Pierre ретвитнул

New logo. New website. Same DFIR Report team. 🔎
Check out the incredible analysts behind the research:
thedfirreport.com/company/analys…
English
Pierre
71 posts


@pigerlin
Analyst @TheDFIRReport | Passionate about all things DFIR 🇳🇱


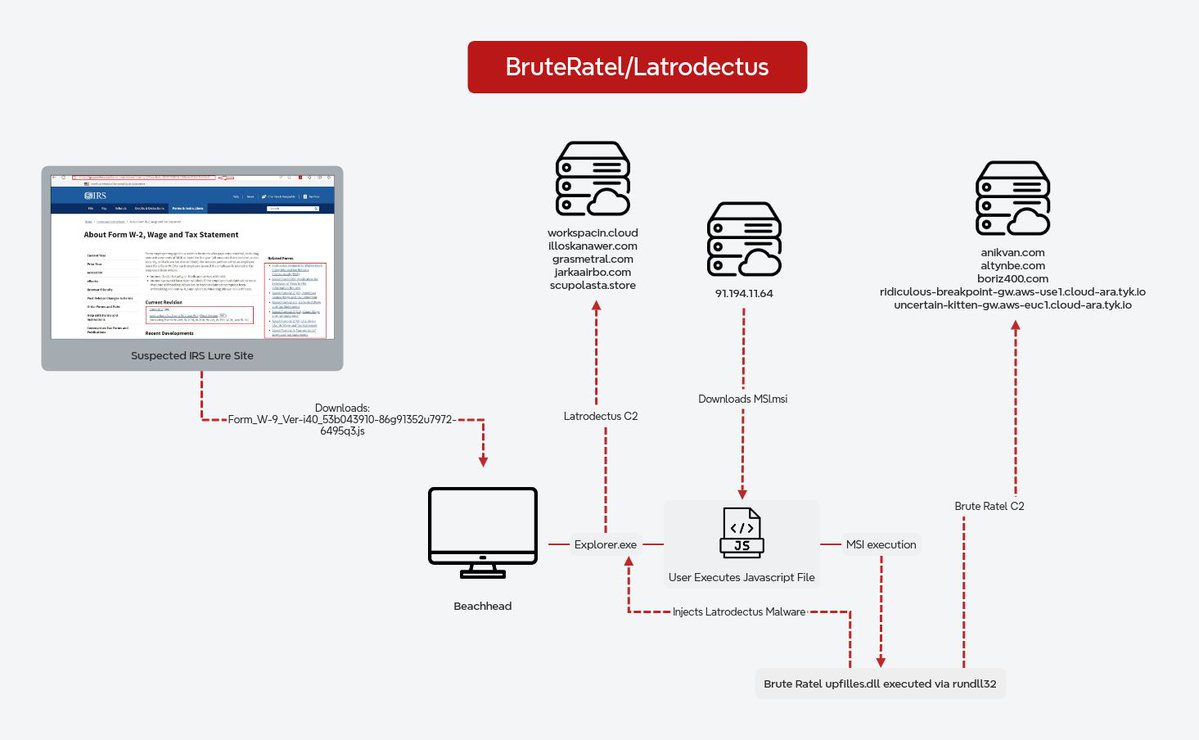














BumbleBee Roasts Its Way to Domain Admin ➡️Initial Access: BumbleBee (zipped ISO /w LNK+DLL) ➡️Persistence: AnyDesk ➡️Discovery: VulnRecon, Seatbelt, AdFind, etc. ➡️Credentials: Kerberoast, comsvcs.dll, ProcDump ➡️C2: BumbleBee, CobaltStrike, AnyDesk thedfirreport.com/2022/08/08/bum…








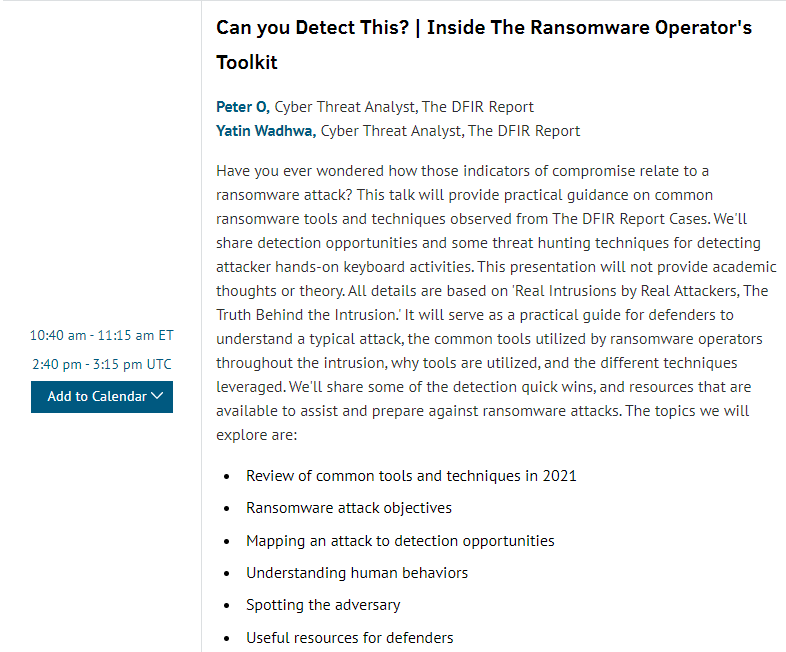
Have you registered for the free #RansomwareSummit It is going to be awesome! I had the privilege of working with speakers for 2 different talks and so excited for them. One is from @TheDFIRReport which you all know I am a huge fan of. #ransomware sans.org/cyber-security…