Alex. Turing
286 posts
Alex. Turing
@TuringAlex
Kernel Developer | Security REsearcher | Basketball Fan {Botconf | VirusBulletin | Kaspersky SAS} Speaker Current: @Xlab_qax EX: @360Netlab @Kaspersky AKA 渣兔






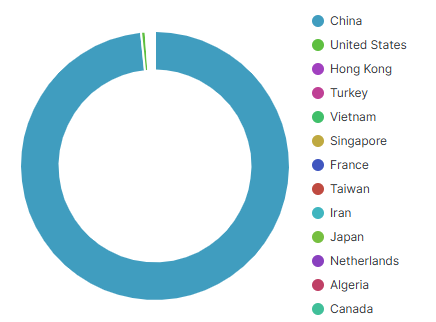
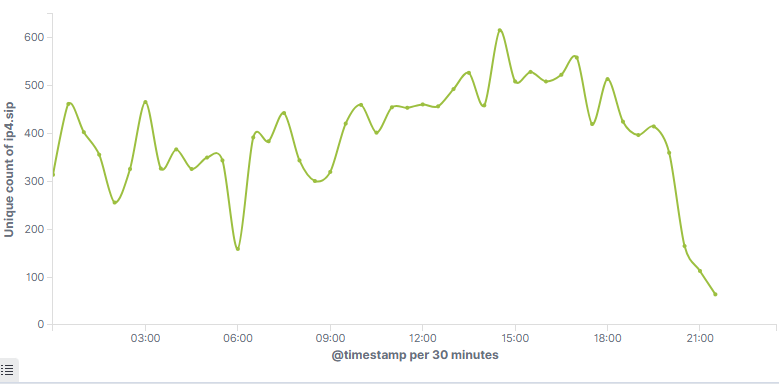
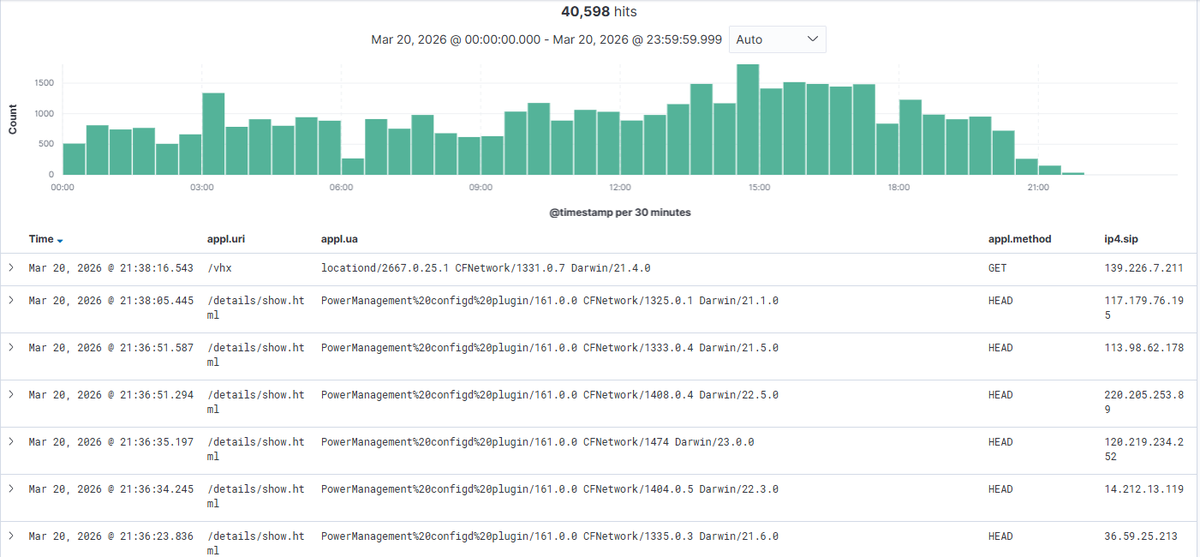
Our new blog. Exposing the Funnull RingH23 Arsenal and MacCMS Supply Chain Attacks blog.xlab.qianxin.com/funnull-resurf…
Our new blog. Exposing the Funnull RingH23 Arsenal and MacCMS Supply Chain Attacks blog.xlab.qianxin.com/funnull-resurf…






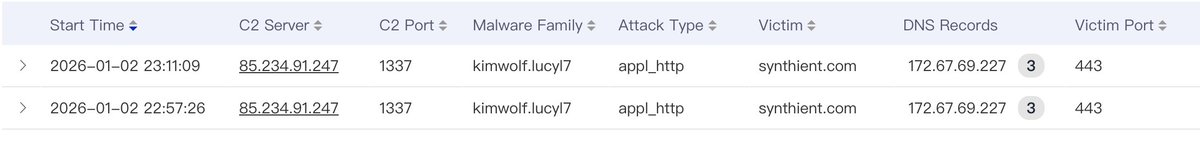
We are actively being DDoS'd given the publication of this research. We apologize if the website is offline.

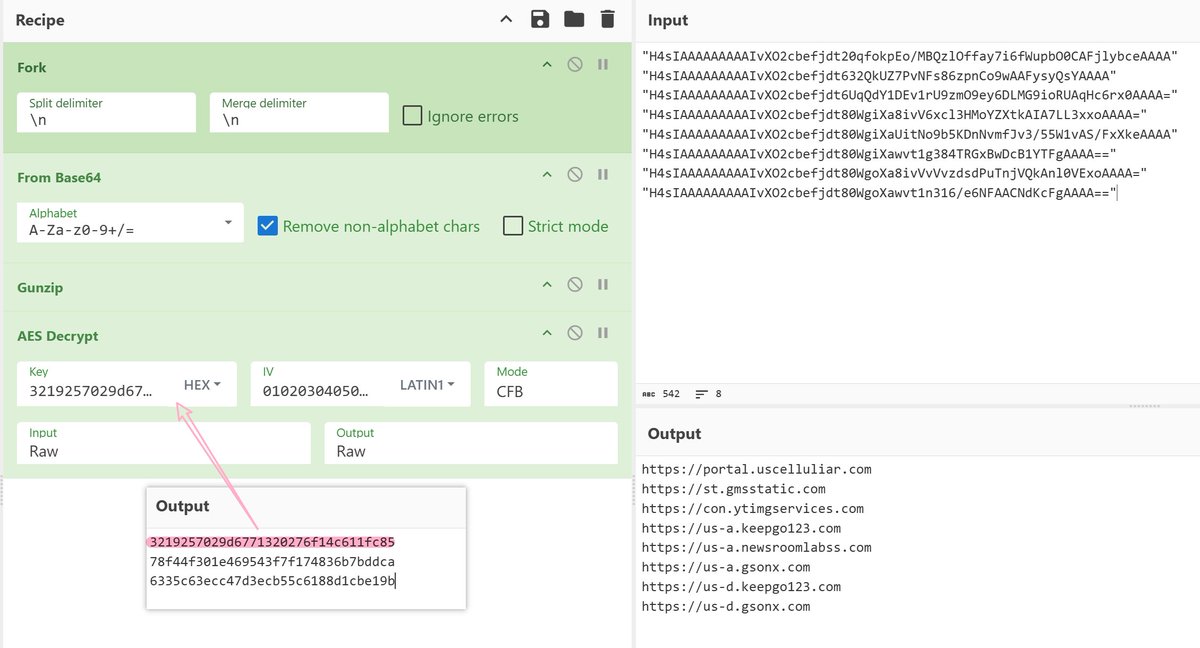
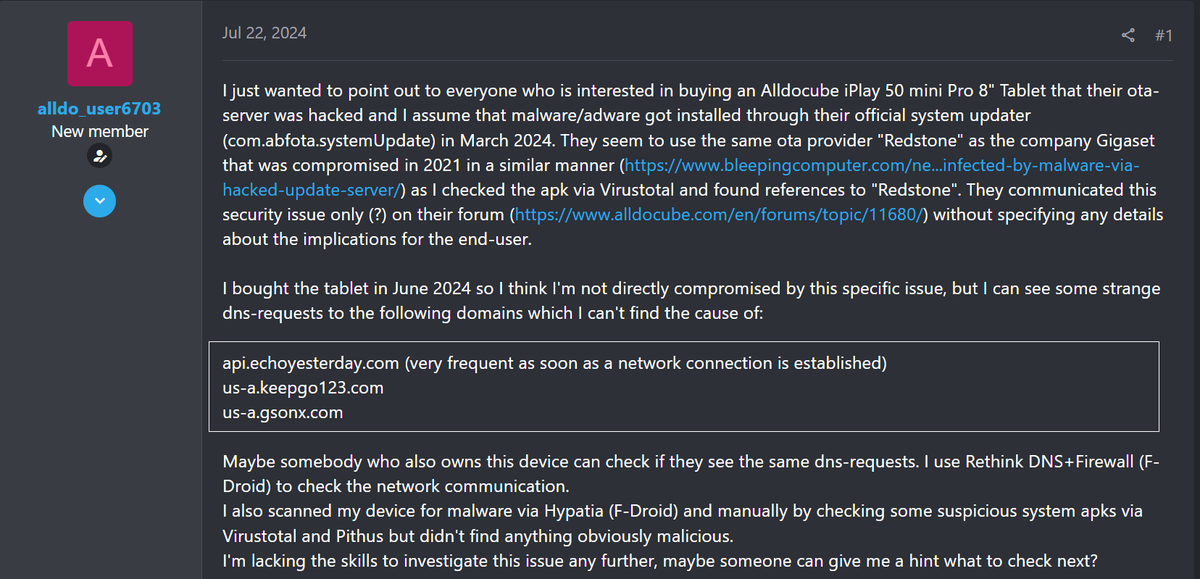

#Kaspersky researchers discovered preinstalled malware on certain models of tablets running Android – we called it Keenadu. It's a backdoor in 𝘭𝘪𝘣𝘢𝘯𝘥𝘳𝘰𝘪𝘥_𝘳𝘶𝘯𝘵𝘪𝘮𝘦.𝘴𝘰. More details are coming soon! #KasperskyGReAT #Research #Cybersecurity