𝕯𝖊𝖛𝕰𝖓𝖓𝖞
9K posts


𝕯𝖊𝖛𝕰𝖓𝖓𝖞
@ennycodes
CS • Student || Full Stack Developer
เข้าร่วม Temmuz 2023
990 กำลังติดตาม6.6K ผู้ติดตาม

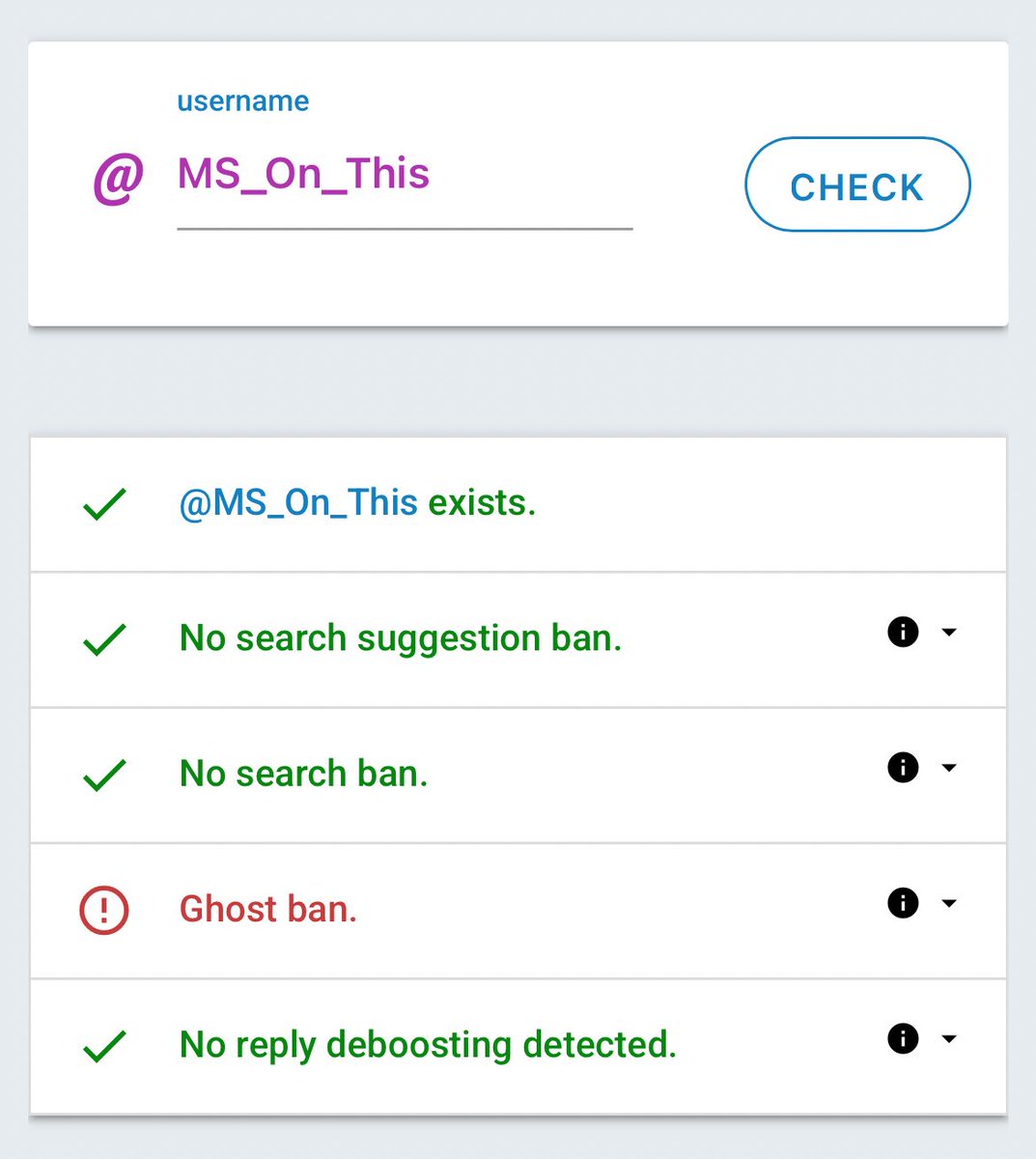
@ennycodes Not really a bug😂, bad ux but yeah let me fix that
Thanks boss
English

Noticed a bug just now. It I decide to click on a post to check the comments, then I go back to the main wall it goes back to the first post again having me to scroll down to the post I was before.
Other than that, it’s really good. Y’all should check it out 🌚 @stanlee0nX
Stanlee | Web developer@stanlee0nX
@ennycodes Use my app and tag me sire🙏🏾 de-boothe.vercel.app
English
𝕯𝖊𝖛𝕰𝖓𝖓𝖞 รีทวีตแล้ว

@ennycodes Use my app and tag me sire🙏🏾
de-boothe.vercel.app
English
𝕯𝖊𝖛𝕰𝖓𝖓𝖞 รีทวีตแล้ว

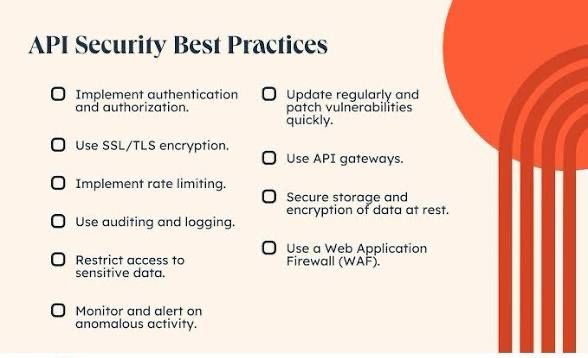
API Security Best Practices
API security refers to the practices and mechanisms used to protect APIs from unauthorized access, abuse, and data breaches.
It ensures only trusted users and systems can interact with backend services.
Secure APIs protect sensitive data and maintain system integrity.
Why API Security Is Important
- APIs expose backend services to external applications
- Poorly secured APIs can lead to data leaks and system compromise
- Many modern applications rely heavily on APIs for communication
- Protects user data, financial transactions, and business logic
Authentication and Authorization
- Always require authentication before granting API access
- Use strong authorization mechanisms to control user permissions
- Implement token-based authentication such as JWT
- Ensure role-based or permission-based access control
Use HTTPS for Encryption
- Encrypt all API communications using HTTPS
- Prevents attackers from intercepting sensitive data
- Protects login credentials, tokens, and user information
- Avoid transmitting sensitive data over unencrypted connections
Input Validation
- Validate all incoming data before processing it
- Prevent malicious inputs such as SQL injection or script injection
- Enforce strict data types and formats
- Reject unexpected or malformed requests
Rate Limiting and Throttling
- Limit the number of requests a client can send
- Prevent brute-force attacks and API abuse
- Protect backend resources from overload
- Example: limit requests per minute per user or IP
API Keys and Tokens
- Use API keys to identify applications accessing your API
- Rotate API keys periodically
- Store keys securely and avoid exposing them publicly
- Combine API keys with stronger authentication methods
Secure Error Handling
- Avoid exposing internal system details in error messages
- Do not reveal database queries or stack traces
- Return generic error messages to clients
- Log detailed errors internally for debugging
Implement Access Control
- Restrict access to sensitive endpoints
- Apply least-privilege access principles
- Ensure users only access resources they own or are permitted to use
Monitoring and Logging
- Log API activity for auditing and investigation
- Monitor unusual traffic patterns
- Detect suspicious behavior early
- Use monitoring tools to track request metrics and failures
API Versioning
- Maintain different versions of APIs when changes are made
- Prevent breaking existing client applications
- Secure deprecated versions before removing them
Protection Against Common Attacks
SQL Injection
- Sanitize inputs and use parameterized queries
Cross-Site Scripting (XSS)
- Validate and encode user-generated content
Denial of Service (DoS)
- Implement rate limiting and traffic filtering
Best Practices Summary
- Always authenticate and authorize API requests
- Encrypt communication using HTTPS
- Validate and sanitize all inputs
- Implement rate limiting and monitoring
- Protect API keys and tokens securely
- Log and analyze API usage patterns
Stay safe out there — secure APIs = secure apps!
English

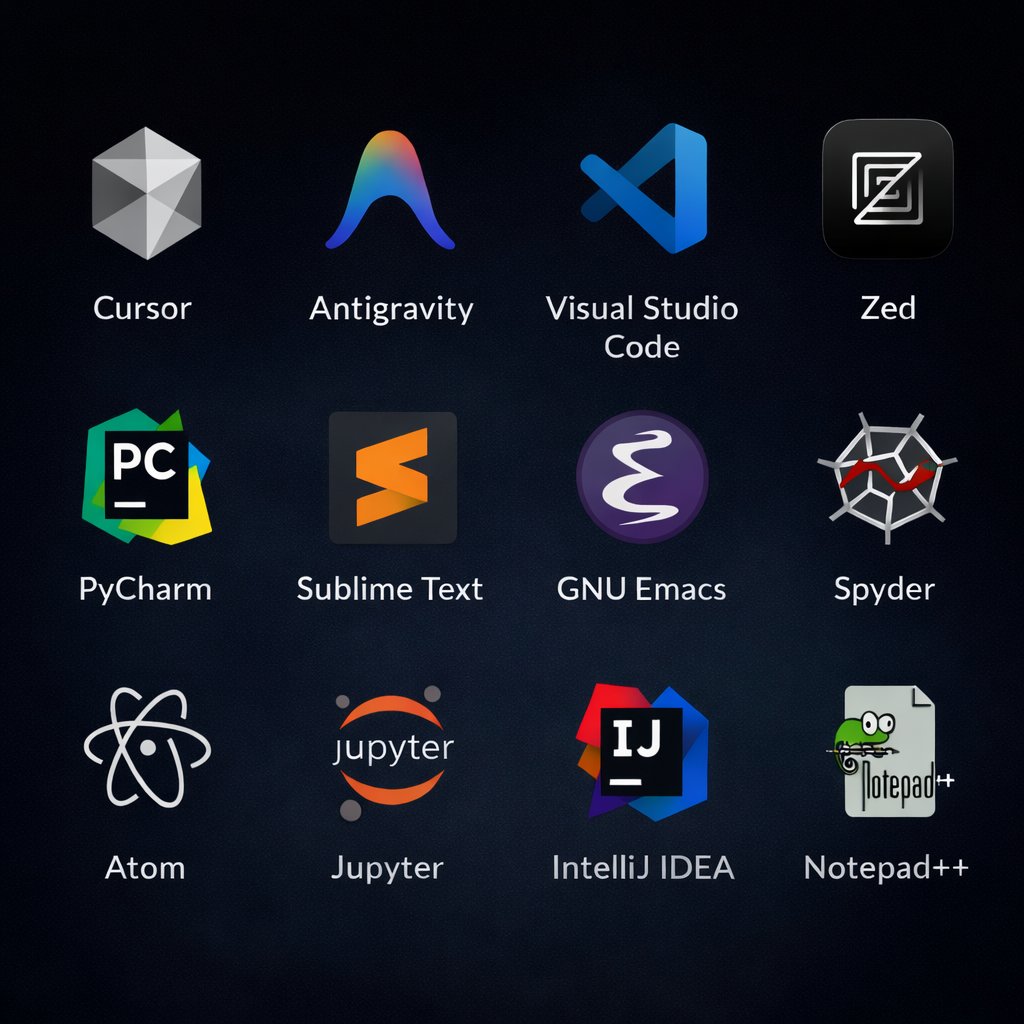
Your Tech Stack skills in 2026 should look like:
Languages & Core
- TypeScript
- Python
- Rust / Go
Frameworks & Backing
- Next.js / SvelteKit
- FastAPI / Node.js
- PostgreSQL / MongoDB
- Redis
- Drizzle ORM / Prisma
AI IDEs & Editors
- Cursor
- Windsurf IDE
- Zed
- Google Antigravity
Autonomous Coding Agents
- Claude Code
- Cline
- Aider
- OpenCode / Amp
Infra & Deployment
- Docker & Kubernetes
- Vercel AI
- AWS / Kuberns
AI Orchestration & Frameworks
- LangChain / LangGraph
- CrewAI
- Microsoft AutoGen
- Vellum AI
Vector Databases
- Pinecone
- Qdrant
- Milvus
English