Oceanwho
129 posts



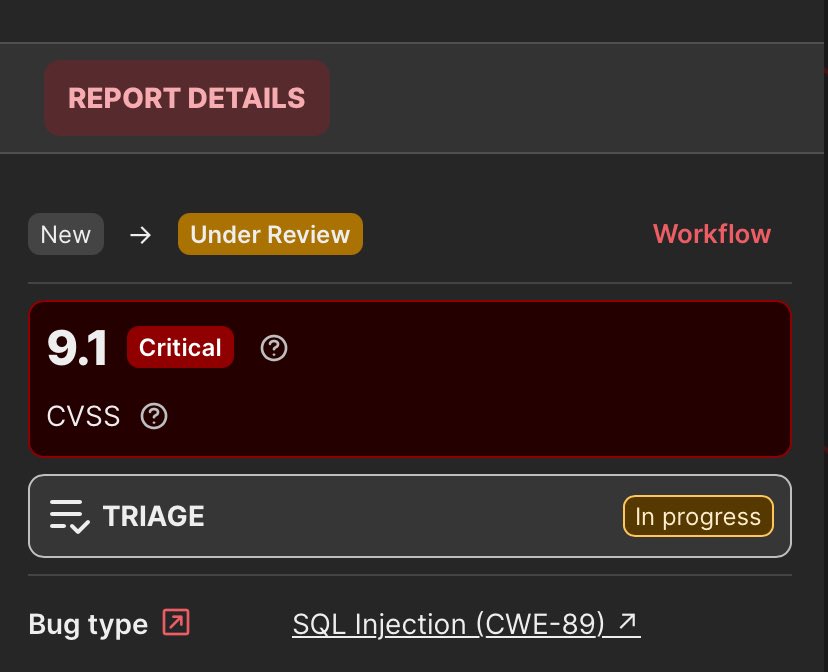
Just Found & reported 2 SQL Injections:
#BugBounty #BugBountyLife #EthicalHacking #CyberSecurity #InfoSec #SQLi #WebSecurity #KeepHacking @intigriti

English

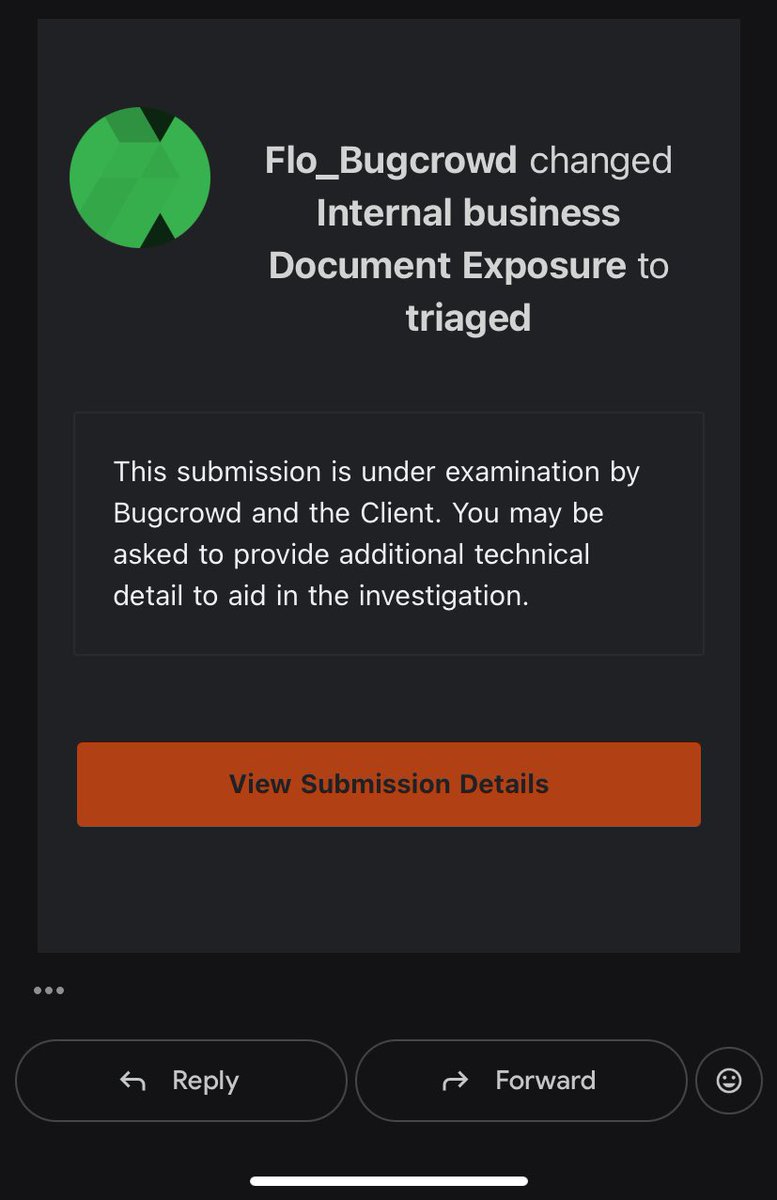
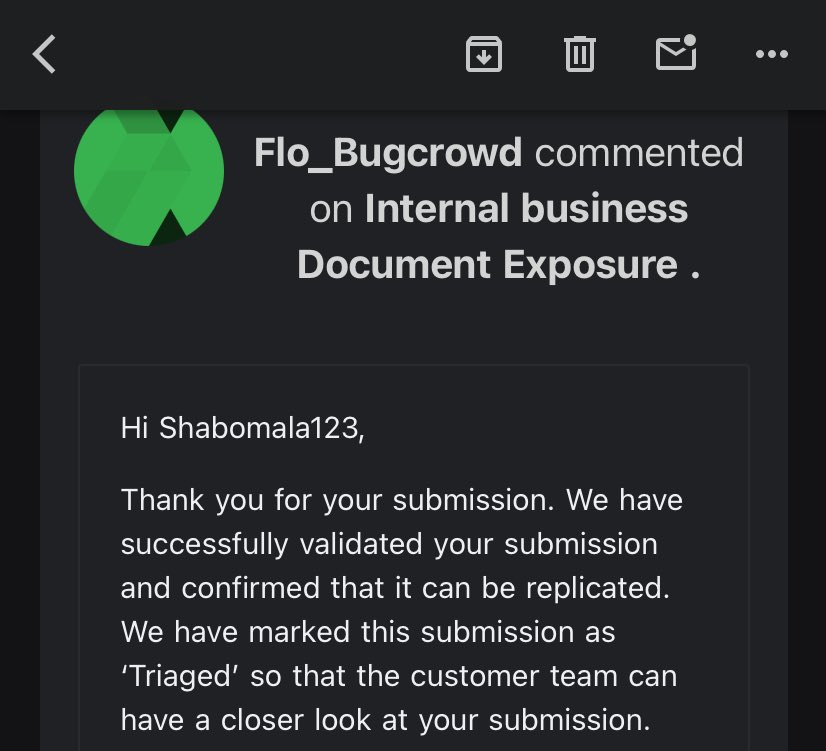
Just got my first paid bug on @Bugcrowd
Privilege escalation via mass assignment.
Tip: Always pay attention to the various ways the same action can be performed.
#bugbounty

English

Y-Dork 🚀🚀🚀🚀
Tip: Wildcard scope work well with Y-Dork via your Sock5
Big up @Olamdeen @4osp3l @GodfatherOrwa
English

XSS ➝ Privilege Escalation ➝ Full Tenant Takeover 🚨
#XSS #CrossSiteScripting #WebSecurity #AppSec #ApplicationSecurity #OWASP #BugBounty #EthicalHacking #InfoSec #PenTesting #RedTeam #BlueTeam #SecureCoding #BugBounty

English
Oceanwho รีทวีตแล้ว

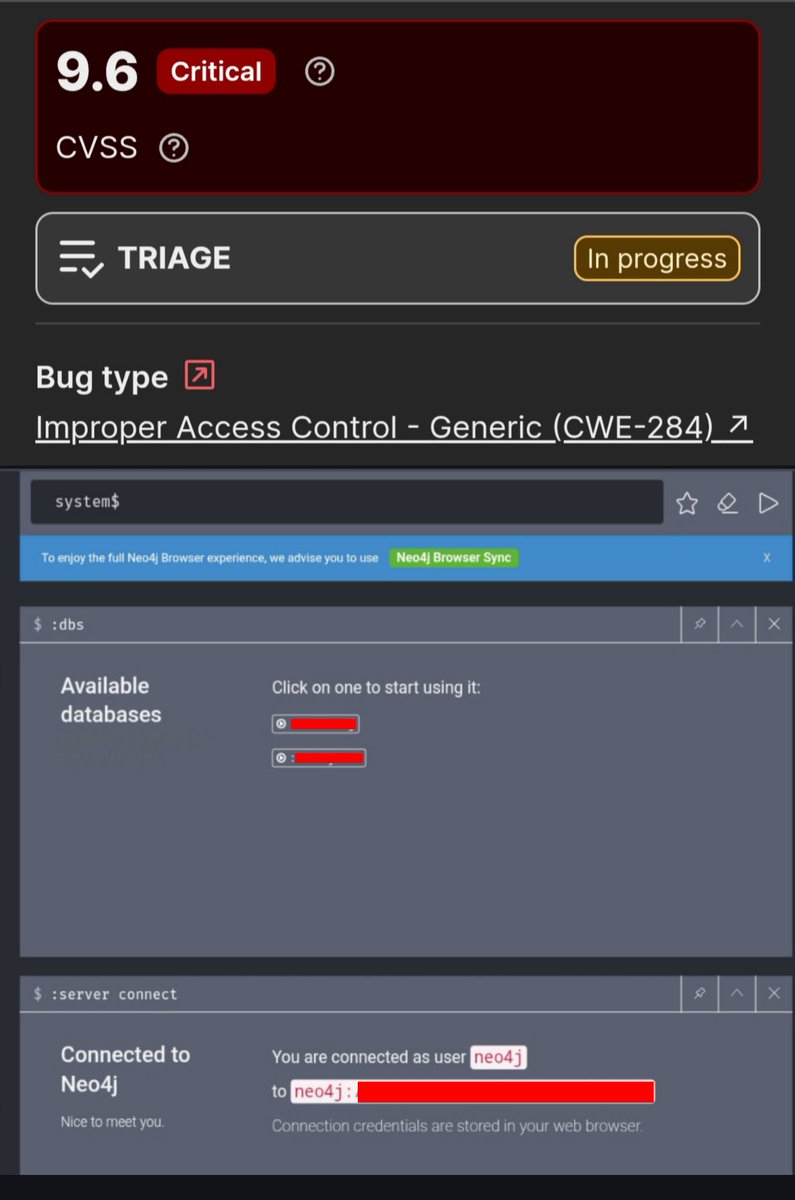
🚨 Neo4j Recon Tip: It’s worse than you think! 🚨
Finding default creds (neo4j:neo4j) isn't just a simple info leak.
Typically, public accounts should be restricted to READ-ONLY. But during recon, I discovered that these accounts often hold full ADMINISTRATIVE & WRITE privileges. 🔥
An anonymous visitor can view data, but also modify, completely destroy the DB, or create persistent backdoors.
Here is the Cypher payload to drop a new admin user:
👇
CALL dbms.security.createUser('ynsmroztas_test', 'P@ssw0rd123!', false)
Game over. 💀🏴☠️
#bugbountytip #bugbountytips #InfoSec #recon
@yeswehack
English

Just got a reward for a vulnerability submitted on @yeswehack -- Server-Side Request Forgery (SSRF) (CWE-918). yeswehack.com/hunters/icare #YesWeRHackers
English
Oceanwho รีทวีตแล้ว

Alhamdulillah, I was able to find a bug that allowed me to register as an admin on any customer panel of the company. I might write a full write-up later 🫶
#BugBounty
English

1. Go to thexssrat.com
2. Pick a COURSE (not bundle)
3. Comment here
4. Share
5. Like
At 200 likes, i will take the 3 most popular courses and give away 1000 seats each :-)
English