A mysterious hacker group known as #Mr_Rot13, which has operated covertly for six years, is exploiting critical cPanel vulnerabilities to deploy backdoor malware. blog.xlab.qianxin.com/mr_rot13-the-e…
Alex. Turing
299 posts
@TuringAlex
Kernel Developer | Security REsearcher | Basketball Fan {Botconf | VirusBulletin | Kaspersky SAS} Speaker Current: @Xlab_qax EX: @360Netlab @Kaspersky AKA 渣兔
A mysterious hacker group known as #Mr_Rot13, which has operated covertly for six years, is exploiting critical cPanel vulnerabilities to deploy backdoor malware. blog.xlab.qianxin.com/mr_rot13-the-e…


@lorenzofb @juanandres_gs I guess the idea was promoted in this 2014 blogpost "APT research is like paleontology...", that I wrote together with @vkamluk and @ryanaraine - securelist.com/the-art-of-fin… - this came right after Regin, which required some deep cyberpaleontology to figure out

🚨 NEW RESEARCH: xlabs_v1 DDoS-for-Hire IoT Botnet Exposed - One Open Directory. An Entire Operation Revealed. hunt.io/blog/xlabs-v1-… The operator built a full commercial DDoS-for-hire operation. Tiered pricing, 21 flood variants, competitor-killing routines baked in. Then left the whole toolkit on a public server with no login. Hunt.io AttackCapture tool had it indexed before they noticed. Key findings: - Botnet branded xlabs_v1, operator handle Tadashi, targeting game servers and Minecraft hosts - 21 flood variants including RakNet and OpenVPN-shaped UDP to dodge common filters - TCP/5555 observed open on 4M+ hosts in the past 180 days, any running ADB is a potential target - ChaCha20 encryption broken via known-plaintext, full nonce reuse across all 16 calls - C2, staging, distribution, and Monero cryptojacking all inside one bulletproof /24 in the Netherlands 👉 Full IOCs, MITRE mapping, and HuntSQL queries: hunt.io/blog/xlabs-v1-…
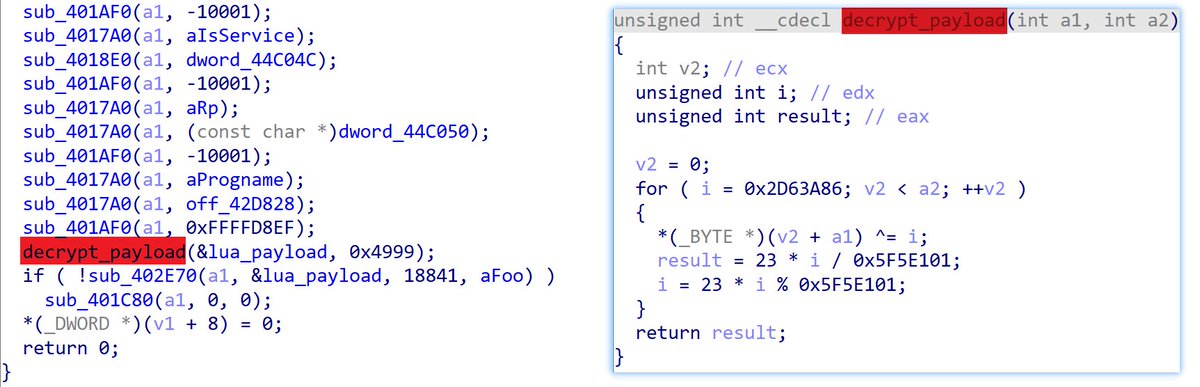
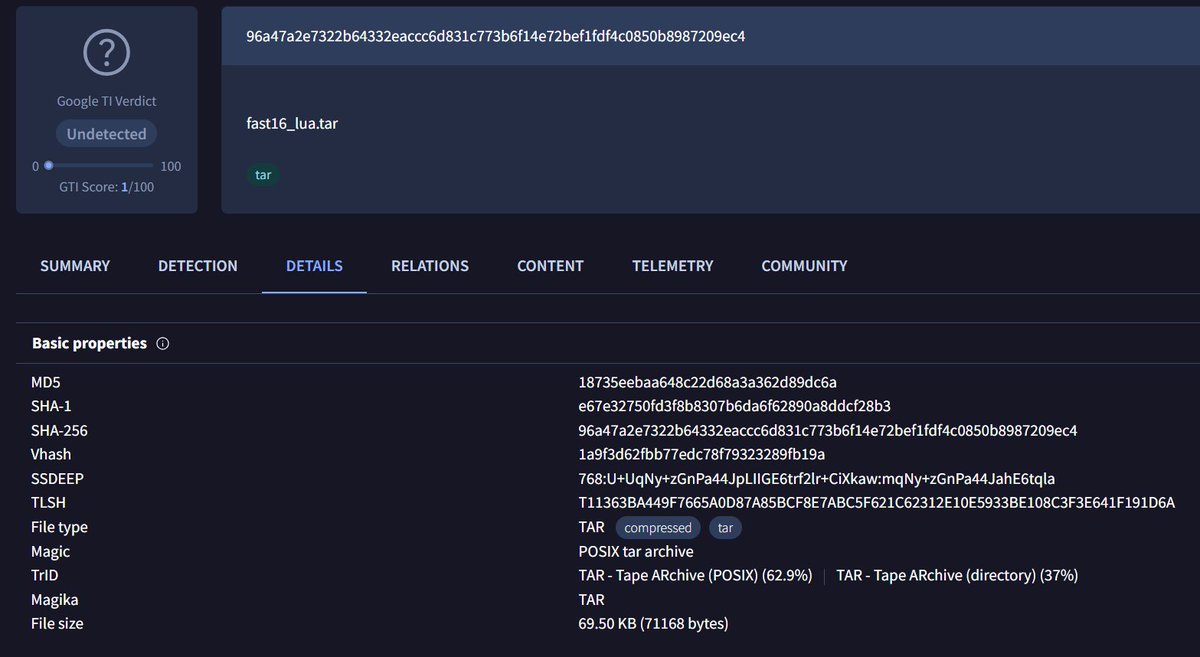
Fresh research from the team (@vkamluk / @juanandres_gs) - this one goes back quite awhile! fast16 | Mystery ShadowBrokers Reference Reveals High-Precision Software Sabotage 5 Years Before Stuxnet sentinelone.com/labs/fast16-my…