Art Manion
1.4K posts









In America, TikTok pushes videos to kids that promote self-harm, eating disorders, and suicide. In China, the version of TikTok available there, the app shows young kids science experiments, museum exhibits, and other educational material.



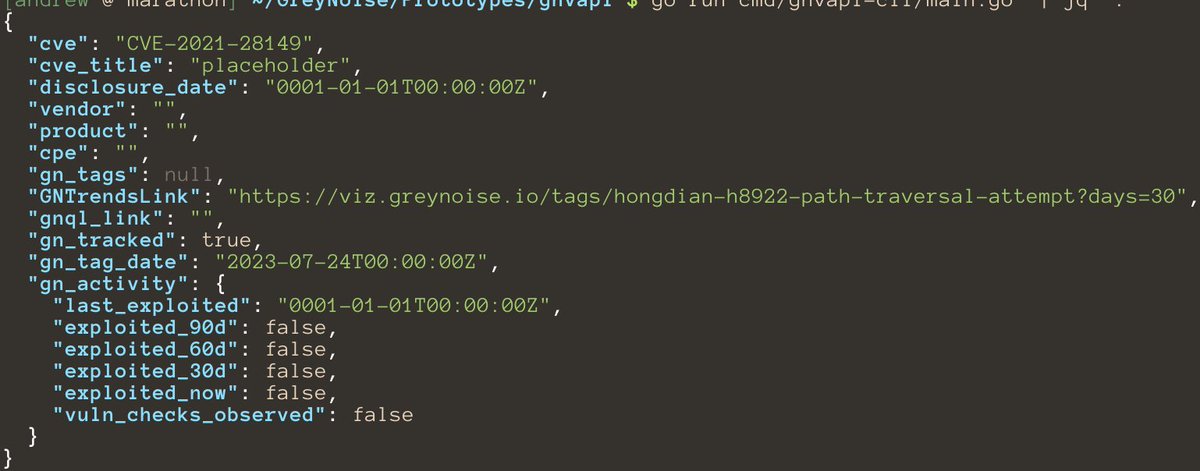
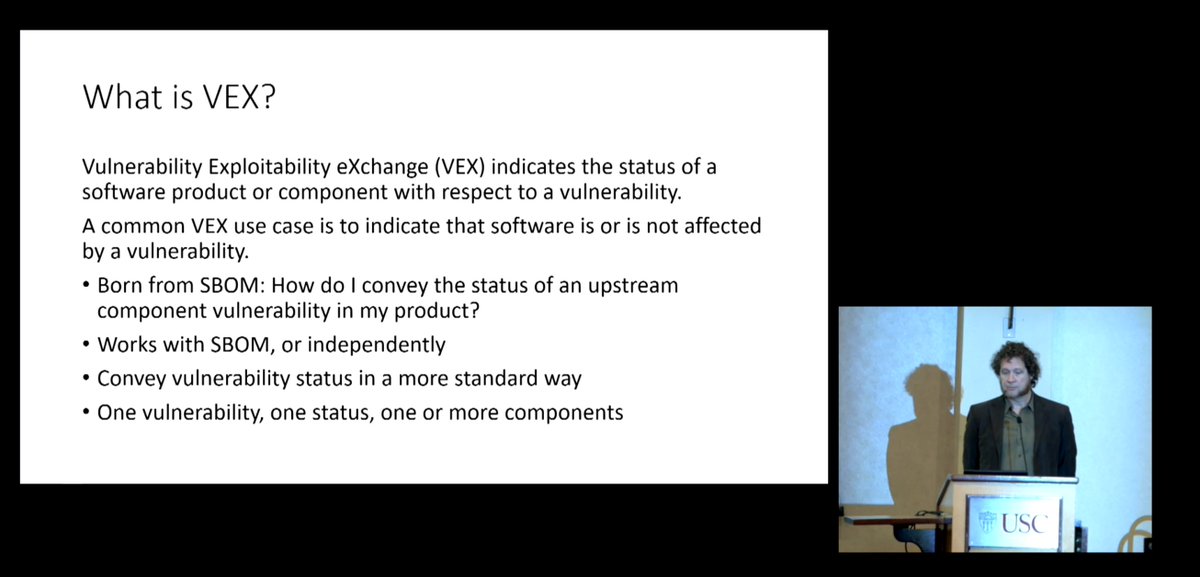
The question "I have an #SBOM. Now what?" is a legitimate one, and more tools and use cases emerge every day. But this basic analysis from @GossiTheDog on what's in Avanti tells a pretty clear story of why we need transparency for our software NOW.



@fortraofficial @Horizon3ai @stephenfewer Looking into the fix for CVE-2024-0204 and it's clear that the root issue is the path traversal "/..;/" -- this was not fixed in GoAnywhere MFT 7.4.1. However, it does appear to be fixed in 7.4.2, though another silent fix. Any CVE yet?


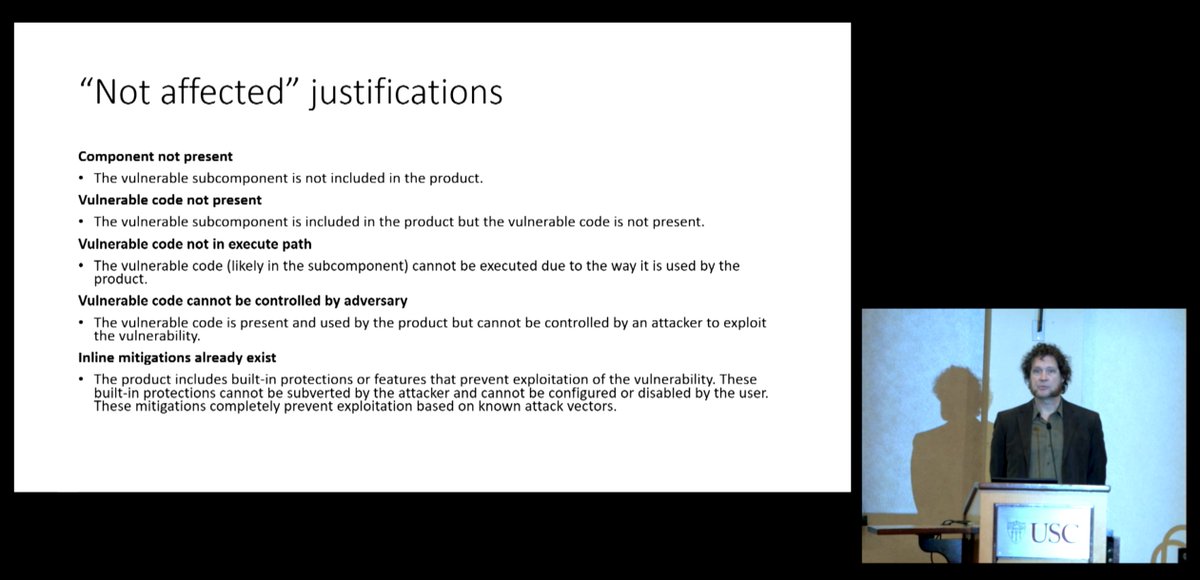
'Buyers evaluating the risks associated with those components require information not typically included within the SBOM, so external enrichment is needed. 'The inability or unwillingness to supply an SBOM should be considered a significant warning'.