itsme
373 posts



Stop tweeting for a hot minute and update your Codex App to find full browser use, global dictation, non-dev mode, a new auto-review mode that is much safer than yolo, in-app docs and PDF viewer, and ... GPT-5.5.


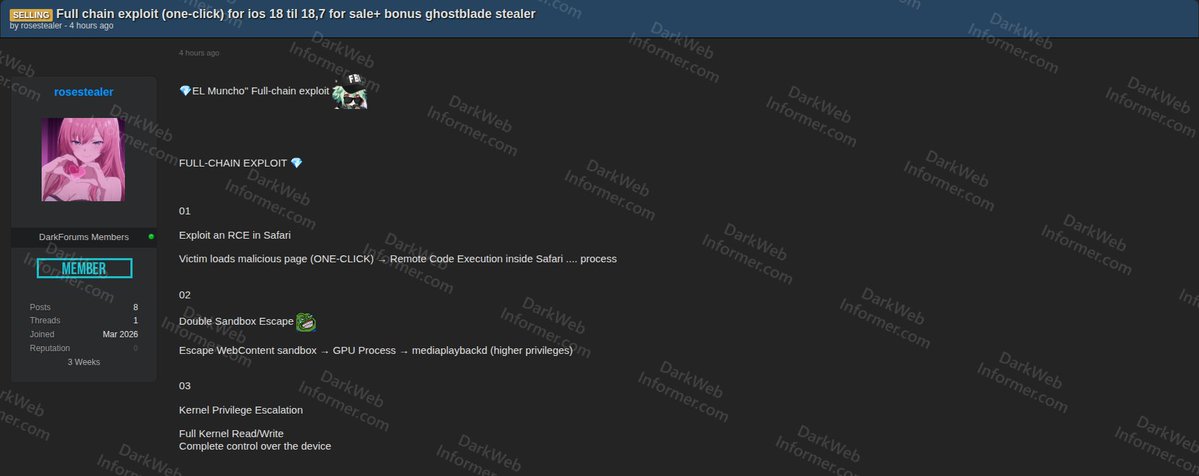
"Mythos and National Power" - This is definitely worth listening to. I'm an old school security person, so my threat models are always dominated by the assumption that attackers already have knowledge of a systems vulnerabilities. chinatalk.media/p/mythos-and-n… 1/n


That’s true, but not every company can realistically afford security by default. The real shift is that, before Mythos and similar players, the assumption was that, economically, these exploits would only be used against high-value targets. That assumption has now fundamentally changed.

Season 4 Ep8: Corner Boys Rewind to #TheWire 24th anniversary







Genians Security Center uncovers an APT37 campaign that used social networking as an initial access vector. Two Facebook accounts set to North Korea-linked locations were used to screen targets, build trust, and move conversations to Messenger. genians.co.kr/en/blog/threat…




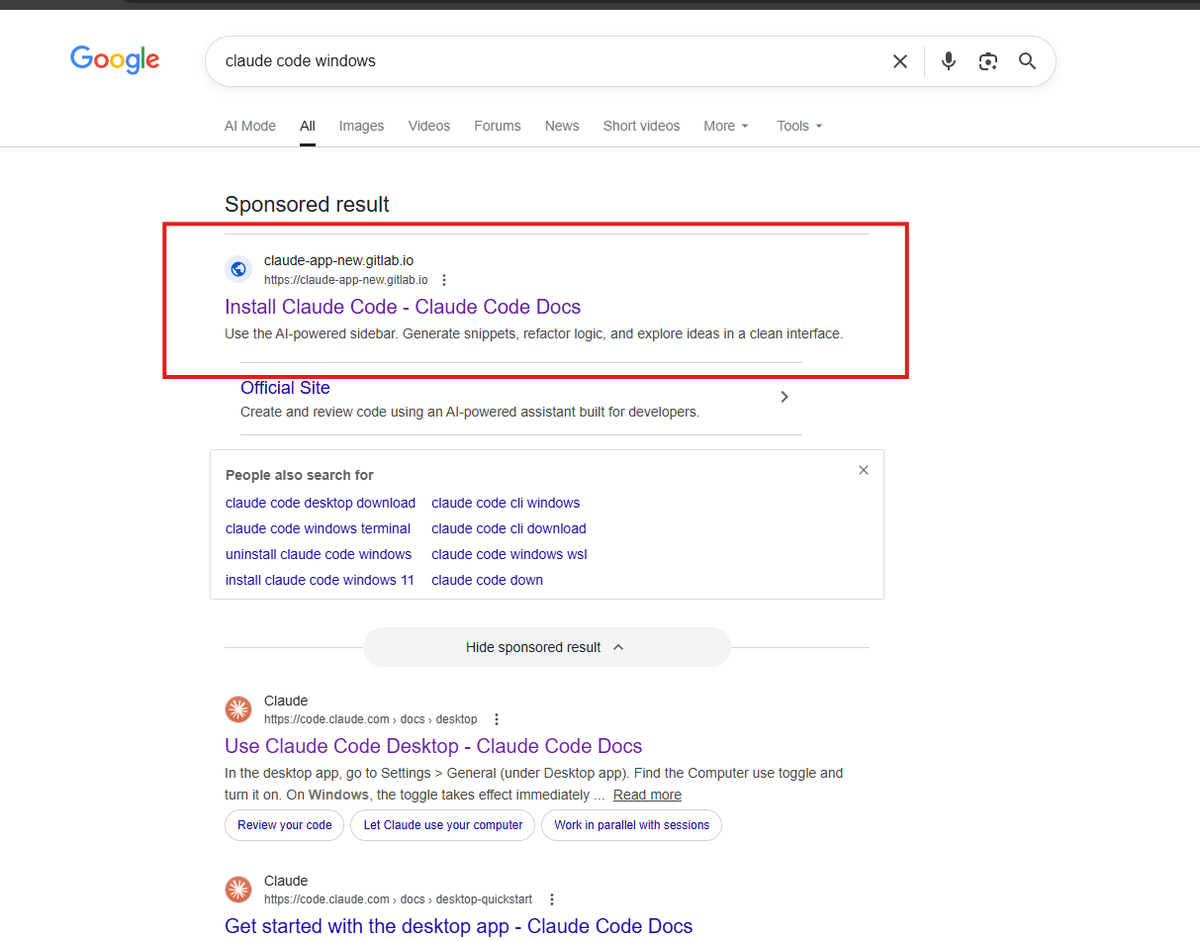
Anthropic will say whatever it takes to stay in the headlines. Claude Mythos claims “thousands of vulnerabilities” off just ~198 reviewed cases • only ~198 reports actually reviewed • “thousands” comes from extrapolation • some bugs weren’t even practical to exploit • some were already patched • others blocked by basic defense layers it's all marketing gimmick now.


🚨 BREAKING: The FBI has successfully extracted deleted Signal messages from a suspect's iPhone via notification storage, the place where all your notifications are stored for up to one month. Notification storage stores data from all messaging apps, it's a big flaw in iOS. But there's a way to turn it off...

🚨 BREAKING: The FBI has successfully extracted deleted Signal messages from a suspect's iPhone via notification storage, the place where all your notifications are stored for up to one month. Notification storage stores data from all messaging apps, it's a big flaw in iOS. But there's a way to turn it off...

We’re updating our ChatGPT Pro and Plus subscriptions to better support the growing use of Codex. We’re introducing a new $100/month Pro tier. This new tier offers 5x more Codex usage than Plus and is best for longer, high-effort Codex sessions. In ChatGPT, this new Pro tier still offers access to all Pro features, including the exclusive Pro model and unlimited access to Instant and Thinking models. To celebrate the launch, we’re increasing Codex usage for a limited time through May 31st so that Pro $100 subscribers get up to 10x usage of ChatGPT Plus on Codex to build your most ambitious ideas.