Come join me for my fast-paced, two-day, hands-on training that takes a deep dive into anti-forensics techniques. The course is divided not only into operating systems but also into red/blue perspectives.
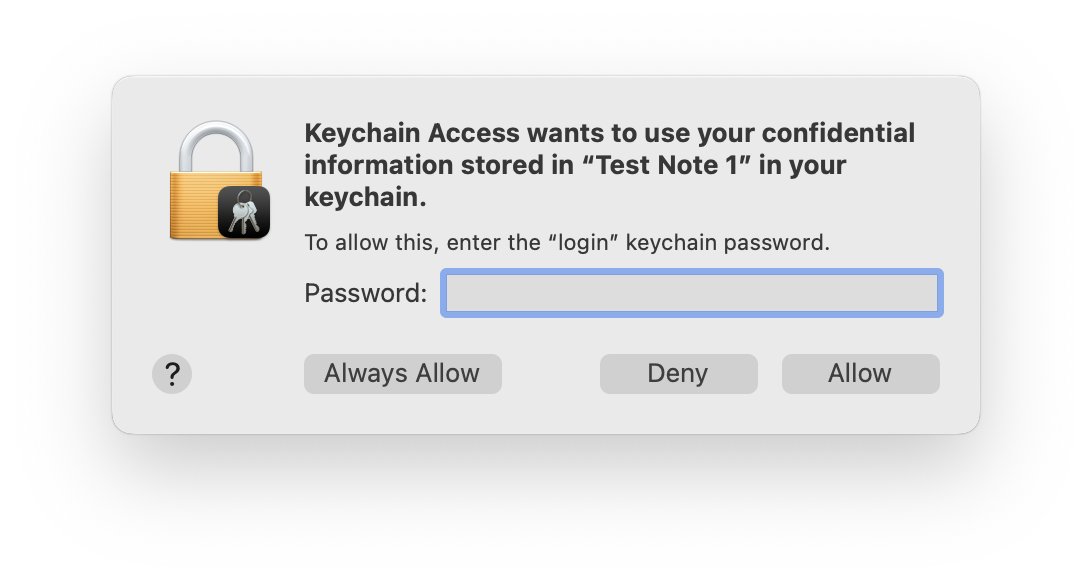
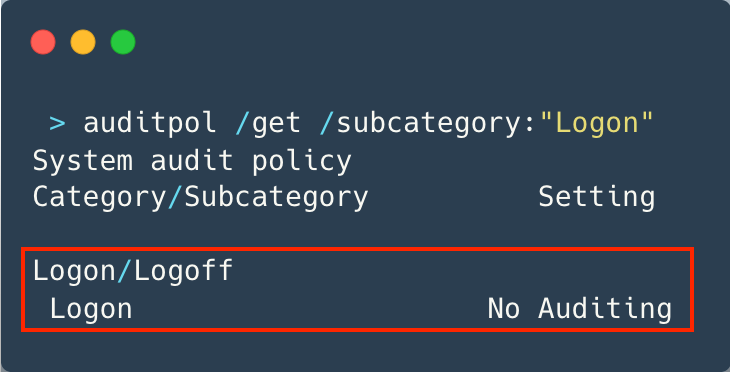
On the one hand, we will learn how adversaries are trying to cover their tracks, which might also be of interest to red teamers. On the other hand, we will teach various methods to circumvent or work around these anti-forensics techniques.🤘
Due to various requests, I will also have a section on Linux Rootkits ready, depending on time and the class's interest. Or just be prepared for a late-night session on the second day 🙃 Looking forward to welcoming some of you in my classroom 🤓
PS: My DMs are open if anyone wants a sneak peek at the content and slides to help them decide whether to register for the training.
More information and registration here: brucon.org/training-detai…
English