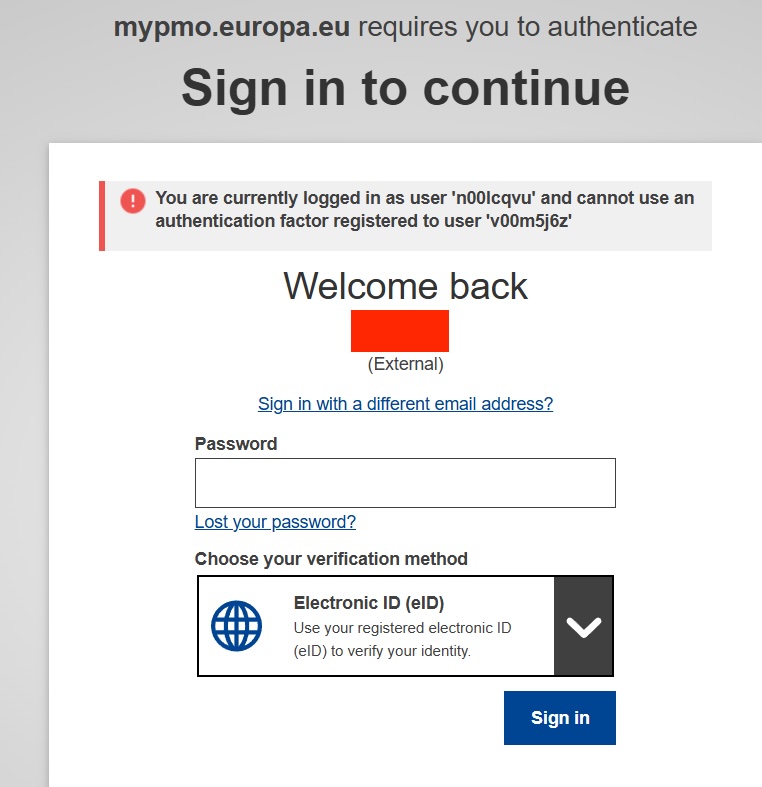
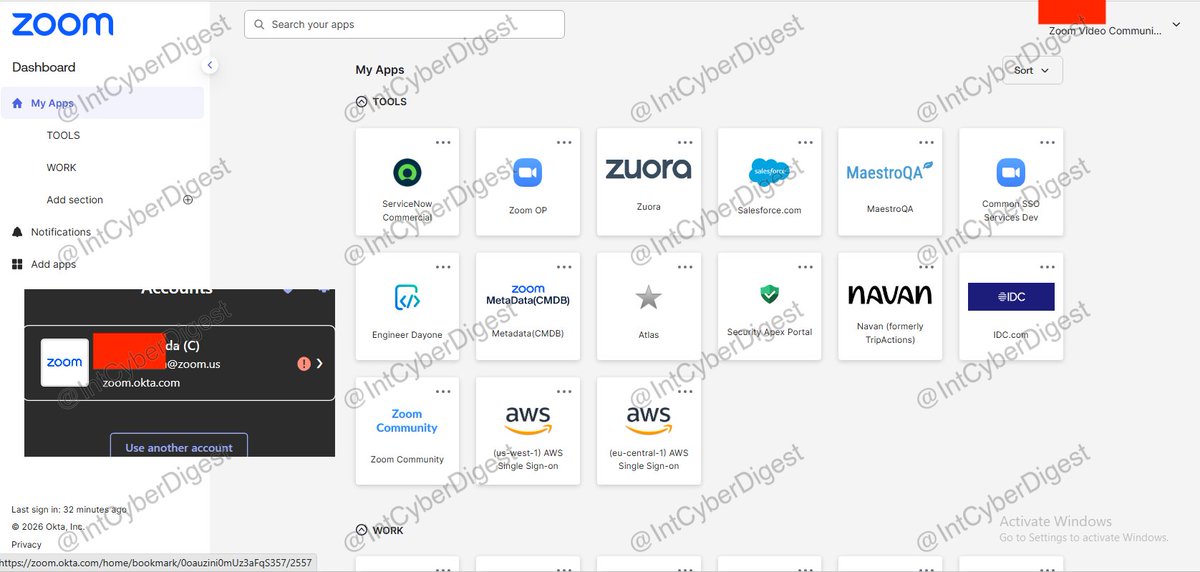
The next wave of KYC will not ask who you are. It will prove it, privately. @zkyctech has joined the @zkPass Verifiable Application Acceleration Program (VAAP) to redefine what trust means in identity verification. Built on zkTLS, zKYC turns traditional KYC into a privacy-preserving proof - verifiable across ecosystems while keeping every piece of personal data untouched. No intermediaries. No exposure. Only cryptographic truth. The Verifiable Internet begins with verifiable identity.