Keith Smiley
25.6K posts


Keith Smiley
@SmileyKeith
devx @Modular, maintainer of @bazelbuild's iOS support, creator of @MobileNativeFdn. LLVM & Swift contributor. Previously Principal Engineer @Lyft
@[email protected] เข้าร่วม Nisan 2008
749 กำลังติดตาม8K ผู้ติดตาม

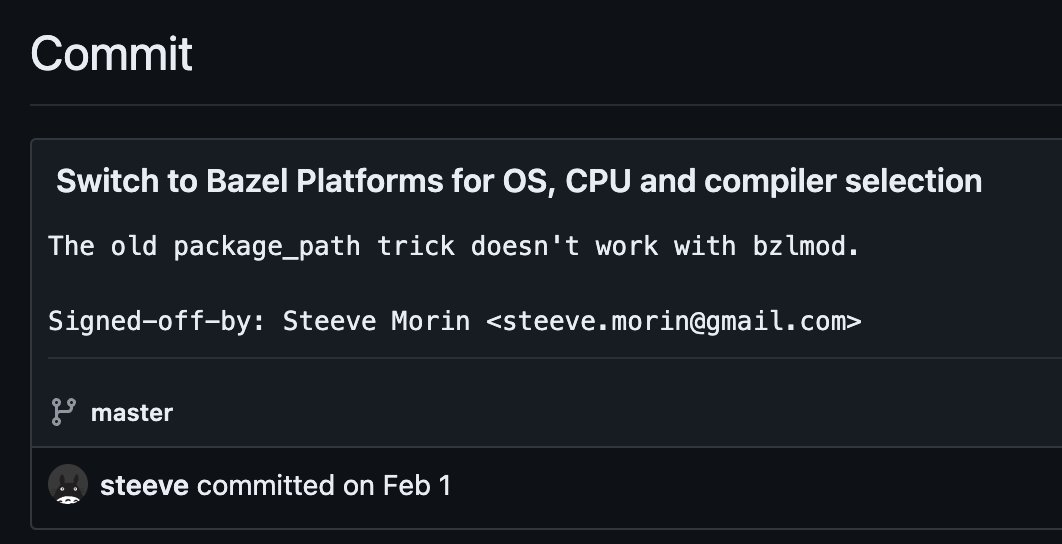
@steeve Yea you should upstream that. Stuff seems pretty dated
English

@SmileyKeith Well well well, we meet again.
My gift to you my man: github.com/zml/nsync/comm…
English
Keith Smiley รีทวีตแล้ว

Wow, @llvmorg just passed half a million commits to the monorepo! Congratulations to all of the 3811 contributors so far!
If you love LLVM, consider star'ing the repo: github.com/llvm/llvm-proj…

English
Keith Smiley รีทวีตแล้ว

Wow that's right. This was a big day and Swift has come a long way in the intervening decade: Congrats to everyone who has driven it forward to support such an amazing tech platform! 🍎🐣
Basic Apple Guy@BasicAppleGuy
10 Years Ago: Apple Announced Swift
English

Excited to announce I'll be demoing my desk companion project at @OpenSauceLive in June!
It's a little device with an e-ink screen, air quality sensors (temp, co2) + wifi+bluetooth.
Designed to be hackable so you can write your own apps for it, and the enclosure is 3D printed.

English

@krzyzanowskim Yea that's what I did everywhere too ¯\_(ツ)_/¯
English

@SmileyKeith and here we are 5 years later. I just got a PR to remove space for compatibility
English

Bazel build system can’t handle filename with a space 🙃 Everything is hard in 2024.
github.com/bazelbuild/baz…
English
Keith Smiley รีทวีตแล้ว

The wait for macOS 14.4/iOS 17.4 sauce is OVER! 🍝🥫
XNU
github.com/apple-oss-dist…
Security
github.com/apple-oss-dist…
OBJC
github.com/apple-oss-dist…
ld64
github.com/apple-oss-dist…
dyld
github.com/apple-oss-dist…
English
Keith Smiley รีทวีตแล้ว

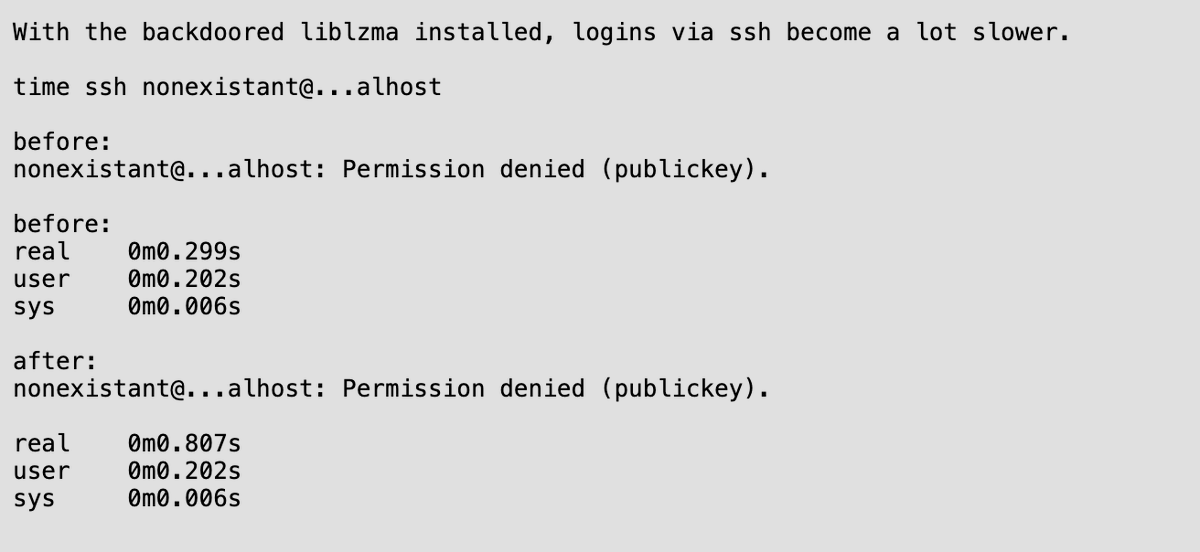
The linker is in a better position to inject malicious code into your system than xz/liblzma if compromised because it can do whatever it wants with the programs being linked. For example, replacing a specific function during linking openssh would be a pretty easy hack.
Therefore, it is important to use a trustworthy linker binary to build your program. But how do you build a trustworthy linker? If you use a malicious linker to link another linker, it can inject code into the new linker which in turn could do something malicious to other programs. This is the well-known chain of trust problem.
This is a real issue for us because we distribute mold binary packages on our GitHub release pages. Fortunately, we recently implemented a change in the script to create the binary packages so that the script is reproducible -- meaning that regardless of the environment it's run in, the script always creates bit-for-bit identical output for the same git commit.
With the reproducible build, you can independently verify that our binary distributions are actually built from the corresponding release of source files. You can also ensure that no third-party binaries are involved during the build.
Thanks to Docker and QEMU, it is pretty easy to write a reproducible build script these days. I'd strongly recommend doing the same if you are distributing binary tarballs. The script for the mold linker is available here: github.com/rui314/mold/bl…
English
Keith Smiley รีทวีตแล้ว

Mojo hit an important milestone today by open sourcing the stdlib, excited to see where it goes from here! 🔥
Modular@Modular
👩💻 We're excited to announce that we've open sourced the Mojo 🔥standard library! 📚 Building Mojo🔥 in the open will lead to a better result and open sourcing the standard library is our next step in the journey. 🚀 We're also dropping MAX 24.2 today! modular.com/blog/the-next-…
English
Keith Smiley รีทวีตแล้ว

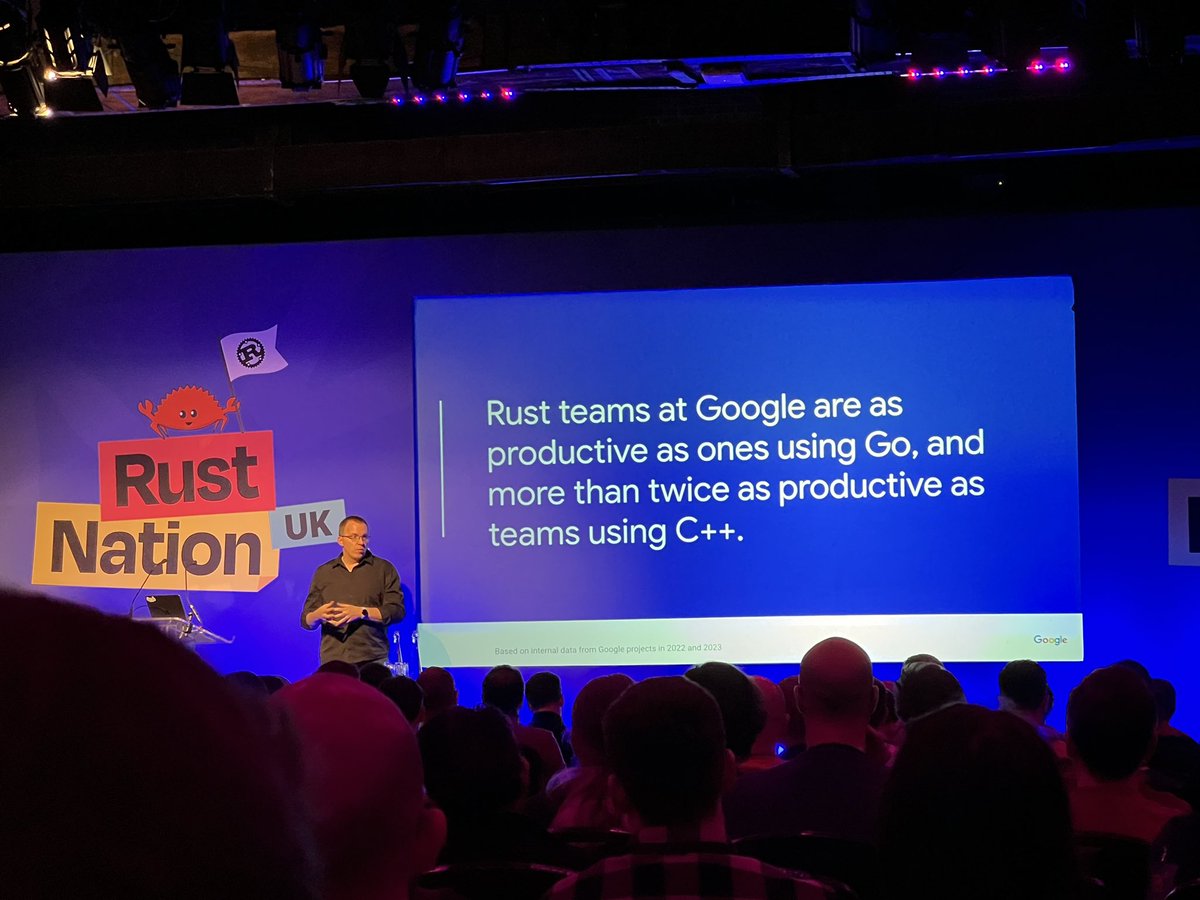
“Rust teams at Google are as productive as ones using Go, and more than twice as productive as teams using C++.” @larsberg_ #RustNationUK
English
Keith Smiley รีทวีตแล้ว

Making a Macintosh Studio youtu.be/BuEziDm9gQw?si…
(This person's videos are generally awesome if you like this one)

YouTube
English
Keith Smiley รีทวีตแล้ว

@SmileyKeith fwiw so far we think that they are considerably slower even w/o the overhead of SwiftSyntax -- forums.swift.org/t/swift-macros…
English