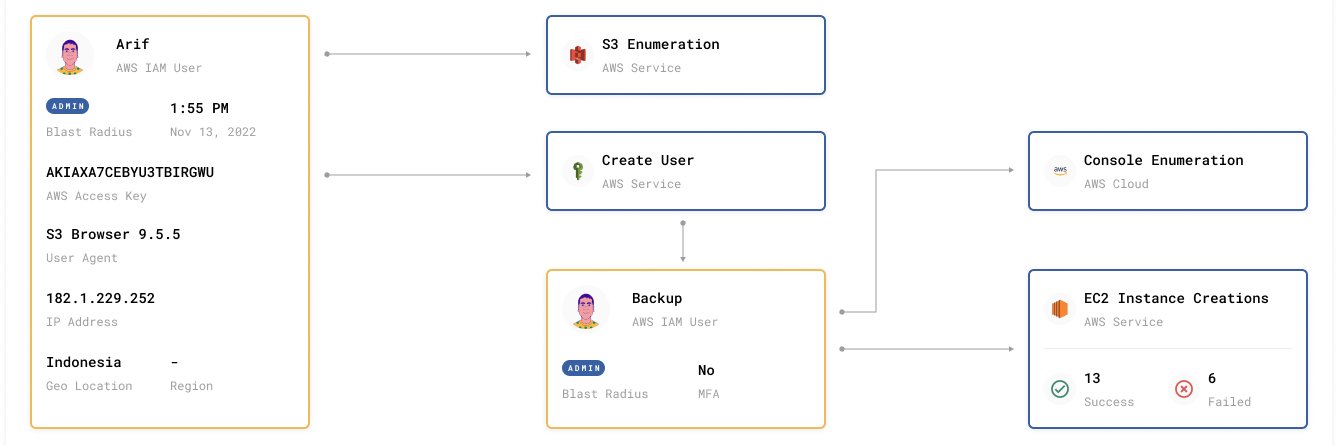
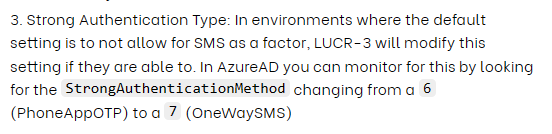
Beware of LUCR-3! 🚨 Threat actor that overlaps with Scattered Spider, Oktapus, UNC3944, & STORM-0875, they exploit IDPs for initial access & aim to steal IP for extortion. They use victims' tools and evade detection with expertise. @permisosecurity permiso.io/blog/lucr-3-sc…