Br*an
16.3K posts

Br*an
@SecurityCollins
☁️ security, general technology fan • opinions = mine


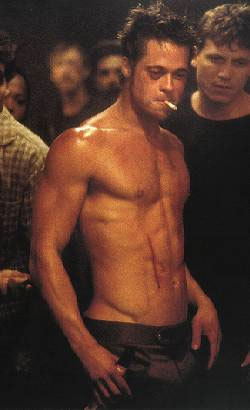
🚨 “I Pushed him TWICE... Then He Kicked the Crap Out of Me" – Neighbor Breaks Silence on Viral Beatdown Ronnie Taylor, the guy "Reacher" star Alan Ritchson beat up explains how the fight started in the first place. “I did push him because he was coming towards me on his bike. He did it again a second time. I pushed him a second time, then he got off his bike and kicked the crap out of me.”




Here is Jay Leno driving the new redesigned @Tesla Semi. He is the first person outside of Tesla to drive it. @danWpriestley: "This truck from an energy standpoint is 50% cheaper to run here in California. Across the US, we're 20% cheaper on a per mile basis, and that's inclusive of everything, not just energy, whether that's reduced maintenance, fuel." via @LenosGarage