Pascal Obiwumma
5.3K posts


Pascal Obiwumma
@Pascal_FTM
Frontend Dev || Fullstack Soon || JavaScript || Crypto Futures Trader || ICT || »»Building My Portfolio. Got any ideas? DM««

Let’s see a photo of your workspace👨🏽💻💫





Na me be Merlin today Still my day +1 Man don de old wetin no good

@namjoon_hottie Nigerian men home and abroad all have the tendency to commit rape. The ones who have not done it yet just haven’t gotten the opportunity. Gosh Nigeria is a zoo!!! Just look at them🤦🏽♀️. This is so heartbreaking. Not one man stopped them!




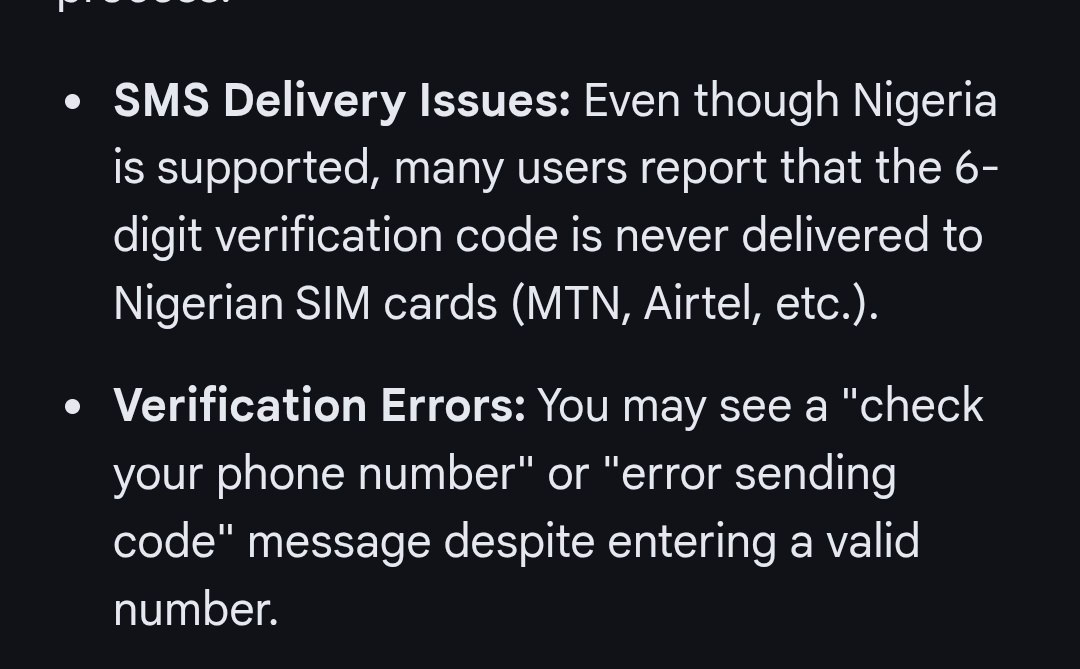
is it only me getting this? cus I don't understand anymore

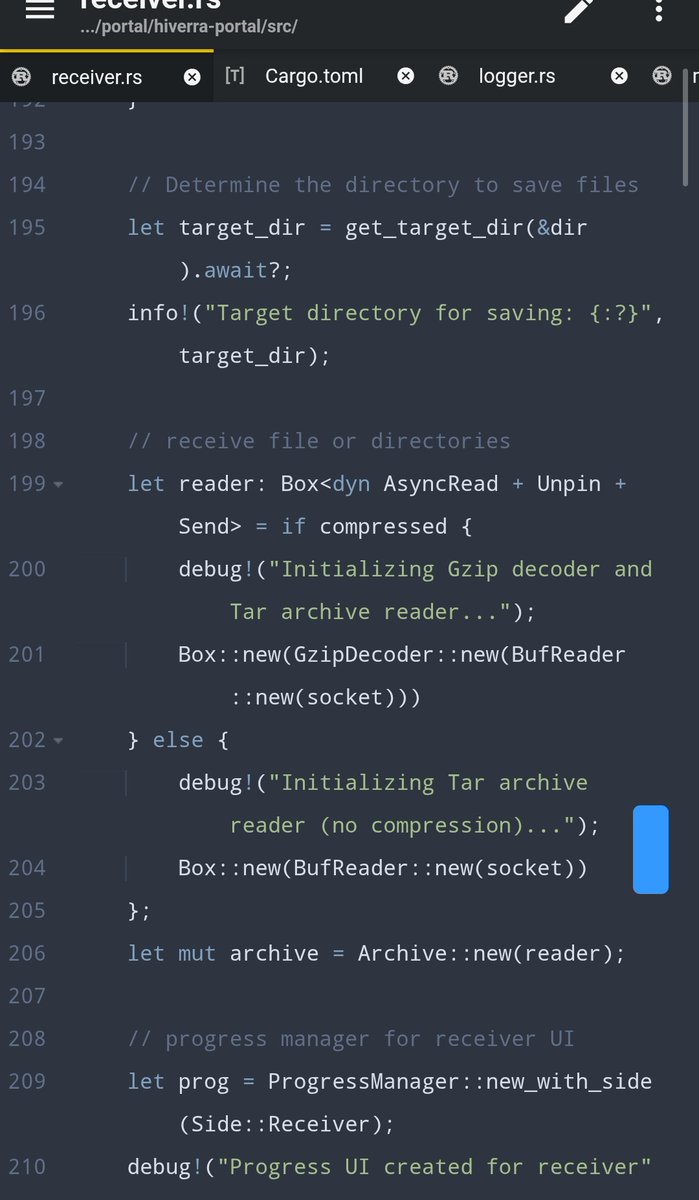
Day 49 despite how I felt I didnt do much today touched three codebase nextjs , rust, vitejs i need to get a paying gig

#day4 mastering Japanese. Learning is slow but it's better than a NO GM, fellas 👋


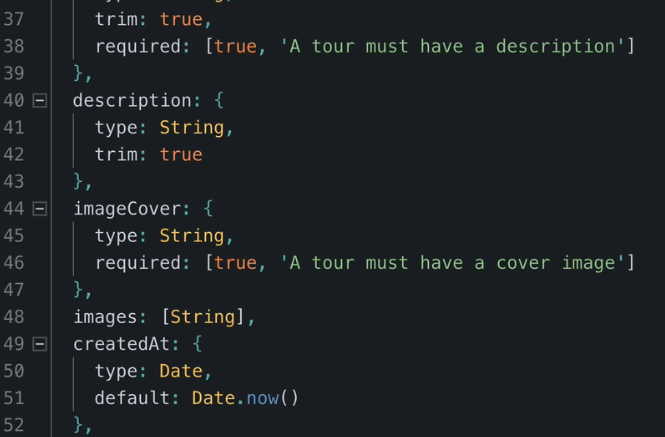
Day 44 Adding filtering methods Basic filtering: When a user hits /api/v1/tours?difficulty=easy&duration=5, Express captures these in req.query. Advanced Filtering (Operators): We use a Regular Expression to find the keywords (gte, gt), swap them for the MongoDB versions.

Day 42 Some good learning done today Performing CRUD operations with mongoose I learnt how to use query methods (FindById, findByIdAndUpdate etc.. ) to perform operations in a DB