drivertom
1.4K posts

drivertom
@drivertomtt
学生/信息安全/CTFer Student/Infosec/CTFer/


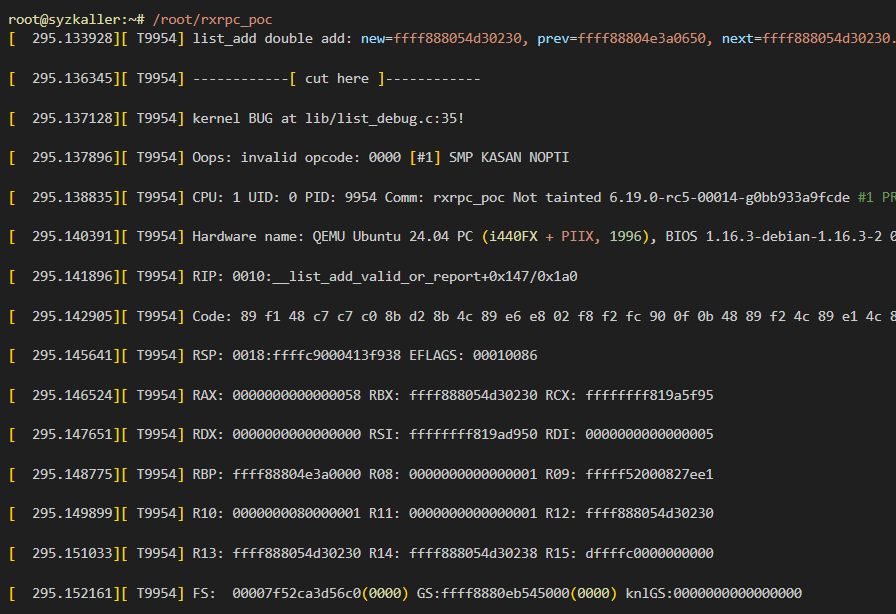
Our AI Agent popped a root shell on Ubuntu 26.04 on the first day it was released :)

Our code auditing agent with “inferior” model discovered 300+ bugs in 3 days under $20k cost. 25 were confirmed exploitable zero-days. We already built 6 browser exploits across 6 different 0-days and 3 Google COS kernel exploits, with 21 more exploitable cases in the pipeline:

WOOT reviews in 2026: treating an obvious hallucination-spam repo as a "publicly available PoC" to question rigor. The "PoC": github.com/Kronk-imp/CVE-… To be fair, not every review comment was wrong. But this was not even the only ridiculous part of the process.

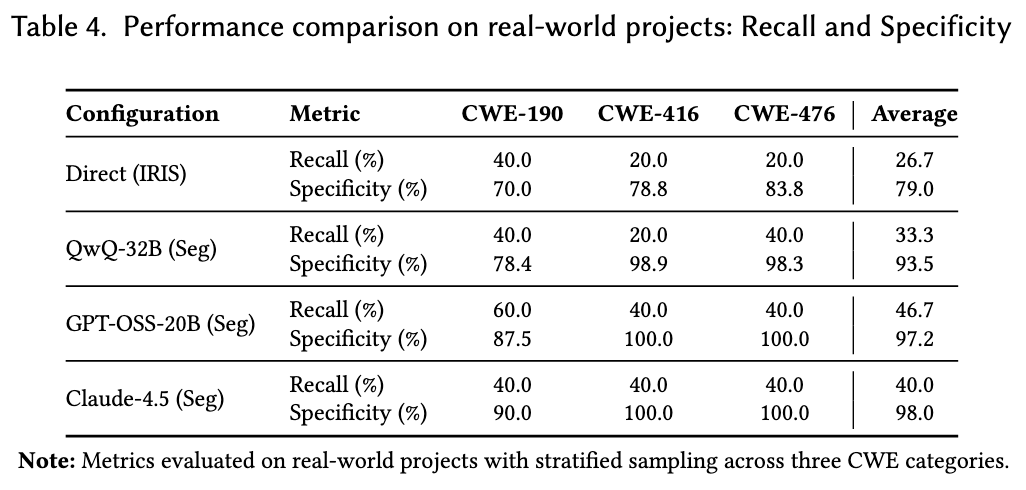
Introducing Claude Code Security, now in limited research preview. It scans codebases for vulnerabilities and suggests targeted software patches for human review, allowing teams to find and fix issues that traditional tools often miss. Learn more: anthropic.com/news/claude-co…


Blog post: On the Coming Industrialisation of Exploit Generation with LLMs sean.heelan.io/2026/01/18/on-… TL;DR: I ran an experiment with GPT-5.2 and Opus 4.5 based agents to generate exploits for a zeroday QuickJS bug. They're pretty good at it. Code: github.com/SeanHeelan/ana…

hotcrp arb file read exploit: ① Register a submission ② Upload any file, view it ③ Add `?docid=2` (change 2 to any number, it's a sequence number start from 2) And you will be able to read *every* submisson pdf, including others and history version The bug was patched at v3.2


Kubernetes Operators introduce Cross-Namespace Reference Vulnerabilities that can be exploited by attacker to breach Kubernetes namespace isolation. Our recent work systematically uncover this attack surface and got accepted in NDSS 2026. Preprint link: arxiv.org/pdf/2507.03387