

Cimol
9.6K posts







MPC. FHE. TEEs. All powerful on their own, but none solve the coordination problem. The hard part isn’t just encrypting computation; it’s the orchestration required to make it functional and secure. That’s what Rialo Extended Execution (REX) does. REX is a protocol-level orchestration system for confidential computation that manages the entire lifecycle of a secure request: Program Governance – Programs to be executed are verified and approved for specific execution runs before they ever touch the core. Encrypted Routing – Encrypted inputs are routed cryptographically to a computation core only after the appropriate program logic is loaded. Explicit Consent – Computation is performed only after explicit authorization from both the application and the user, enforced by strict policy. Confidential Compute Core – Secure execution using MPC, FHE, or TEEs, including protected Web2 API calls within an isolated environment. Verifiable Outputs – The system generates and verifies cryptographic attestations that prove a specific computation was correctly executed before routing the result to its destination. REX transforms Rialo into infrastructure for real-world secure computation: Private AI agents that process personal data without seeing it. Sensitive enterprise workflows that maintain competitive secrecy. Authenticated API automation for secure, off-chain interactions. Verifiable off-chain compute with immutable on-chain guarantees. This is native privacy at the protocol layer. Get Real. Get Rialo.


MPC. FHE. TEEs. All powerful on their own, but none solve the coordination problem. The hard part isn’t just encrypting computation; it’s the orchestration required to make it functional and secure. That’s what Rialo Extended Execution (REX) does. REX is a protocol-level orchestration system for confidential computation that manages the entire lifecycle of a secure request: Program Governance – Programs to be executed are verified and approved for specific execution runs before they ever touch the core. Encrypted Routing – Encrypted inputs are routed cryptographically to a computation core only after the appropriate program logic is loaded. Explicit Consent – Computation is performed only after explicit authorization from both the application and the user, enforced by strict policy. Confidential Compute Core – Secure execution using MPC, FHE, or TEEs, including protected Web2 API calls within an isolated environment. Verifiable Outputs – The system generates and verifies cryptographic attestations that prove a specific computation was correctly executed before routing the result to its destination. REX transforms Rialo into infrastructure for real-world secure computation: Private AI agents that process personal data without seeing it. Sensitive enterprise workflows that maintain competitive secrecy. Authenticated API automation for secure, off-chain interactions. Verifiable off-chain compute with immutable on-chain guarantees. This is native privacy at the protocol layer. Get Real. Get Rialo.





this week’s rialo shark tank recap; another edition of the rialo shark tank just concluded it’s basically a space where builders showcase what they’re working on, and the community decides which product stands out the most huge shoutout to everyone who showed up both the builders and the community members who came through as audience this shark tank is quickly becoming one of my favorite events on the rialo server, probably because i see myself becoming a builder too ∑ three projects were presented today: • trigr, • rialestate, and • rialobster ⊂ ⊃⊂ ⊃⊂ ⊃⊂ ⊃ ➝ nftgal presented trigr — a decentralized trading terminal with native automation that lets users execute trades directly on-chain without bots, keepers, or intermediaries, improving reliability and fairness ➝ rita presented rialestate — a platform that allows users to tokenize assets and properties, removing middlemen and land grabbers. it supports usdc, bank transfers, and card payments, and it’s more like a live product ➝ lun presented rialobster, — an agentic infrastructure designed for the rialo blockchain, where autonomous agents handle tasks seamlessly, with no subscriptions required and users able to deploy their own agents ⊂ ⊃⊂ ⊃⊂ ⊃⊂ ⊃ ✓ one thing i noticed across all three projects is their clean ui, something @ericargent31113 also commended i’ll probably start dropping weekly highlights on on the rialo shark tank make sure you’re on the server every thursday by 4:30pm utc so you don’t miss the next one grialo rialones!


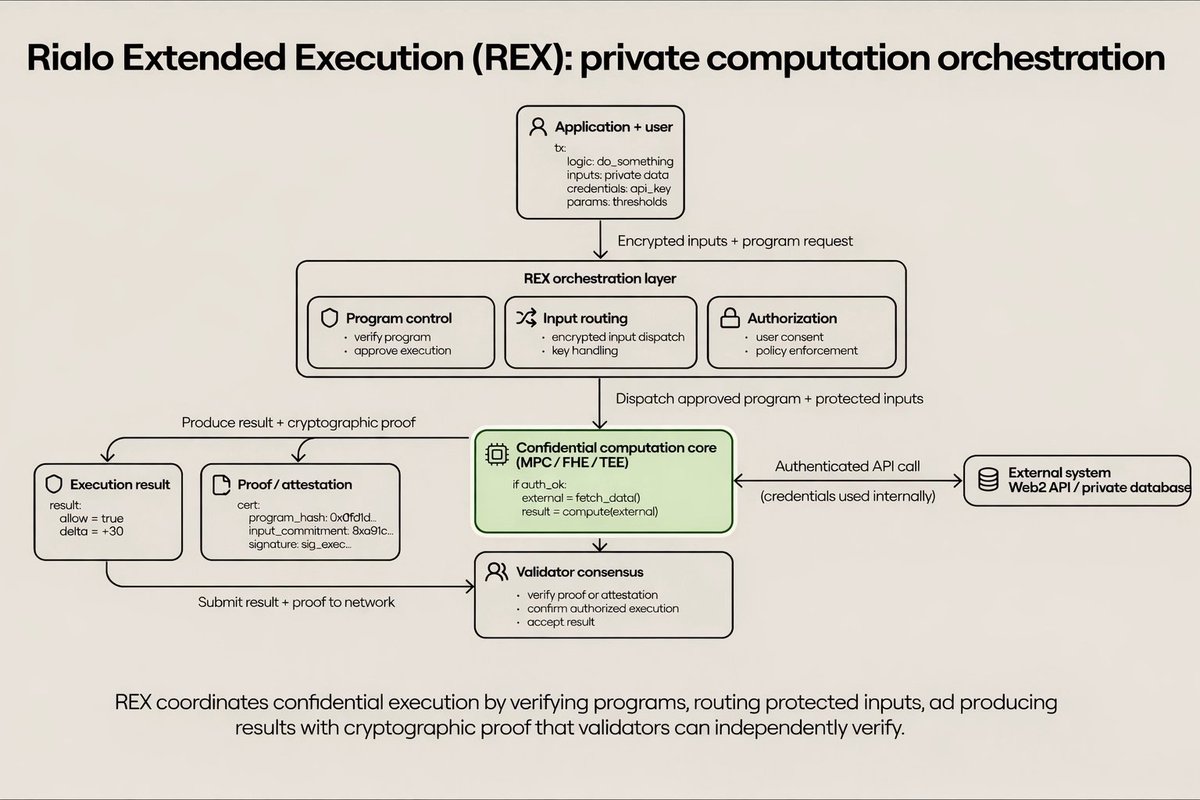
MPC. FHE. TEEs. All powerful on their own, but none solve the coordination problem. The hard part isn’t just encrypting computation; it’s the orchestration required to make it functional and secure. That’s what Rialo Extended Execution (REX) does. REX is a protocol-level orchestration system for confidential computation that manages the entire lifecycle of a secure request: Program Governance – Programs to be executed are verified and approved for specific execution runs before they ever touch the core. Encrypted Routing – Encrypted inputs are routed cryptographically to a computation core only after the appropriate program logic is loaded. Explicit Consent – Computation is performed only after explicit authorization from both the application and the user, enforced by strict policy. Confidential Compute Core – Secure execution using MPC, FHE, or TEEs, including protected Web2 API calls within an isolated environment. Verifiable Outputs – The system generates and verifies cryptographic attestations that prove a specific computation was correctly executed before routing the result to its destination. REX transforms Rialo into infrastructure for real-world secure computation: Private AI agents that process personal data without seeing it. Sensitive enterprise workflows that maintain competitive secrecy. Authenticated API automation for secure, off-chain interactions. Verifiable off-chain compute with immutable on-chain guarantees. This is native privacy at the protocol layer. Get Real. Get Rialo.


"Why didn't you buy Bitcoin in 2010?" Me in 2010:

