Chaplin
72 posts








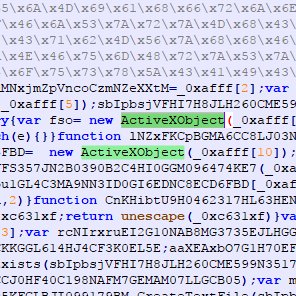
A game called PirateFi released on Steam last week and it contained malware. Valve have removed the game two days ago. Users that played the game have received the following email:




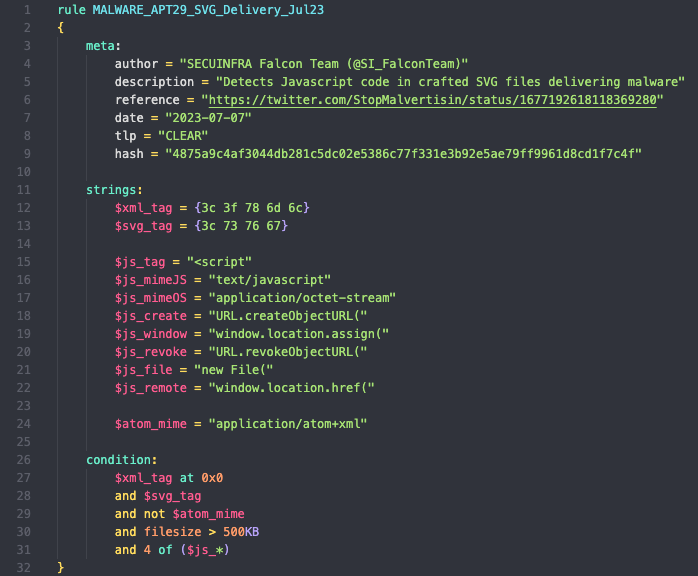
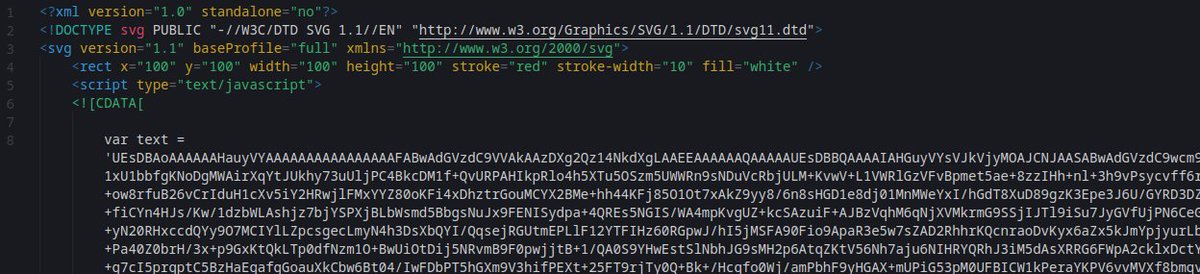
Interesting #APT29 document uploaded to VT yesterday. Invitation - Santa Lucia Celebration.msg f29083f25d876bbc245a1f977169f8c2 The email itself is from June 23 2023 and contains an .SVG attachement which drops an .ISO image called "invitation.iso"

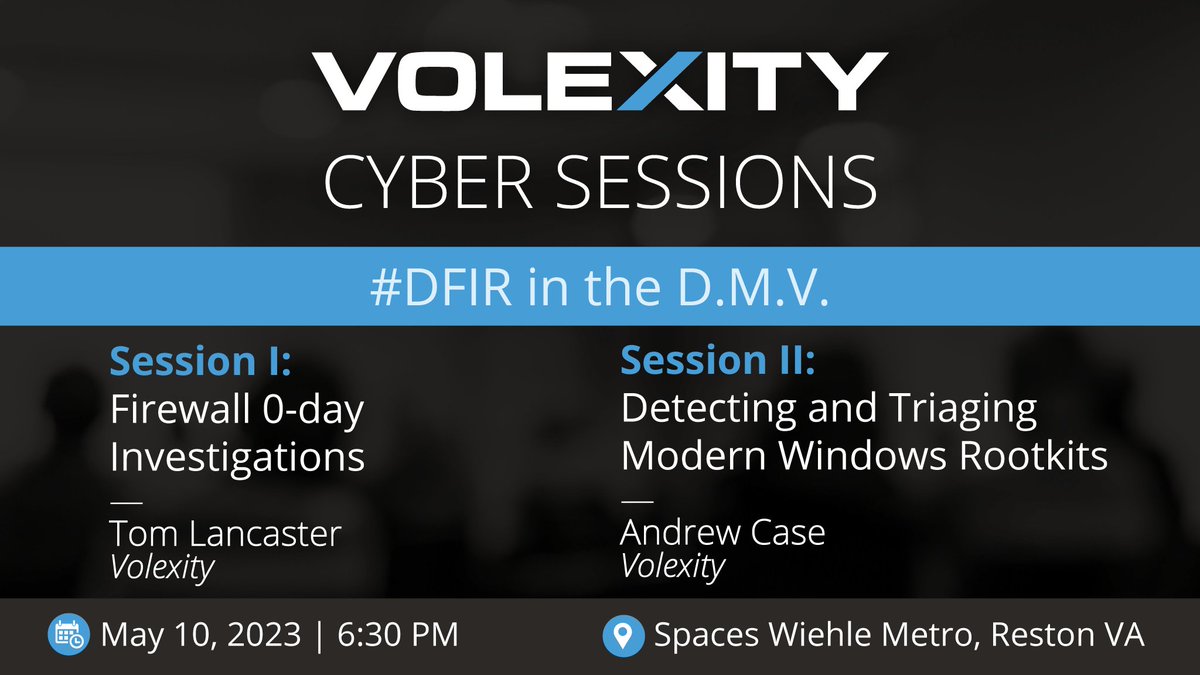




#Magniber #Ransomware is continuing to spread fake Windows Update installers (.msi), but since yesterday the threat actors are also distributing .iso archives instead of .zip files. You can find our brief analysis of the msi and the lnk file below ⬇️ 1/3🧵









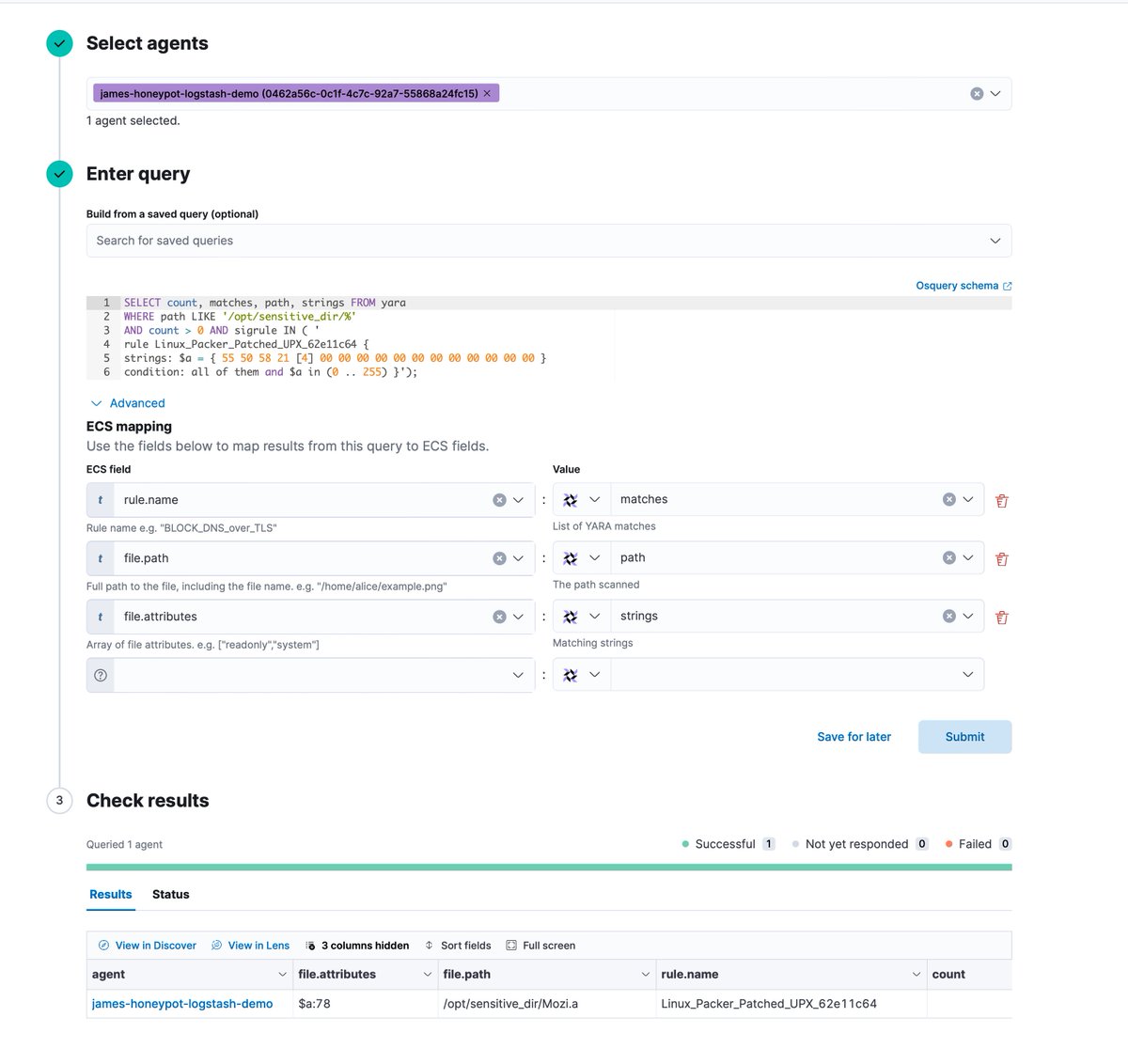
Not sure if this got enough love when it was announced, but you should 100% sign up to the free Azure Data Explorer instance - aka.ms/kustofree. 100 GB of storage, load up whatever data you want (csv, json, txt) and go ham with it