Dexaran
1.2K posts


Dexaran
@Dexaran
#Pseudonymous smartcontract developer & security engineer Founder of https://t.co/gggSQaclP3, EthereumCommonwealth & https://t.co/meZKAfcdwG Author of #ERC223






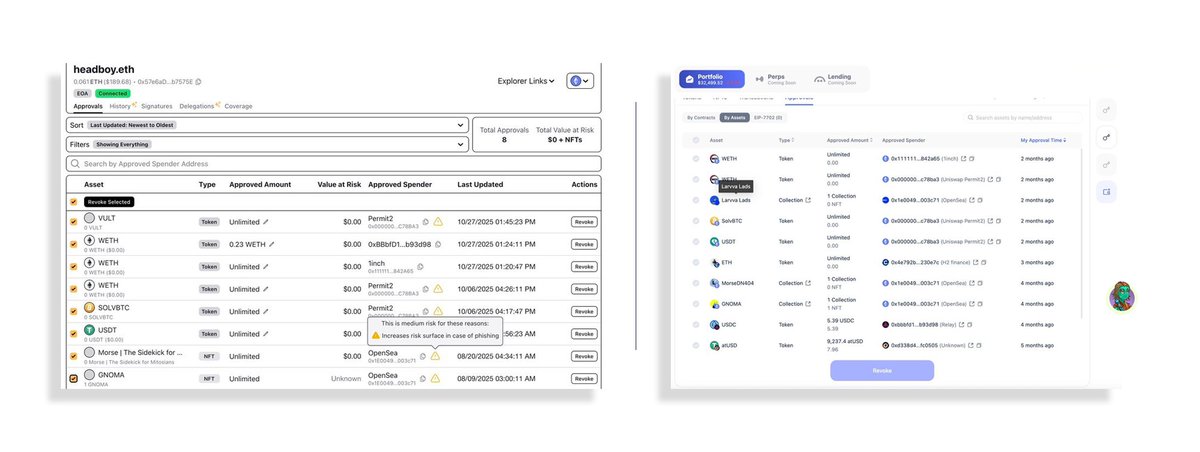
Last night around 5pm I sat down to do some work. I opened my Rabby wallet to try out Espresso's new cross-chain mint product, Presto, that Rarible had just put live on mainnet. When I opened my wallet, I immediately saw that $30k was missing...




Last night around 5pm I sat down to do some work. I opened my Rabby wallet to try out Espresso's new cross-chain mint product, Presto, that Rarible had just put live on mainnet. When I opened my wallet, I immediately saw that $30k was missing...




this is so f*cking scary - a txn made 9 months ago to transfer just $5 ended up causing a $30K loss. TLDR: → a txn was approved 9 months ago → to interact with the ThirdWeb Universal Bridge → Infinite approval was given (just for a $5 transfer) → a vulnerability in the contract was discovered in April → but the contract remained active onchain, including the blog referencing the affected contract address → vulnerability allowed anyone to drain funds from users with infinite approval → the hacker waited 9 months for the user to deposit a substantial amount → And boom - $30K gone in a single txn → funds were sent to Railgun, so can’t be traced → thirdWeb permanently disabled the legacy affected contract after the hack was disclosed → the blog referencing the affected (now-disabled) contract address is still live I don’t even know whom to blame here. It’s honestly a shame that after all these years of building, crypto users still have to deal with stuff like this and this user is literally one of the smartest people in the industry.



0g labs raised $357m $250m of that is labeled as “token commitments” (whatever that even means) literally for nothing apparently the $75m from pre-seed and seed wasn’t enough, so they also did a $30m node sale node sale… basically just a fancy way of saying token sale last time I saw the founder, he was bribing kols to get to the top of the kaito leaderboard they’ve burned millions on this nonsense. not surprising when you have too much money and nothing to actually build it has basically zero activity; they just mint worthless nfts from time to time to pretend something’s happening it’s still sitting at a $1.2b fdv what the fuck does “ai l1” even mean anyway? zero


this is so f*cking scary - a txn made 9 months ago to transfer just $5 ended up causing a $30K loss. TLDR: → a txn was approved 9 months ago → to interact with the ThirdWeb Universal Bridge → Infinite approval was given (just for a $5 transfer) → a vulnerability in the contract was discovered in April → but the contract remained active onchain, including the blog referencing the affected contract address → vulnerability allowed anyone to drain funds from users with infinite approval → the hacker waited 9 months for the user to deposit a substantial amount → And boom - $30K gone in a single txn → funds were sent to Railgun, so can’t be traced → thirdWeb permanently disabled the legacy affected contract after the hack was disclosed → the blog referencing the affected (now-disabled) contract address is still live I don’t even know whom to blame here. It’s honestly a shame that after all these years of building, crypto users still have to deal with stuff like this and this user is literally one of the smartest people in the industry.



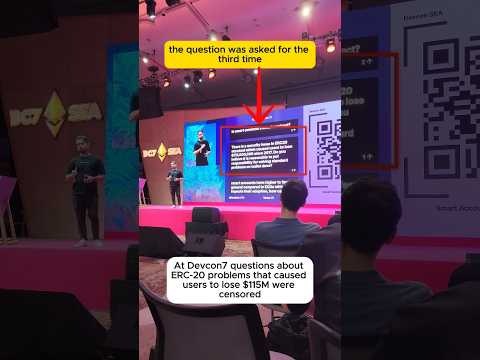
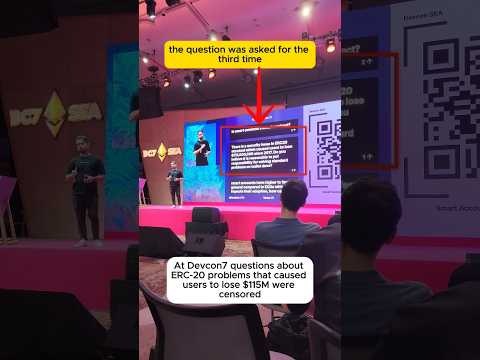
ERC-20 is insecure by design. It violates two of the most basic security principles: - Error handling is a must (there is no transaction handling which makes error handling impossible) - Secure defaults > In ERC-20 the `transfer(..)` function is unhandleable >> devs need a way to deposit tokens to contracts >>> they implement another `approve(..) + transferFrom(..)` pattern to do so >>>>t hey leave `transfer(..)` unhandleable which makes the defaults of ERC-20 unsafe >>>>> approve + transferFrom incentivizes DAPP devs to ask for an unlimited approval since it makes UX and gas fees for their users better >>>>>> users lose money but everyone blames them for making mistakes.... completely ignoring the fact that the root of the problem is the design of the standard and there are dozens of security researchers who are supposed to be competent enough to identify this Whom to blame? - Every security researcher/auditor who didn't write that ERC-20 is an insecure standard. What are they even doing if they don't expose violations of the most basic security principles while pretending to be security experts? Hey @SEAL_911 how many articles have you written about the fact that ERC-20 violates well-known software security principles? What have you done in 8 years to PREVENT it? If you design a piece of software and it violates 2 out of 8 most basic security principles guess what? - People lose money. I've outlined it many times and even designed an alternative ERC-223 standard in 2017 to solve these problems and eliminate the need for approvals completely: medium.com/dex223/erc-20-… dexaran820.medium.com/security-probl… I've highlighted that ERC-20 design will inevitebly result in a loss of funds back during its finalization process #issuecomment-296711733" target="_blank" rel="nofollow noopener">github.com/ethereum/EIPs/…
There were less than $20K at that momen. This problem report was ignored for 8 years and now there are more than $100,000,000 lost because of the lack of error handling and billions lost because of approval-related problems: dexaran.github.io/erc20-losses Regarding approvals in ERC-20 standard (explanation: #issuecomment-1679275590" target="_blank" rel="nofollow noopener">github.com/ethereum/ether…): - The standard was proposed in 2015, there was 1024-call-stack-depth bug in EVM. - Approve & transferFrom pattern was introduced to make tokens unaffected by this bug. It was not a smart design, it was a weird quirk to bypass bugs of EVM. - 1024-call-stack depth bug was fixed in 2016 and rendered approvals unnecessary. - In 2017 I proposed ERC-223 token standard which eliminates approvals completely.

The deep irony that as I sat here writing a defense of privacy in crypto to present in DC next week... my wallet was getting drained and the funds are getting deposited into Railgun.