Guillaume Caillé รีทวีตแล้ว
Guillaume Caillé
156 posts


Guillaume Caillé
@OffenseTeacher
Senior Director - Penetration Testing
เข้าร่วม Temmuz 2012
272 กำลังติดตาม276 ผู้ติดตาม

Another great post by my now ex-colleague (💔) on using some concepts from Ekko to build a more resilient sleep masking technique that masquerades as a legitimate DLL while sleeping. Worth a read!
OldBoy21 ❄️@vincenzosantuc1
In-memory sleeping technique using threads created in suspended state and timers that work with the ResumeThread function in order to adapt SWAPPALA to the Reflective DLL context oldboy21.github.io/posts/2024/06/… #sleeping #memory #c #swappala #hiding #maldev #obfuscation
English

@ShitSecure Haha, sorry😇. Now you have time to do a more interesting one!
English

@OffenseTeacher Well. This was an idea for my next blog post 😅👍
English

Just published my methodology for finding good DLL side-loading candidates while avoiding using DllMain for injection to bypass Loader Lock limitations.
If you have been struggling with this, I hope this saves you time in the future.
okiok.com/achieving-dll-…
English

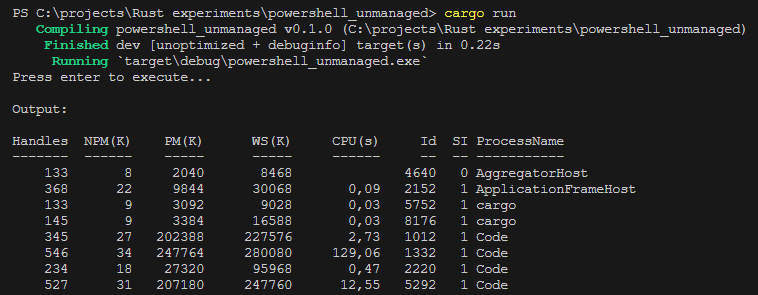
This was a lot more messy than I would've thought it to be, but an interesting project nonetheless: I got PowerShell execution via custom runspaces to work in Rust with the awesome ClrOxide library by @_yamakadi!
Contributed the code as an example here: github.com/yamakadi/clrox…
English

@barberousse_bin @NorthSec_io Sounds interesting! :) will be there
English
Guillaume Caillé รีทวีตแล้ว

How's your M365 password spraying game in 2024 ?
On my side, it's harder than ever.
For instance, after 6 rounds each 6 hours apart, starting to lock out accounts more and more each round, to the point where impact is noticeable.
Rounds performed using the great #TeamFiltration
English

@Tr0llyTr0llFace @wartranslated Wow that made me laugh :p. Thank you.
English

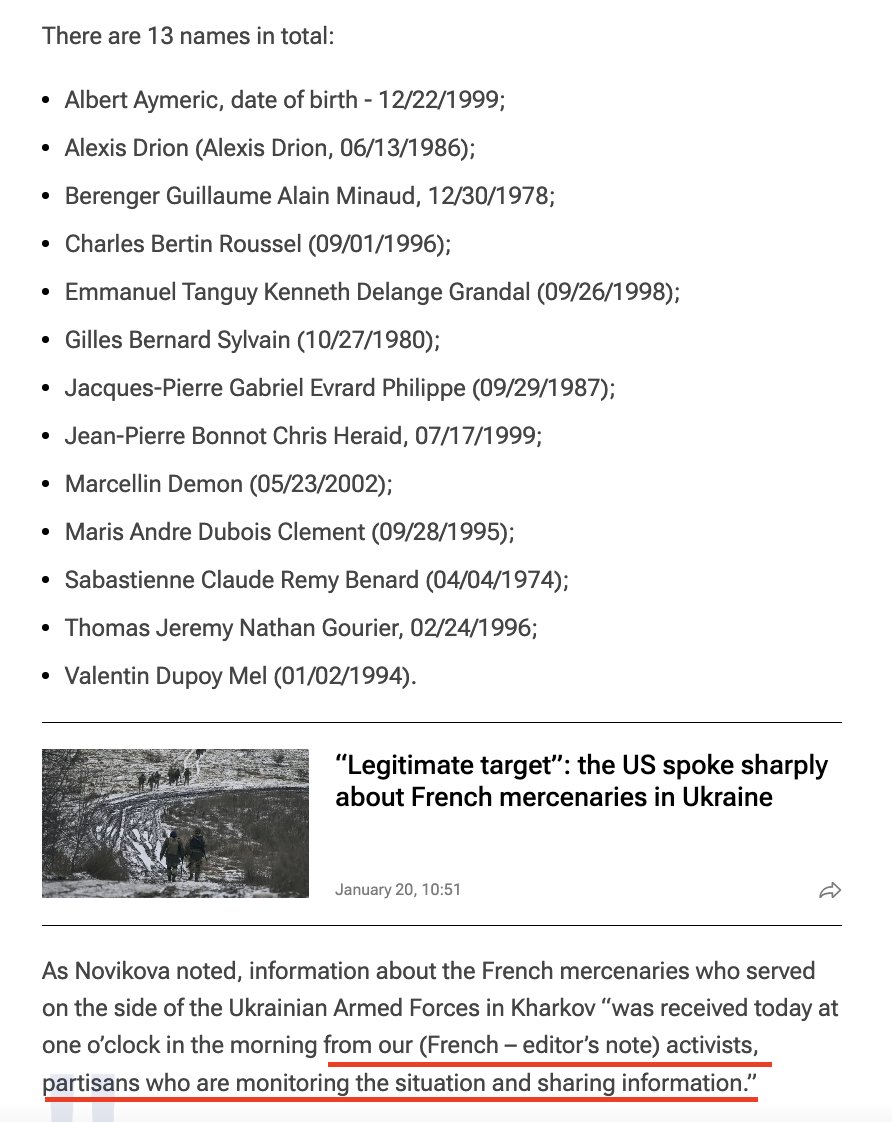
@wartranslated RIP Emmanuel Tanguy Kenneth Delange Grandal, grand master of omelette du fromage, slayer of salade russe, cuisse de grenouille whisperer.
English

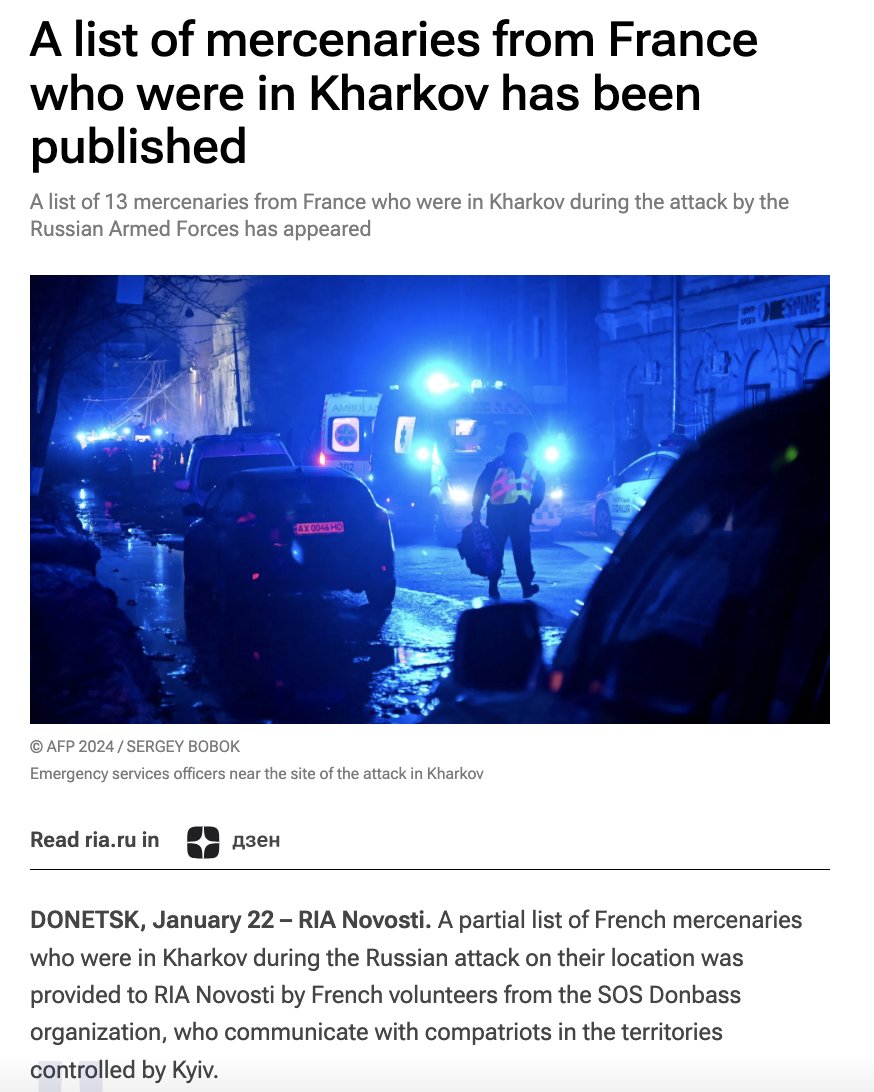
russian news outlet RIA continues pursuing the line about the "French mercenaries" allegedly killed during a missile strike against Kharkiv and even provides a list of names. This information was allegedly "received today at one o’clock in the morning from our French activists, partisans who are monitoring the situation and sharing information".
So the best thing russia could come up with to respond to increased military supply by France, including 40+ SCALP missiles, was striking a civilian building and claiming they killed some "mercenaries".
ria.ru/20240122/naemn…
English

@embee_research I really appreciate your posts on Ghidra. Thanks for publishing these!
English

👽Identifying and Fixing Encrypted Strings in Ghidra 👽
embee-research.ghost.io/ghidra-basics-…
English

Today I wrote a small code using Nim to emulate DLL Unlinking, one of the very old techniques. Not a fancy or new code, but if someone needs such thing, here it is:
#infosec
github.com/frkngksl/Unlin…
English
Guillaume Caillé รีทวีตแล้ว

With initial access to a M365 account, Red Teamers can potentially find a treasure trove of sensitive information. @Flangvik goes over three tools (and one script) that he believes to be the modern-day Triforce for initial access. Read it now on our blog! hubs.la/Q0281CvN0
English

@byt3bl33d3r @HackingLZ @GuhnooPlusLinux @MJHallenbeck We will definitely be paying for it as we have been
English

@HackingLZ @GuhnooPlusLinux @MJHallenbeck We were planning on continuing developing CME before they decided to fork it. After the exchange with the people who created the hostile fork I’ve honestly lost all desire for open source. CME will return as a fully commercial product as that’s somehow more acceptable
English

If people don't know, we've forked CrackMapExec to a community fork and renamed (per request). v1.0.0 coming soon: github.com/Pennyw0rth/Net…
English

@AnubisOnSec @M_haggis @tastypepperoni I thought backstab's driver could not get installed anymore after the last driver blacklist update. I am wrong?
English

@M_haggis @tastypepperoni This tool is listed in the LOLDriver, but that's why all these EDR killers and PPL methods that use BYOVD will always be inferior to using procexp.sys, this driver has been goated for a while:
github.com/Yaxser/Backstab
English

Just dove into this blog about bypassing Protected Process Light (PPL) on Windows using PPLBlade by @tastypepperoni ! 🤯 Written entirely in Go, this tool exposes methods to sidestep Defender's signature-based detections.
🛡️Defenders, understanding this is crucial! 🛡️
PPLBlade leverages this #LOLDrivers - PROCEXP152.sys - to open a handle to a running process, thereby allowing it to access processes that are under PPL protection.
Must-read: tastypepperoni.medium.com/bypassing-defe….
Check out the driver: loldrivers.io/drivers/0567c6…
Abhijith B R@abhijithbr
Did some experiments on bypassing PPL Protection and Windows Defender, to dump LSASS. No detections so far! @tastypepperoni's PPLBlade repo: github.com/tastypepperoni… My short write-up: tacticaladversary.io/adversary-tact… #adversarytactics #redteam #tacticaladversary #PPLBlade
English

@R0h1rr1m @JulioUrena So nice!
Will definitely be using it :)
English
Guillaume Caillé รีทวีตแล้ว

I developed a Fileless Lateral Movement tool called NimExec. It changes service configuration to execute the payload via manually crafted RPC packets. It's the improved version of @JulioUrena 's SharpNoPSExec with Pass the Hash support. Enjoy!
#infosec
github.com/frkngksl/NimEx…
English

Almost done with RTO course and I learned a lot, it is very complete and up-to-date.
However, one *key* material is not covered... Which MX switches is @_RastaMouse using ! We hear them in the background during the demo videos, I'm loving the sound.
English

Here is a small POC for doing steganography with Nim-Lang. Useful for reducing payload entropy on disk or giving you a remote Killswitch.
github.com/OffenseTeacher…
English

After various requests and DMs, I've decided to write a detailed blog on Detection Engineering and Evasion. This will explain in detail how modern EDRs such as Elastic, CS, ATP or S1 build detections, how to test/write your payloads against them, this will include everything from yara rules to kernel callbacks... Watch out this space for more information! #darkvortex
English

Last week I ported TinyNuke HVNC to a Cobalt Strike BOF: github.com/WKL-Sec/Hidden…
English