Pierre Milioni รีทวีตแล้ว

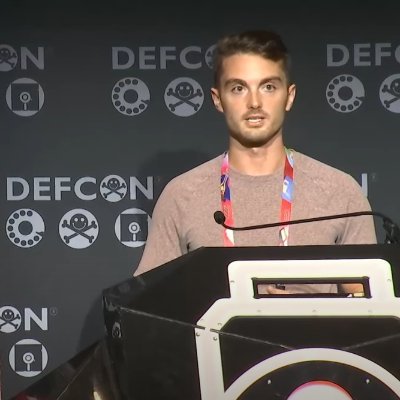
From legacy WEP to WPA3-Enterprise: sharing our recent #WiFi field experiences. 📡
We detail various scenarios to better understand the risks, including WPA3 PEAP relaying & optimized online PSK brute-forcing.
⤵️ synacktiv.com/en/publication…
English