Grégoire Clermont
439 posts
Grégoire Clermont
@gregclermont
building security at https://t.co/mBie3u14lP
France เข้าร่วม Nisan 2010
1.1K กำลังติดตาม559 ผู้ติดตาม
Grégoire Clermont รีทวีตแล้ว
Grégoire Clermont รีทวีตแล้ว
Grégoire Clermont รีทวีตแล้ว

CertCentral is now TheCertGraveyard[.]org & CertGraveyard[.]org.
The CertCentral API returns an error directing to use the new domains.
Please give me a like or a share to get the word out.
Also use the site to report and investigate certificates used to sign malware. :)
Squiblydoo@SquiblydooBlog
I'm being required to give up the domain CertCentral[.]org; and the change has to happen by Monday. I'm noodling on alternative names. Keep an eye out for the change.
English
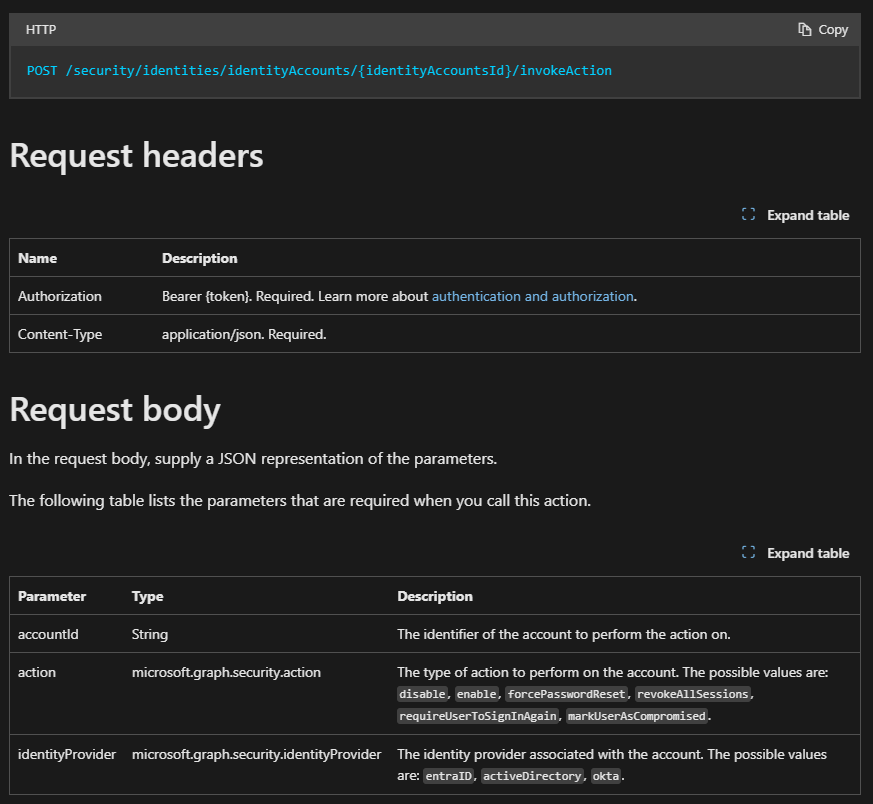
@IAMERICAbooted One vector that I'm still worried about is OAuth phishing with first-party Microsoft app (e.g. volexity.com/blog/2025/04/2…).
As almost all the CA checks are performed on the victim's side, I've found this technique hard to mitigate.
Do you have recommendations?
English

Do you know why I focused most of time on entra conditional access when I was consulting?
Because Jef Kazimer at Microsoft constantly reminded me what you can do with CAPs and how they mitigate almost all M365 initial access.
And he was right.
However, if you are allowing users to access M365 as BYOD (not phones, we are not talking about MAM-WE here) and you are not forcing authentication contexts requiring phishing resistant authentication that mitigates downgrades (hardly anyone), your CAPs alone will not save you from uploads, and neither will SharePoint settings.
There is the forgotten beast called Power Platform. In consulting, I have yet to see any orgs that dont have API gaps due to resource targeting in CAPs.
This is why you need exclude by exception and when you do exclude, you need to understand that exclusion is creating an API gap.
English
@ItsReallyNick Any chance Microsoft might officially document UserAuthenticationMethod at some point? I realize it's not your remit, but if this ever comes up in conversation with the right folks internally, there's definitely interest in the community!
English
@ItsReallyNick Thanks, Nick! Your tweets and GitHub comments were the only information I could find coming from a Microsoft employee (or anyone, really) about this field!
That definitely gave me some confidence that this bitfield interpretation was credible.
English
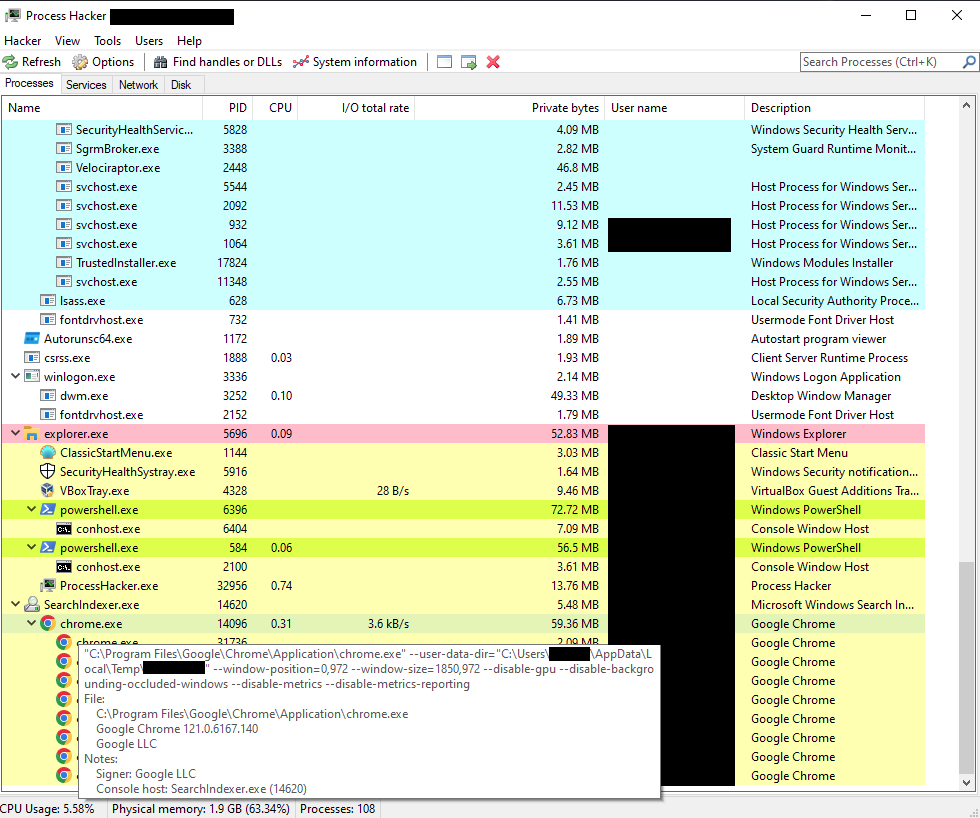
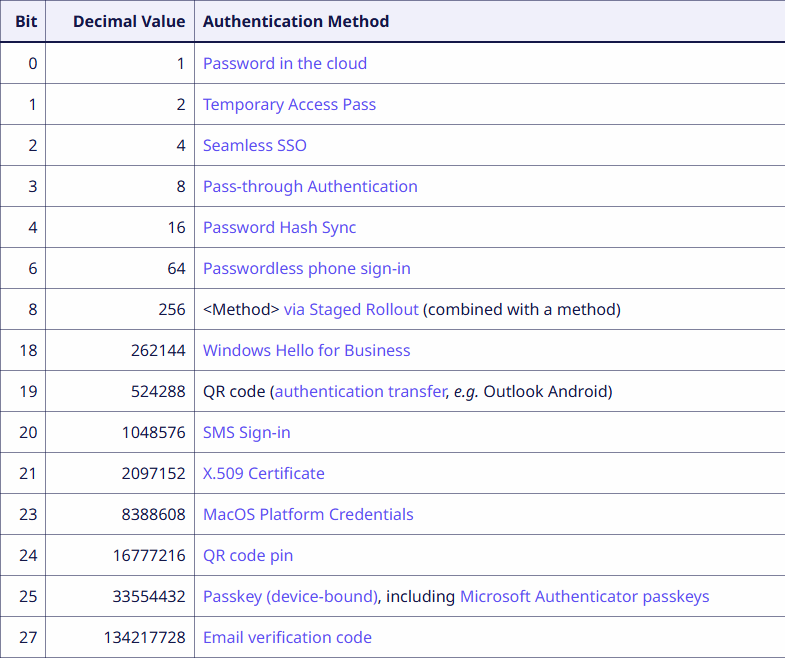
The #UserAuthenticationMethod field of the Microsoft 365 sign-in logs contains numeric values (16, 272, 33554432...) that were not documented anywhere.
I figured out that it's a bitfield, and recovered the meaning of most of the bits!
cryptopotato@cryptoishard
does everyone still know nothing about this? "UserAuthenticationMethod" is a black box
English
Grégoire Clermont รีทวีตแล้ว

Our latest technical deep-dive unravels the mystery behind the opaque numeric codes (16, 272, 33554432, etc.) you see in #Microsoft365 audit logs.
buff.ly/w04flj1
English
@sekoia_io UserAuthenticationMethod 16457, of SolarWinds fame (and that doesn't seem to exist anymore) remains a bit of a mystery to me.
I'm not sure if it could be decoded in the same way (bits 0, 3, 6, 14?)
x.com/ItsReallyNick/…
Nick Carr@ItsReallyNick
@reprise_99 this was a weird one until it was removed from UAL in late 2020 “Fixed the glitch” 😂
English
The results and methodology are detailed on the @sekoia_io blog:
blog.sekoia.io/userauthentica…
Several bits remain unmapped (bits 5, 7, 9-17, 22, 26). If you observe these values, please share your findings!
English
@ZackKorman I have a pet theory that the reason why Kusto got so versatile and powerful is because the Entra/Azure/M365 logs are so convoluted and impractical.
Instead of fixing the logs, they built a crazy query language.
English
Grégoire Clermont รีทวีตแล้ว

"Uncovering the Chinese Proxy Service Used in APT Campaigns" published by Spur. #Kimsuky, #DPRK, #CTI spur.us/how-spur-uncov…
English
Grégoire Clermont รีทวีตแล้ว
Grégoire Clermont รีทวีตแล้ว
Hey everyone, I’m proud to announce that I'm hosting a new conference called State of Statecraft (🆘) October 28 in Brussels, Belgium. SOS exclusively discusses state-sponsored operations.
Speakers! Our CFP closes in 2 weeks!!! -> Apply here: stateofstatecraft.com/cfp

English
Grégoire Clermont รีทวีตแล้ว
New RE Blog Post: RustyPages-Pt1
the-sequence.com/rustypages-mal…
We RE a Rust dropper, that sets persistence and runs the downloaded next stage, queries @patrickwardle's tools, and quiets notifications. We included relevant IOCs as we continue our analysis of the loader for Part 2. :)
English
Grégoire Clermont รีทวีตแล้ว

⚠️ Threat hunting and detection engineering using time series anomaly detection methods is so powerful but quite tricky.
Here is why:
- Users/endpoints don't have a reliable baseline
- First seen activities don't fit time series anomaly logic by default (with some modifications, it can)
- Compute resources limit the historical data that can be analyzed, which directly impacts what the logic outputs with default parameters.
That's why I have multiple lessons to explain how to develop robust detection logic.
#ThreatHunting #DetectionEngineering

English
Grégoire Clermont รีทวีตแล้ว
Grégoire Clermont รีทวีตแล้ว

Aaand we (or mostly Fabian) made this cool website where you can explore all these first party apps and their scopes at entrascopes.com x.com/fabian_bader/s…
Fabian Bader@fabian_bader
One of the results of the joined research with @_dirkjan is entrascopes.com Basically the yellow pages for Microsoft first party apps. #TROOPERS25
English