Jon G
7K posts


Jon G
@GainSec
Hacker by night. 50 CVEs. Husband. Father. Skateboarder. Posts are my own.

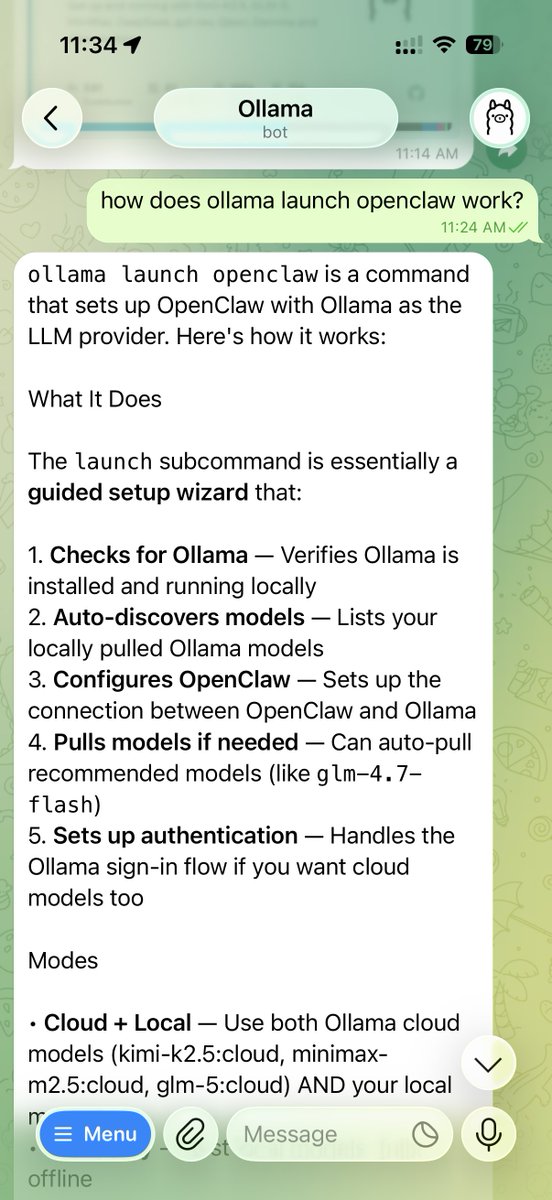
NVIDIA just built a security layer that works with OpenClaw, NemoClaw, and other agents. Not just one... all of them. OpenShell wraps the entire agent stack from the outside... deny-by-default, added security. The point is it isn't an OpenClaw fix, it works with any agent. I have a feeling there'll be more approaches like OpenShell which doesn't compete with OpenClaw but augments with it. Agentic AI still has many factions (Claude Code vs OpenClaw vs whatever Claw fork out there) so providing integration layers for security (and possibly others) is the only way to capitalize... Again, Apple benefited by selling picks and shovels instead of rushing into competition... didn't compete, just provided another layer (local access). NVIDIA is running the same play... OpenShell becomes the security layer for the entire stack.

Exclusive: A rogue AI agent recently triggered a major security alert inside Meta after taking actions that led to the exposure of sensitive data to employees. Read more from @Jjyoti_mann1 👇 thein.fo/4tdRPRV


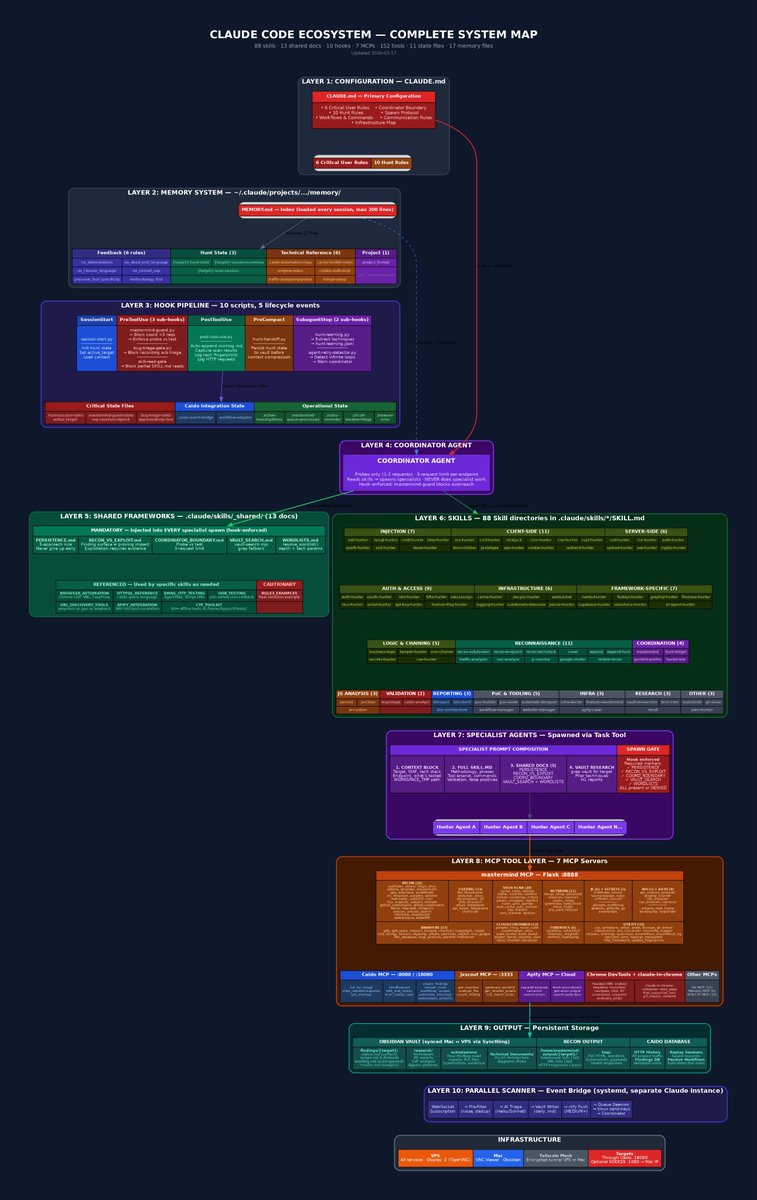



I'm vibe coding an agentic OSINT/SIGINT app over the weekend. I call it Infinite Monitor 🌐 Each widget is its own isolated app with its own instance of claude code.





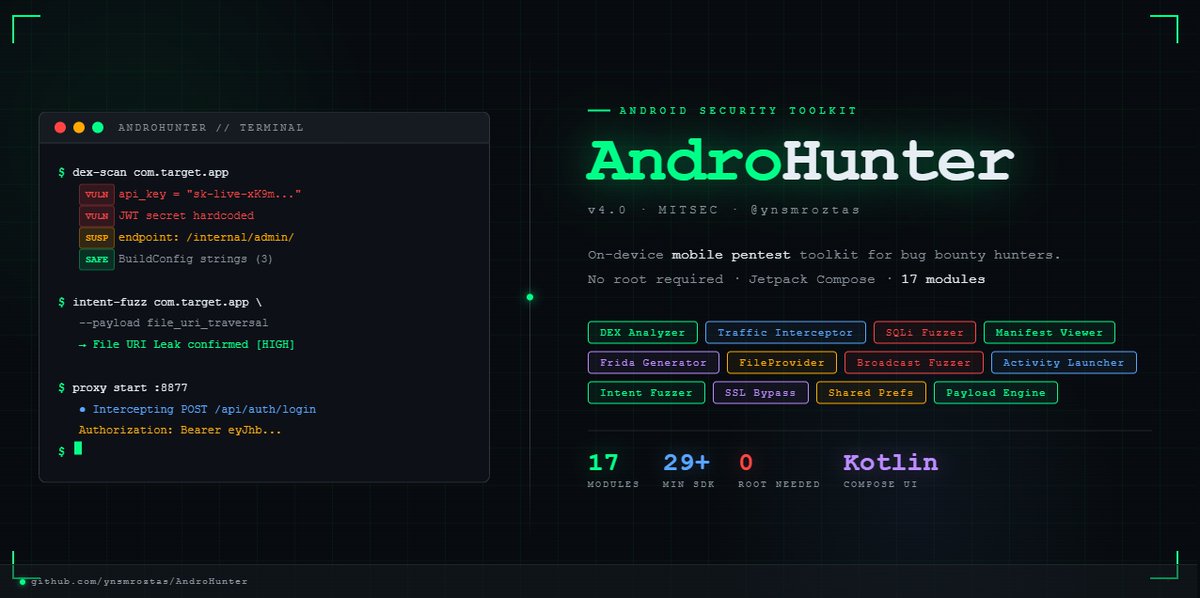
Did you know you can perform SQL injection tests on mobile applications using Ghauri or SQLmap? 🥳🥳🥰🥰 I managed to test potentially critical endpoints by combining both applications. This way, you won't have to connect to the Android application via proxy or deal with SSL Pinning issues; you can directly subject the application to SQL injection tests. I'll be sharing a great article and my tools about this soon, so stay tuned! 🌹🥳🥳 #bugbountytip #bugbountytips #infosec #recon #Android