Lol. @HackenProof a reputable bug bounty platform sends out invites for their program to attack Russian critical infrastructure (SCADA, banks, energy). Crazy times & Happy hunting. #StandingWithUkraine hackenproof.com/ukraine-will-w…
English
Jens Müller
228 posts


@jensvoid
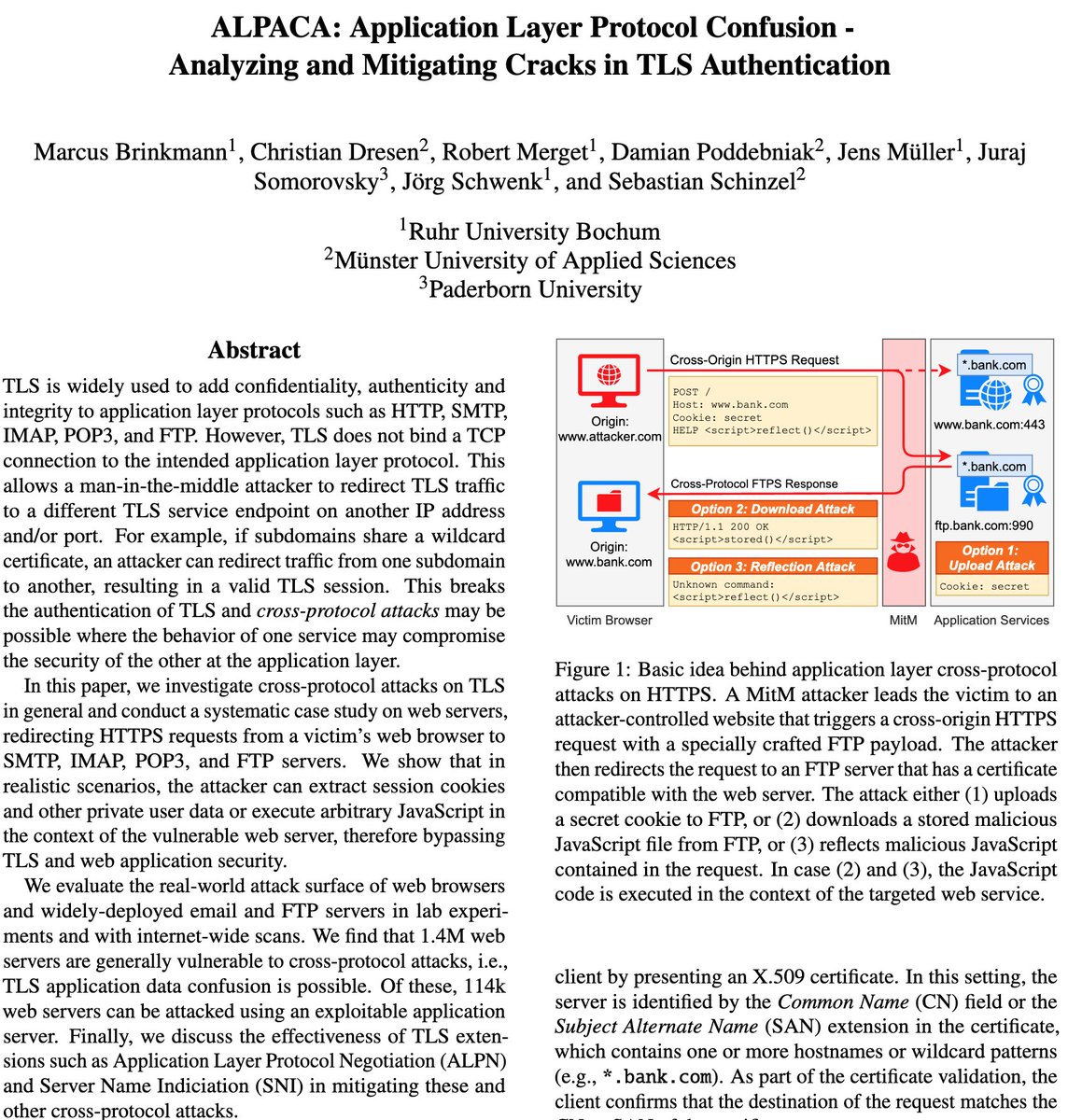
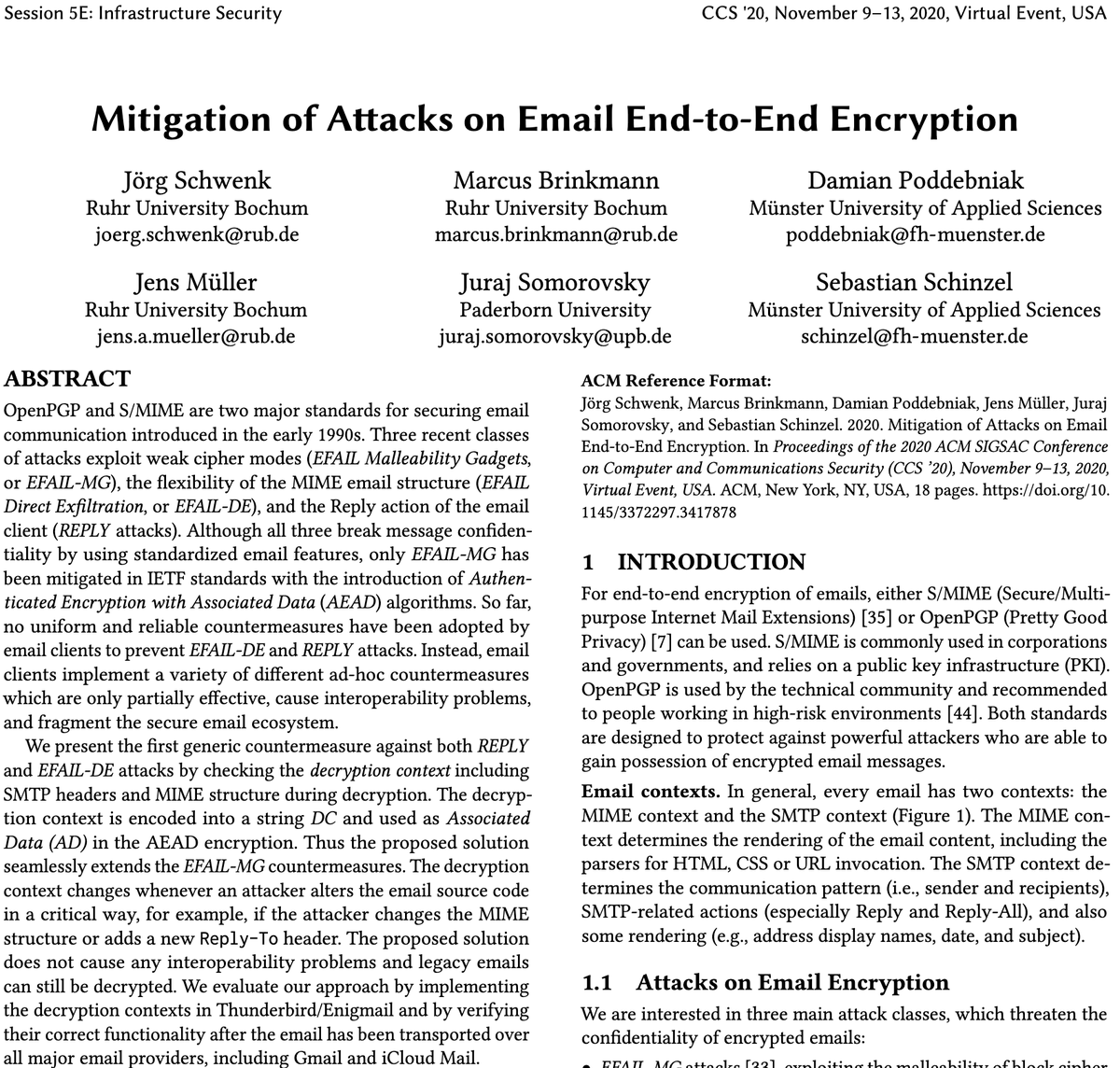
Hack the Planet! On a #yolo trip around the word during a pandemic. Involved in https://t.co/UATbdfU5vH, #efail, #pdfex. Raw tech. No chit-chat.